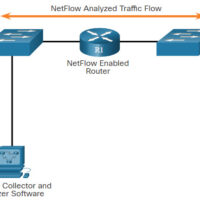
15.0 Introduction 15.0.1 Why Should I Take this Module? Since all networks are under attack, it is important for you to understand network monitoring and network monitoring tools to help you defend and protect the network. Read more to learn about these methods and tools! 15.0.2 What Will …
14.0 Introduction 14.0.1 Why Should I Take this Module? By now you know why our networks are attacked. In this module you will learn about common threats and attacks. 14.0.2 What Will I Learn in this Module? Module Title: Common Threats and Attacks Module Objective: Explain the various …
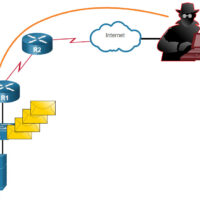
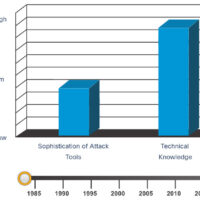
13.0 Introduction 13.0.1 Why Should I Take this Module? Who is attacking our network and why? In this module you will learn about white hats, grey hats, and black hats. You will also learn about the techniques and tools used by these “hackers”. Keep reading to learn more! …
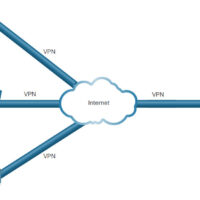
12.0 Introduction 12.0.1 Why Should I Take this Module? With the many threats to network security, how can networks be designed to protect data resources and ensure that network services are provided as required? The network security infrastructure defines the way in which devices are connected together to …
11.0 Introduction 11.0.1 Why Should I Take this Module? The network infrastructure defines the way in which devices are connected together to achieve end-to-end communications. Just as there are many sizes of networks, there are also many ways to build an infrastructure. However, there are some standard designs …
10.0 Introduction 10.0.1 Why Should I Take this Module? In this module you will learn about network services including DHCP, NAT, PAT, FTP, TFTP, email protocols, and DNS. A recent analysis of network security threats discovered that over 90% of the malicious software that is used to attack …
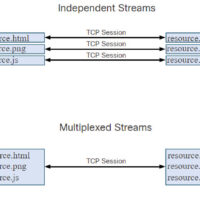
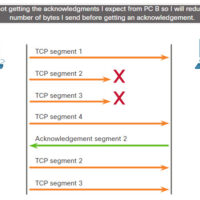
9.0 Introduction 9.0.1 Why Should I Take this Module? Welcome to Transport Layer! The transport layer is where, as the name implies, data is transported from one host to another. This is where your network really gets moving! The transport layer uses two protocols: TCP and UDP. Think …
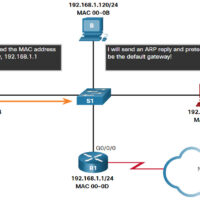
8.0 Introduction 8.0.1 Why Should I Take this module? Did you ever wonder how information that you send gets delivered to the correct device? This module will explain how the combination of a logical address and a physical address enable communication between two hosts. You will learn how …
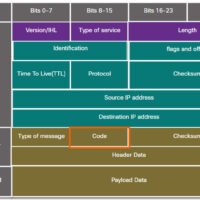
7.0 Introduction 7.0.1 Why Should I Take this Module? Do networks ever break? Of course they do. Fortunately, the developers of the IP protocols included a testing protocol called ICMP. ICMP tools create special packets that test networks. Cybersecurity analysts must understand the network that normal data travels …
6.0 Introduction 6.0.1 Why Should I Take this Module? How do devices know how to send and receive information within the network, and from the vast internet? Every piece of data that is sent requires addresses; addresses for destinations, and addresses for the return of information to the …