Instructor Planning Guide
Activities
What activities are associated with this chapter?
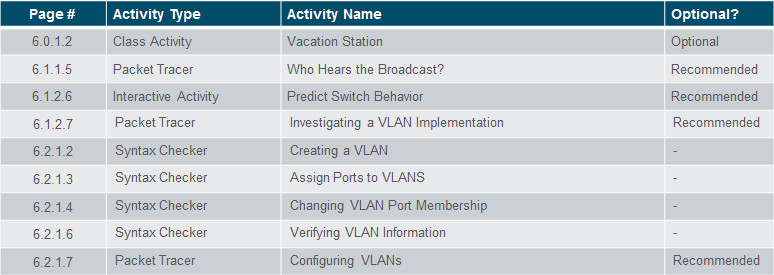
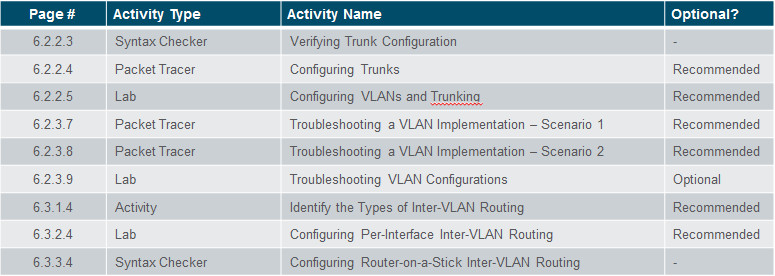
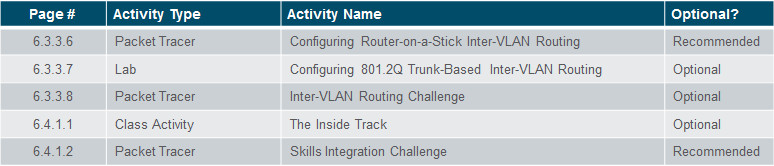
Assessment
Students should complete Chapter 6, “Assessment” after completing Chapter 6.
Quizzes, labs, Packet Tracers and other activities can be used to informally assess student progress.
Sections & Objectives
6.1 VLAN Segmentation
Explain the purpose of VLANs in a switched network.
Explain how a switch forwards frames based on VLAN configuration in a multi-switch environment.
6.2 VLAN Implementations
Configure a switch port to be assigned to a VLAN based on requirements.
Configure a trunk port on a LAN switch.
Troubleshoot VLAN and trunk configurations in a switched network.
6.3 Inter-VLAN Routing Using Routers
Describe the two options for configuring Inter-VLAN routing.
Configure legacy Inter-VLAN Routing.
Configure Router-on-a-Stick Inter-VLAN Routing
Chapter 6: VLANs
6.1 – VLAN Segmentation
6.1.1 – Overview of VLANs
6.1.1.1 – VLAN Definitions
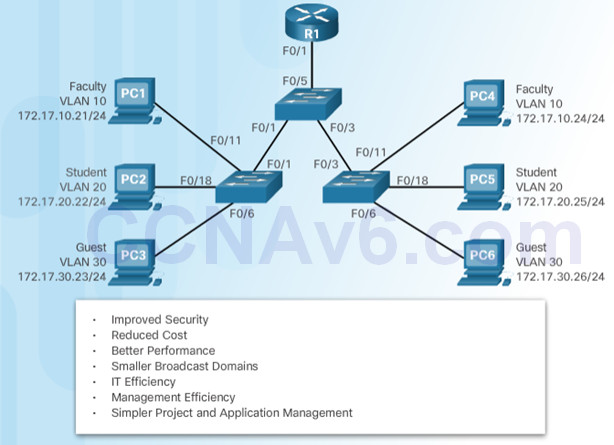
VLANs can segment LAN devices without regard for the physical location of the user or device.
- In the figure, IT users on the first, second, and third floors are all on the same LAN segment. The same is true for HR and Sales users.
A VLAN is a logical partition of a Layer 2 network.
- Multiple partitions can be created and multiple VLANs can co-exist.
- The partitioning of the Layer 2 network takes place inside a Layer 2 device, usually via a switch.
- Each VLAN is a broadcast domain that can span multiple physical LAN segments.
- Hosts on the same VLAN are unaware of the VLAN’s existence.

VLANs are mutually isolated and packets can only pass between VLANs via a router.
6.1.1.2 – Benefits of VLANs
6.1.1.3 – Types of VLANs
Common types of VLANs:
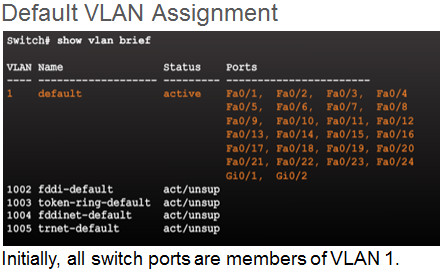
- Default VLAN – Also known as VLAN 1. All switch ports are members of VLAN 1 by default.
- Data VLAN – Data VLANs are commonly created for specific groups of users or devices. They carry user generated traffic.
- Native VLAN – This is the VLAN that carries all untagged traffic. This is traffic that does not originate from a VLAN port (e.g., STP BPDU traffic exchanged between STP enabled switches). The native VLAN is VLAN 1 by default.
- Management VLAN – This is a VLAN that is created to carry network management traffic including SSH, SNMP, Syslog, and more. VLAN 1 is the default VLAN used for network management.
6.1.1.4 – Voice VLANs
To support time-sensitive voice traffic, Cisco switches support a voice VLAN that requires:
- Assured bandwidth
- Delay of less than 150 ms across the network to ensure voice quality
- Transmission priority over other types of network traffic
- Ability to be routed around congested areas on the network.
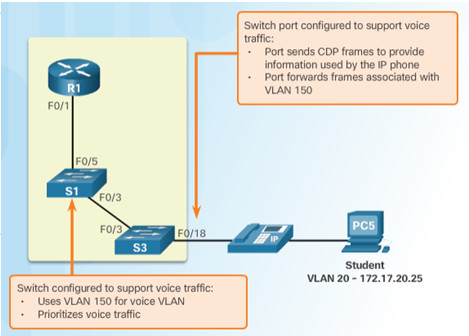
The voice VLAN feature enables access ports to carry user and IP voice traffic.
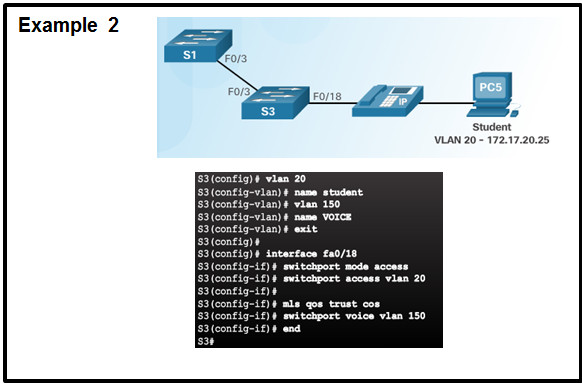
- In the figure, the S3 F0/18 interface has been configured to tag student traffic on VLAN 20 and voice traffic on VLAN 150.
6.1.1.5 – Packet Tracer – Who Hears the Broadcast?
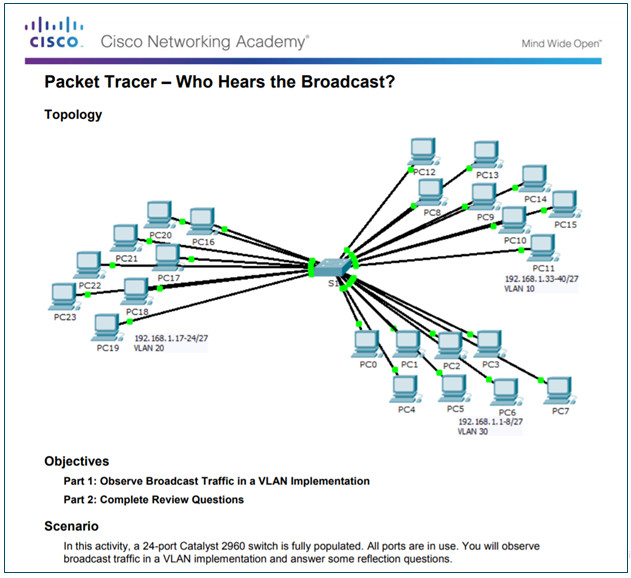
6.1.1.5 Packet Tracer – Who Hears the Broadcast
6.1.2 – VLANs in a Multi-Switched Environment
6.1.2.1 – VLAN Trunks
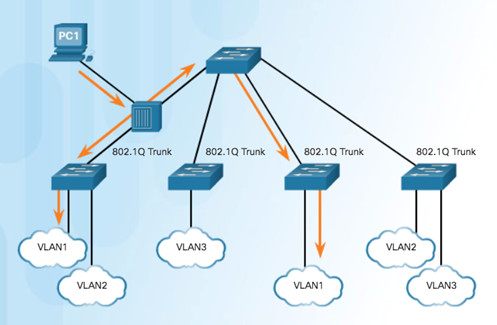
A VLAN trunk is a point-to-point link that carries more than one VLAN.
- Usually established between switches to support intra VLAN communication.
- A VLAN trunk or trunk ports are not associated to any VLANs.
Cisco IOS supports IEEE 802.1q, a popular VLAN trunk protocol.
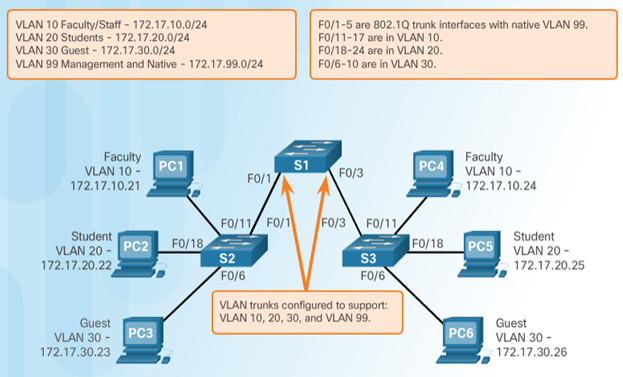
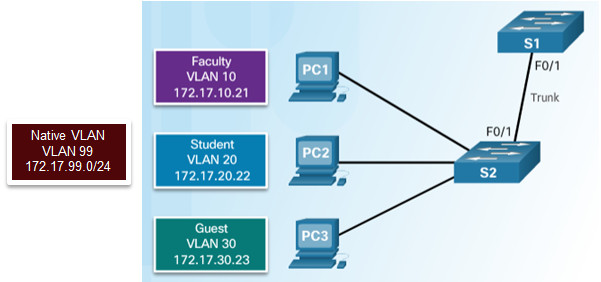
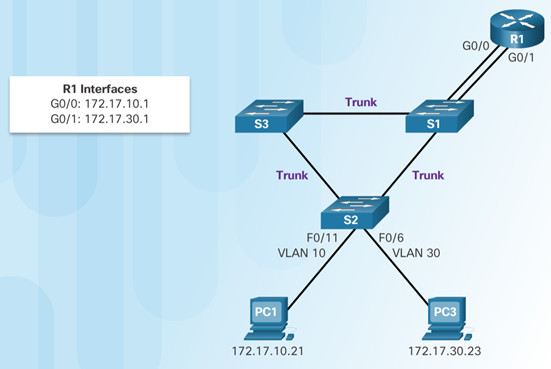
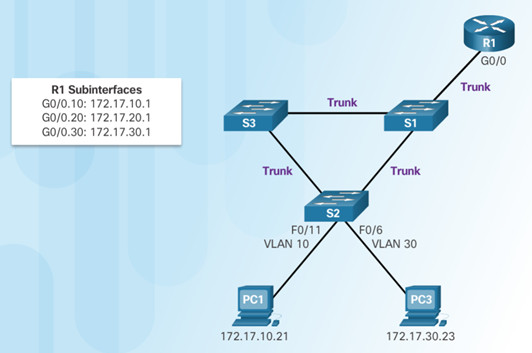
The links between switches S1 and S2, and S1 and S3 are configured to transmit traffic coming from VLANs 10, 20, 30, and 99 across the network.
6.1.2.2 – Controlling Broadcast Domains with VLANs
If a switch port receives a broadcast frame, it forwards it out all ports except the originating port.
- Eventually the entire network receives the broadcast because the network is one broadcast domain.
VLANs can be used to limit the reach of broadcast frames because each VLAN is a broadcast domain.
- VLANs help control the reach of broadcast frames and their impact in the network.
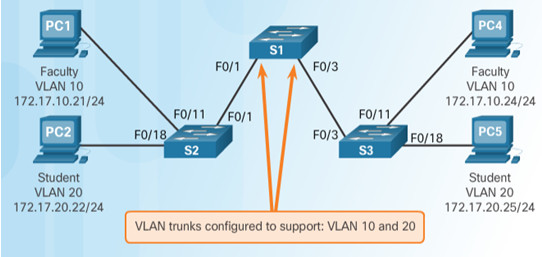
In the figure, PC1 on VLAN 10 sends a broadcast frame.
- Trunk links between S2 – S1 and S1 – S3 propagate the broadcast to other devices in VLAN 10.
- Only devices in the same VLAN receive the broadcast therefore, PC4 would receive the broadcast.
6.1.2.3 – Tagging Ethernet Frames for VLAN Identification
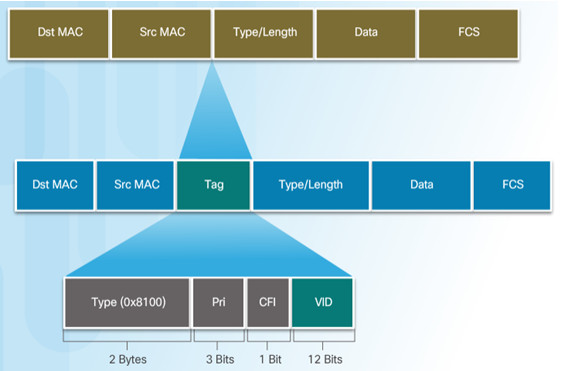
Before a frame is forwarded across a trunk link, it must be tagged with its VLAN information.
- Frame tagging is the process of adding a VLAN identification header to the frame.
- It is used to properly transmit multiple VLAN frames through a trunk link.
IEEE 802.1Q is a vey popular VLAN trunking protocol that defines the structure of the tagging header added to the frame.
- Switches add VLAN tagging information after the Source MAC address field.
- The fields in the 802.1Q VLAN tag includes VLAN ID (VID).
- Trunk links add the tag information before sending the frame and then remove the tags before forwarding frames through non-trunk ports.
6.1.2.4 – Native VLANs and 802.1Q Tagging
Control traffic sent on the native VLAN should not be tagged.
Frames received untagged, remain untagged and are placed in the native VLAN when forwarded.
If there are no ports associated to the native VLAN and no other trunk links, an untagged frame is dropped.
When configuring a switch port on a Cisco switch, configure devices so that they do not send tagged frames on the native VLAN.
In Cisco switches, the native VLAN is VLAN 1, by default.
6.1.2.5 – Voice VLAN Tagging
An access port connecting a Cisco IP phone can be configured to use two separate VLANs:
- A VLAN for voice traffic
- A VLAN for data traffic from a device attached to the phone.
The link between the switch and the IP phone behaves like a trunk to carry traffic from both VLANs.
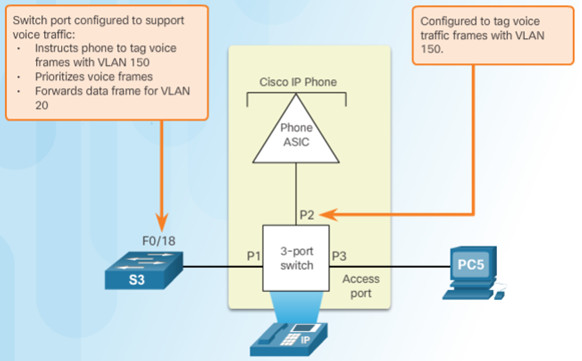
Cisco IP Phone contains an integrated three-port 10/100 switch dedicated to these devices:
- Port 1 connects to the switch or other VoIP device.
- Port 2 is an internal 10/100 interface that carries the IP phone traffic.
- Port 3 (access port) connects to a PC or other device.
6.1.2.7 – Packet Tracer – Investigating a VLAN Implementation
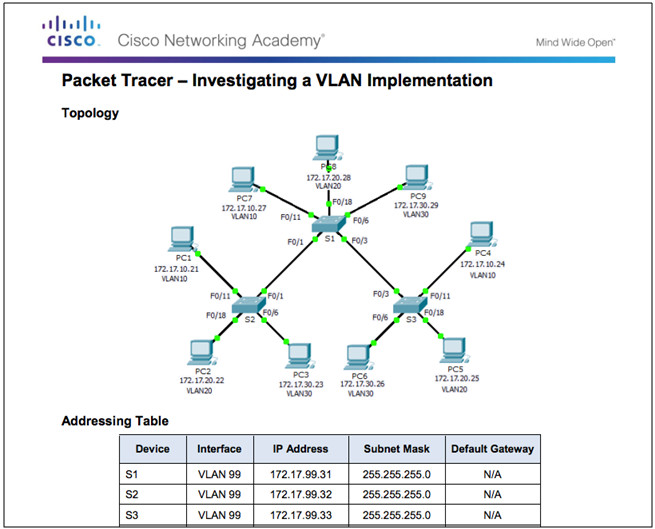
6.1.2.7 Packet Tracer – Investigating a VLAN Implementation
6.2 – VLAN Implementations
6.2.1 – VLAN Assignment
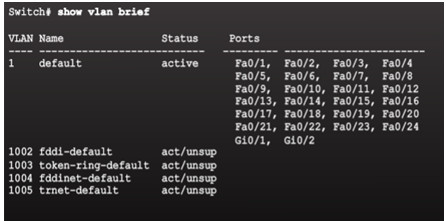
6.2.1.1 – VLAN Ranges on Catalyst Switches
VLANs are split into two categories:
Normal range VLANs
- VLAN numbers from 1 to 1,005
- Configurations stored in the vlan.dat (in the flash memory)
- IDs 1002 through 1005 are reserved for legacy Token Ring and Fiber Distributed Data Interface (FDDI) VLANs, automatically created and cannot be removed.
Extended Range VLANs
- VLAN numbers from 1,006 to 4,096
- Configurations stored in the running configuration (NVRAM)
- VLAN Trunking Protocol (VTP) does not learn extended VLANs
Cisco Catalyst 2960 and 3560 Series switches support over 4,000 VLANs.
6.2.1.2 – Creating a VLAN
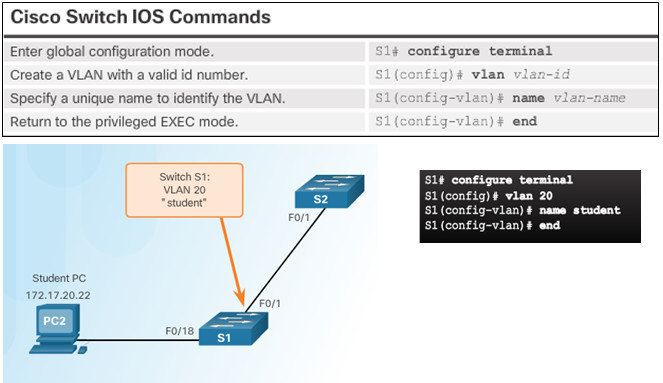
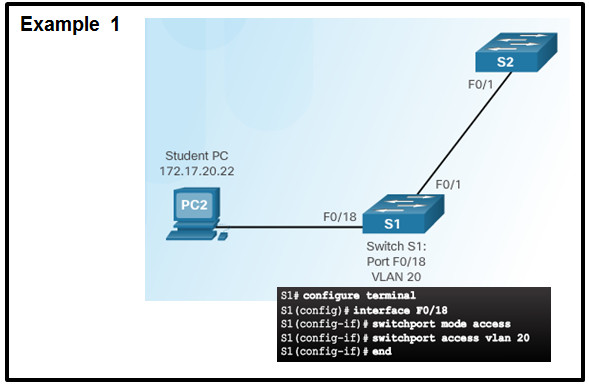
6.2.1.3 – Assigning Ports to VLANs
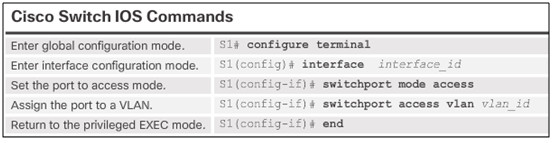
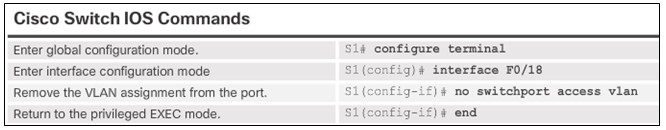
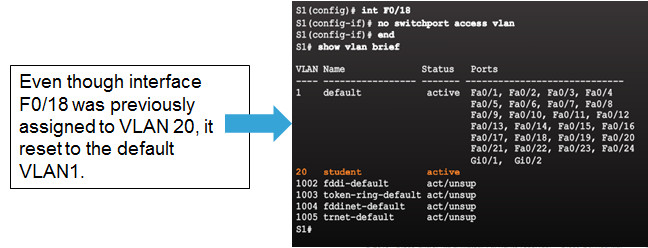
6.2.1.4 – Changing VLAN Port Membership
Remove VLAN Assignment
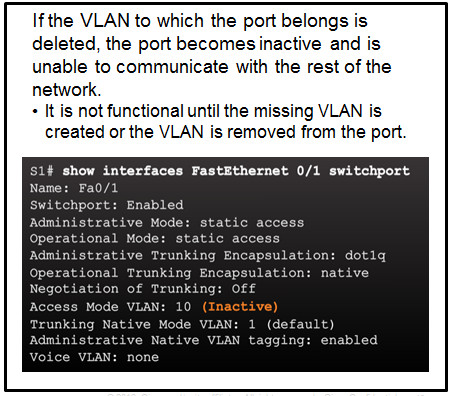
6.2.1.5 – Deleting VLANs
Use the no vlan vlan-id global configuration mode command to remove VLAN.
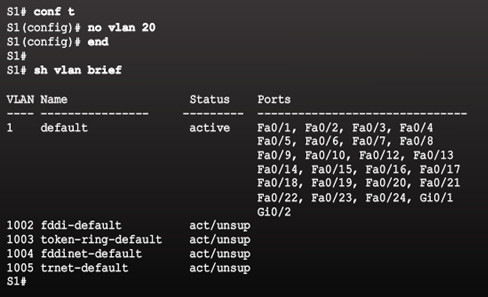
To delete the entire vlan.dat file, use the delete flash:vlan.dat privileged EXEC mode command.
- delete vlan.datcan be used if the vlan.dat file has not been moved from its default location.
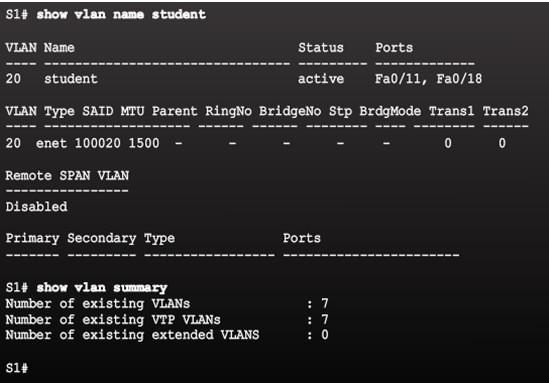
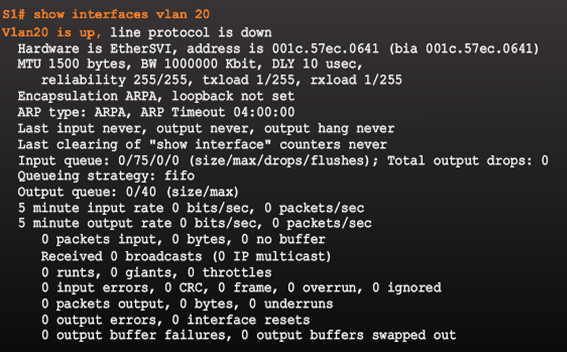
6.2.1.6 – Verifying VLAN Information
VLAN configurations can be validated using the Cisco IOS show vlan and show interfaces command options.
6.2.1.7 – Packet Tracer – Configuring VLANs
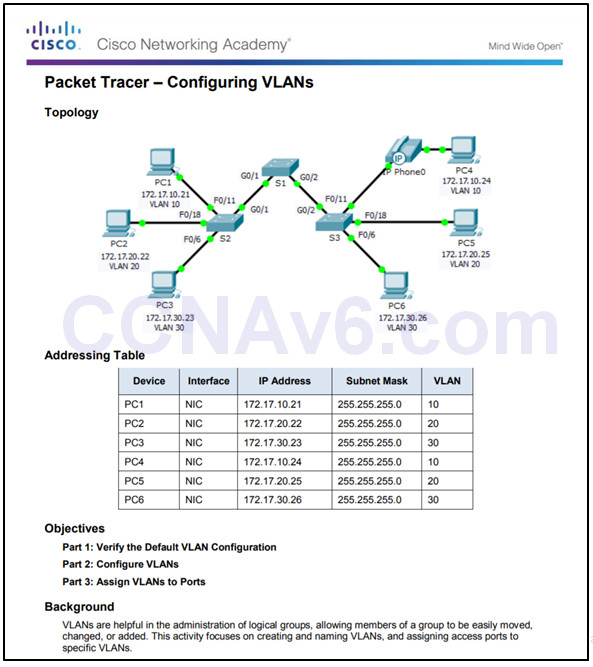
6.2.1.7 Packet Tracer – Configuring VLANs
6.2.2 – VLAN Trunks
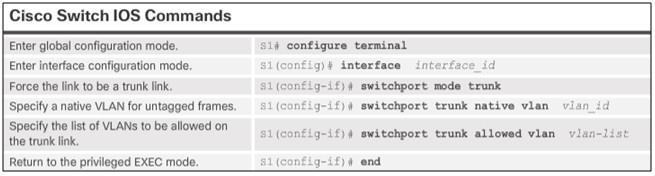
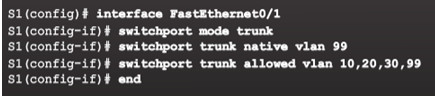
6.2.2.1 – Configuring IEEE 802.1q Trunk Links
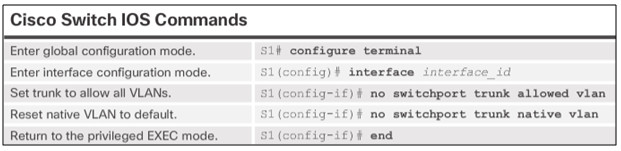
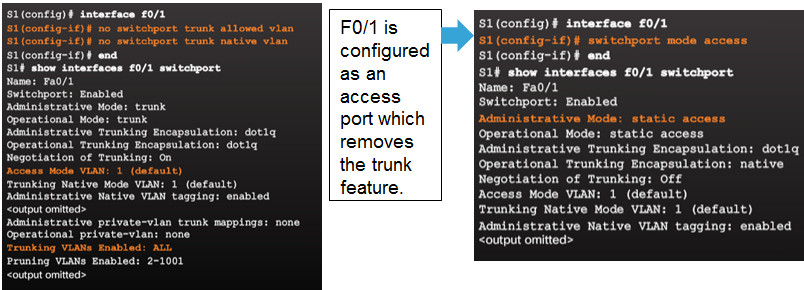
6.2.2.2 – Resetting the Trunk to Default State
6.2.2.3 – Verifying Trunk Configuration
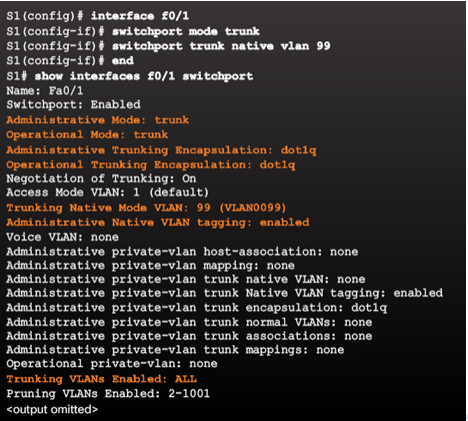
6.2.2.4 – Packet Tracer – Configuring Trunks
6.2.2.4 Packet Tracer – Configuring Trunks
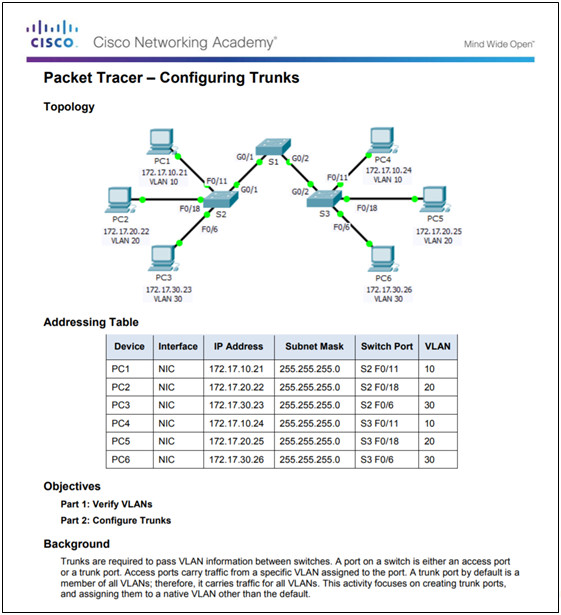
6.2.2.5 – Lab – Configuring VLANs and Trunks
6.2.2.5 Lab – Configuring VLANs and Trunking
6.2.3 – Troubleshoot VLANs and Trunks
6.2.3.1 – IP Addressing Issues with VLANs
Common practice to associate a VLAN with an IP network.
- Different IP networks must communicate through a router.
- All devices within a VLAN must be part of the same IP network to communicate.
In the figure, PC1 cannot communicate to the server because it has a wrong IP address configured.
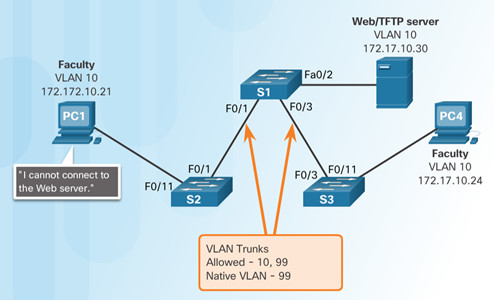
6.2.3.2 – Missing VLANs
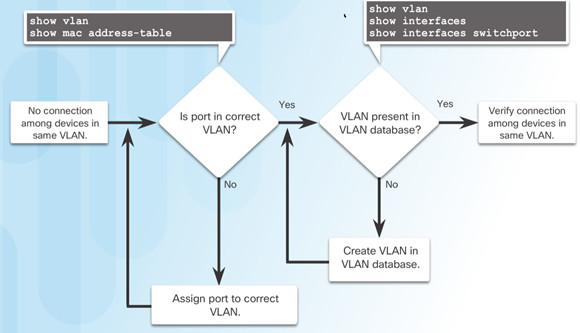
If all the IP address mismatches have been solved, but the device still cannot connect, check if the VLAN exists in the switch.
6.2.3.3 – Introduction to Troubleshooting Trunks
6.2.3.4 – Common Problems with Trunks
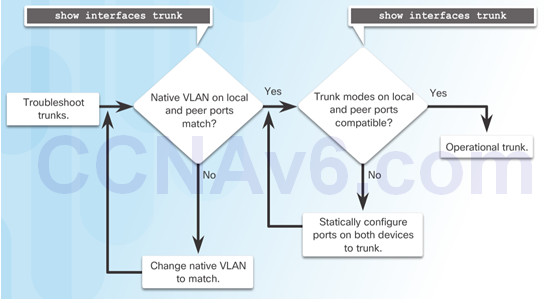
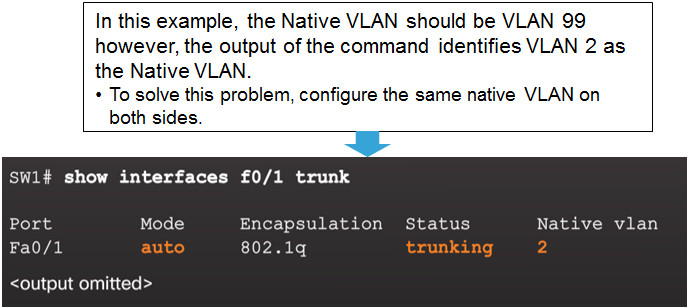
Trunking issues are usually associated with incorrect configurations.
The most common type of trunk configuration errors are:
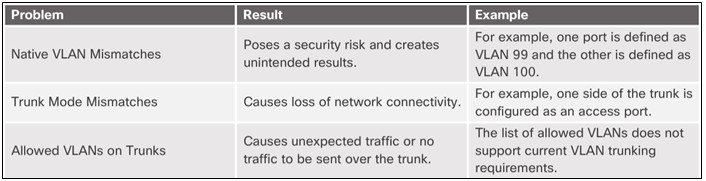
When a trunk problem is suspected, it is recommended to troubleshoot in the order shown above.
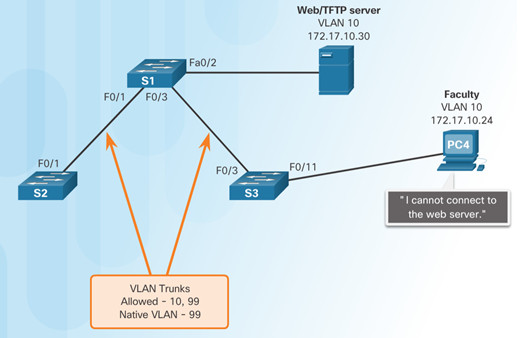
6.2.3.5 – Incorrect Port Mode
In this example, PC4 cannot reach the Web server.
- The trunk links on S1 and S3 are verified and reveal that the S3 trunk port has been configured as an access port.
6.2.3.6 – Incorrect VLAN List
In this example, PC5 cannot reach the Student Email server.
- The output of the switchport trunk allowed vlan command reveals S1 is not allowing VLAN 20.
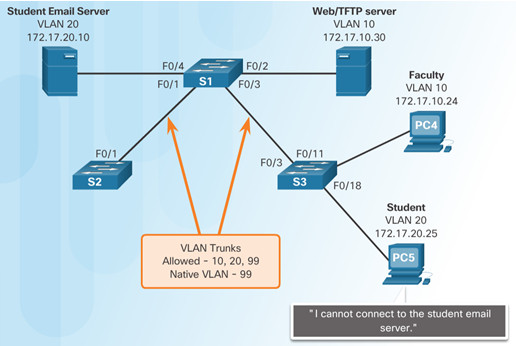
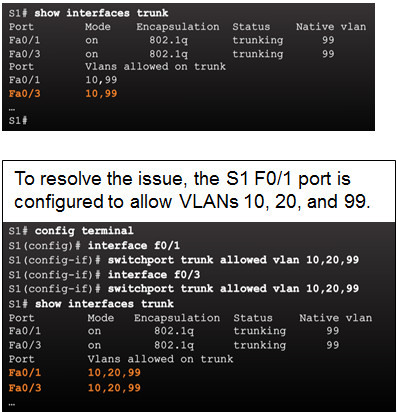
6.2.3.7 – Packet Tracer – Troubleshooting a VLAN Implementation – Scenario 1
6.2.3.7 Packet Tracer – Troubleshooting a VLAN Implementation – Scenario 1
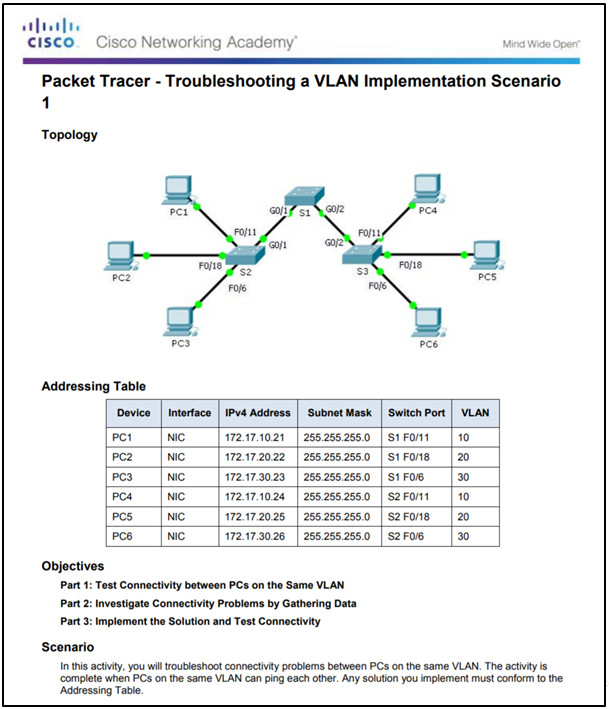
6.2.3.8 – Packet Tracer – Troubleshooting a VLAN Implementation – Scenario 2
6.2.3.8 Packet Tracer – Troubleshooting a VLAN Implementation – Scenario 2
6.2.3.9 – Lab – Troubleshooting VLAN Configurations
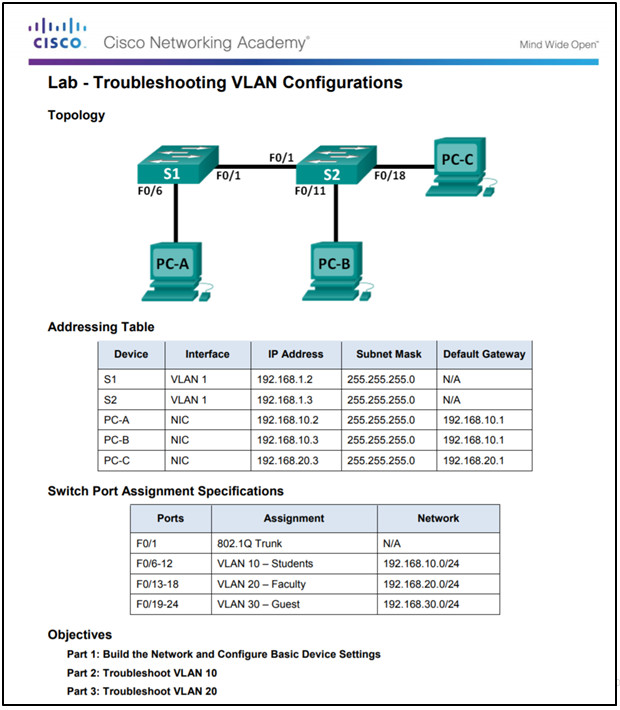
6.2.3.9 Lab – Troubleshooting VLAN Configurations
6.3 – Inter-VLAN Routing Using Routers
6.3.1 – Inter-VLAN Routing Operation
6.3.1.1 – What is Inter-VLAN Routing?
Layer 2 switches cannot forward traffic between VLANs without the assistance of a router.
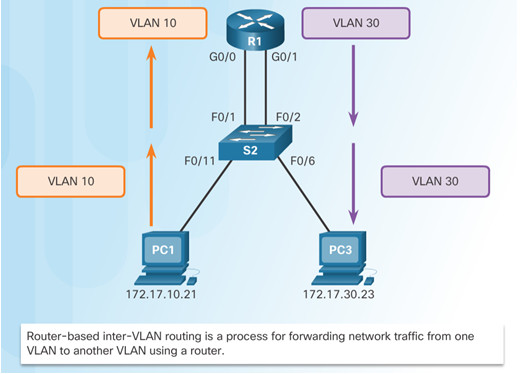
Inter-VLAN routing is a process for forwarding network traffic from one VLAN to another, using a router.
There are three options for inter-VLAN routing:
- Legacy inter-VLAN routing
- Router-on-a-Stick
- Layer 3 switching using SVIs
6.3.1.2 – Legacy Inter-VLAN Routing
In the past:
- Router interfaces were used to route between VLANs.
- Each VLAN was connected to a different physical router interface.
- Packets would arrive on the router through one interface, be routed and leave through another.
- Because the router interfaces were connected to VLANs and had IP addresses from that specific VLAN, routing between VLANs was achieved.
- Large networks with large number of VLANs required many router interfaces.
In this example, the router was configured with two separate physical interfaces to interact with the different VLANs and perform the routing.
6.3.1.3 – Router-on-a-Stick Inter-VLAN Routing
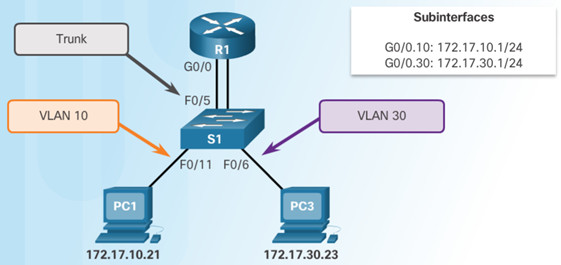
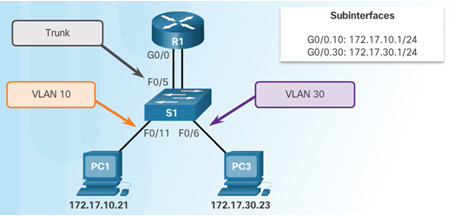
The router-on-a-stick approach uses only one of the router’s physical interface.
- One of the router’s physical interfaces is configured as a 802.1Q trunk port so it can understand VLAN tags.
- Logical subinterfaces are created; one subinterface per VLAN.
- Each subinterface is configured with an IP address from the VLAN it represents.
- VLAN members (hosts) are configured to use the subinterface address as a default gateway.
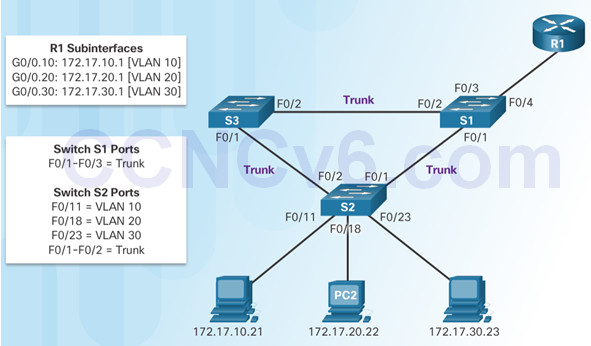
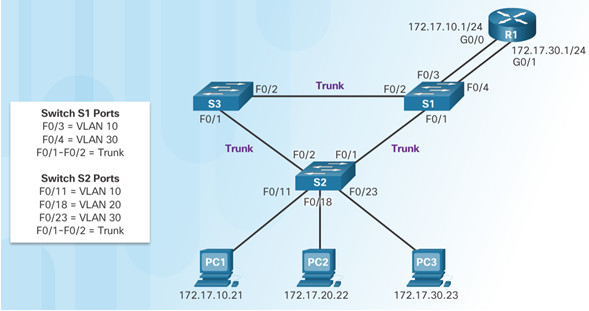
In this example, the R1 interface is configured as a trunk link and connects to the trunk F0/4 port on S1.
- Router accepts VLAN-tagged traffic on the trunk interface
- Router internally routes between the VLANs using subinterfaces.
- Router then forwards the routed traffic as VLAN-tagged for the destination VLAN out the trunk link.
6.3.2 – Configure Legacy Inter-VLAN Routing
6.3.2.1 – Configure Legacy Inter-VLAN Routing: Preparation
Legacy inter-VLAN routing requires routers to have multiple physical interfaces.
Each one of the router’s physical interfaces is connected to a unique VLAN.
Each interface is also configured with an IP address for the subnet associated with the particular VLAN.
Network devices use the router as a gateway to access the devices connected to the other VLANs.
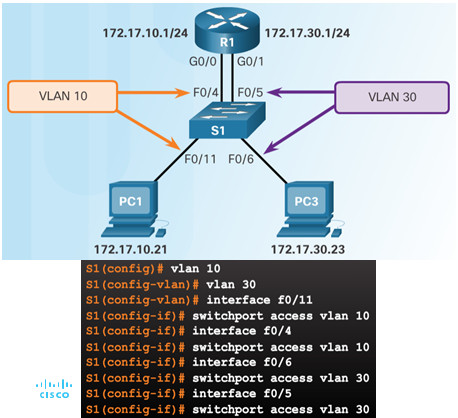
6.3.2.2 – Configure Legacy Inter-VLAN Routing: Switch Configuration
Configure the VLANs on the switch and then assign the ports to their respective VLANs.
In this example, the S1 ports are configured as follows:
- Ports F0/4 and F0/11 of S1 are on VLAN 10
- Ports F0/5 and F0/16 ports are on VLAN 30.
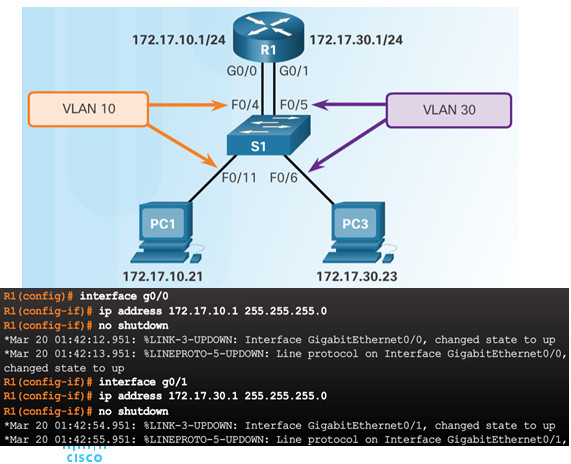
6.3.2.3 – Configure Legacy Inter-VLAN Routing: Router Interface Configuration
Next configure the router interfaces.
6.3.2.4 – Lab – Configuring Per-Interface Inter-VLAN Routing
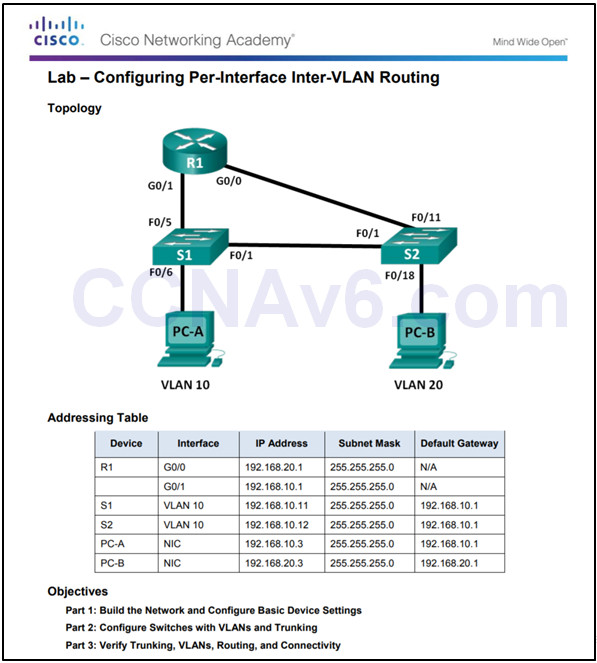
6.3.2.4 Lab – Configuring Per-Interface Inter-VLAN Routing
6.3.3 – Configure Router-on-a-Stick Inter-VLAN Routing
6.3.3.1 – Configure Router-on-a Stick: Preparation
An alternative to legacy inter-VLAN routing is to use VLAN trunking and subinterfaces.
VLAN trunking allows a single physical router interface to route traffic for multiple VLANs.
The physical interface of the router must be connected to a trunk link on the adjacent switch.
On the router, subinterfaces are created for each unique VLAN.
Each subinterface is assigned an IP address specific to its subnet or VLAN and is also configured to tag frames for that VLAN.
6.3.3.2 – Configure Router-on-a Stick: Switch Configuration
To enable inter-VLAN routing using router-on-a stick, start by enabling trunking on the switch port that is connected to the router.
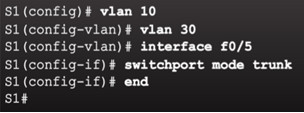
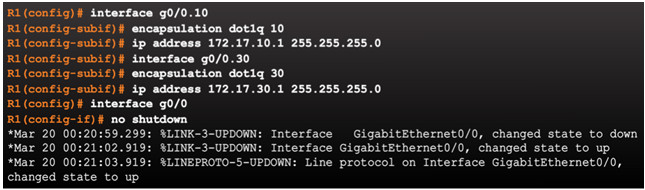
6.3.3.3 – Configure Router-on-a Stick: Router Subinterface Configuration
The router-on-a-stick method requires subinterfaces to be configured for each routable VLAN.
- The subinterfaces must be configured to support VLANs using the encapsulation dot1Q VLAN-ID interface configuration command.
6.3.3.4 – Configure Router-on-a Stick: Verifying Subinterfaces
By default, Cisco routers are configured to route traffic between local subinterfaces.
- As a result, routing does not specifically need to be enabled.
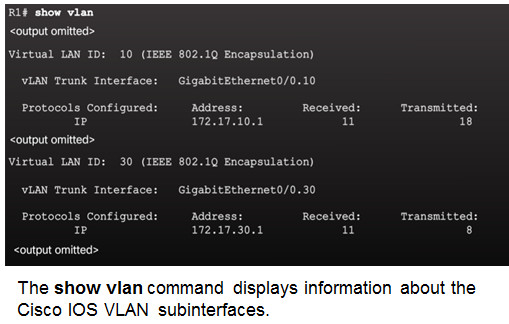
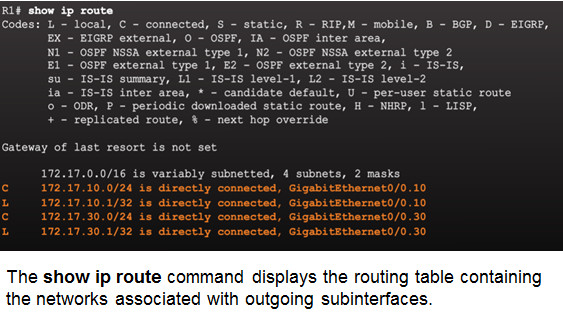
Use the show vlan and show ip route commands to verify the subinterface configurations.
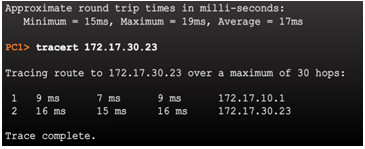
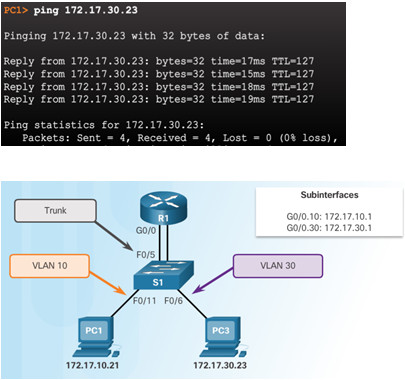
6.3.3.5 – Configure Router-on-a Stick: Verifying Routing
Remote VLAN device connectivity can be tested using the pingcommand.
- The command sends an ICMP echo request and when a host receives an ICMP echo request, it responds with an ICMP echo reply.
Tracert is a useful utility for confirming the routed path taken between two devices.
6.3.3.6 -Packet Tracer – Configuring Router-on-a-Stick Inter-VLAN Routing
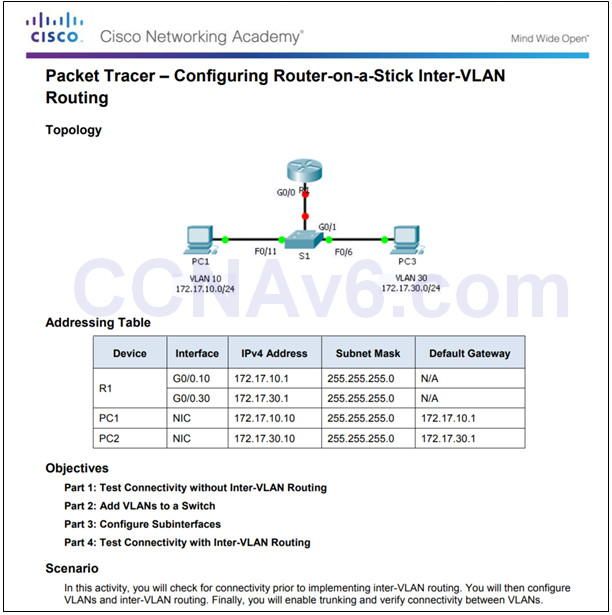
6.3.3.6 Packet Tracer – Configuring Router-on-a-Stick Inter-VLAN Routing
6.3.3.7 -Lab – Configuring 801.2Q Trunk-Based Inter-VLAN Routing
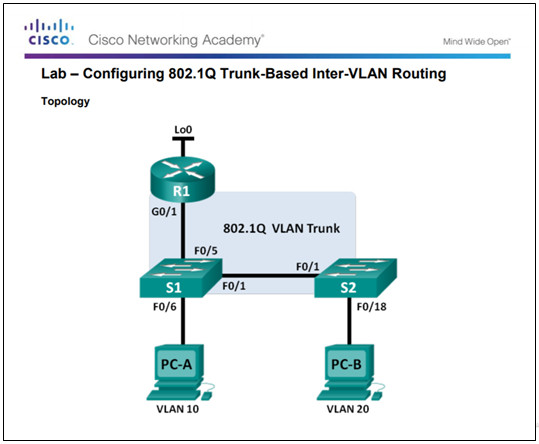
6.3.3.7 Lab – Configuring 802.1Q Trunk-Based Inter-VLAN Routing
6.3.3.8 -Packet Tracer – Inter-VLAN Routing Challenge
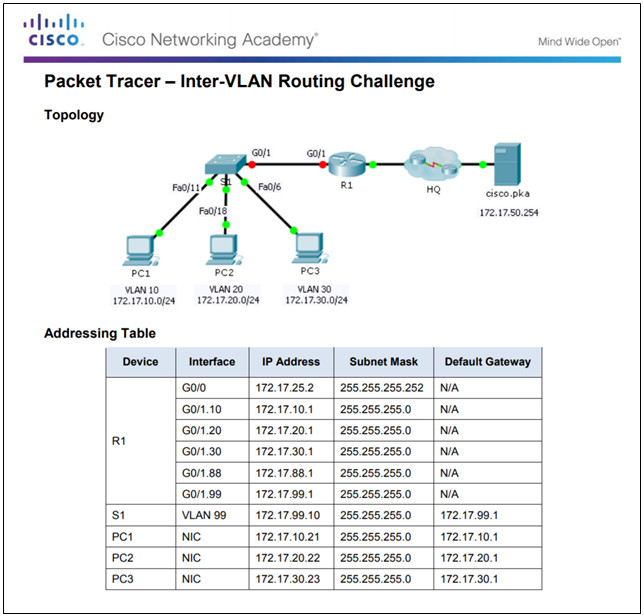
6.3.3.8 Packet Tracer – Inter-VLAN Routing Challenge
6.4 – Summary
6.4.1 – Conclusion
6.4.1.1 The Inside Track Instructions
6.4.1.1 The Inside Track Instructions
6.4.1.2 – Packet Tracer – Skills Integration Challenge
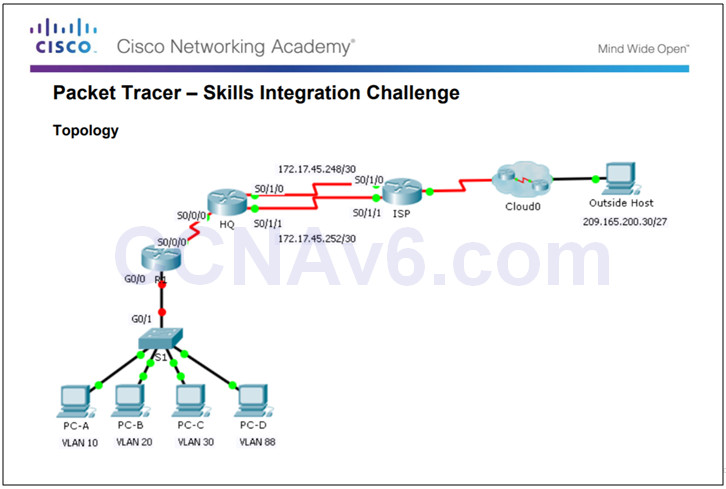
6.4.1.2 Packet Tracer – Skills Integration Challenge
6.4.1.3 – Chapter 6: VLANs
Explain how VLANs segment broadcast domains in a small to medium-sized business network.
Implement VLANs to segment a small to medium-sized business network..
Configure routing between VLANs in a small to medium-sized business network.
New Terms and Commands
Section 6.1
| •VLAN
•Logical broadcast domain •Data VLAN •Default VLAN •Native VLAN •Management VLAN •show vlan brief •Voice VLAN •VLAN Trunk •VLAN Segmentation •IEEE 802.1Q •VLAN Tagging •Canonical Format Identifier (CFI) |
•User Priority
•VLAN ID •Type •show interfaces int switchport
|
Section 6.2
| •Normal Range VLANs
•Extended Range VLANs •vlan vlan-id •name vlan-name •switchport mode access •switchport access vlan vlan-id •interface range •no switchport access vlan vlan-id •no vlan vlan-id •delete flash:vlan.dat •delete vlan.dat |
•show vlan
•show interfaces •show vlan summary •show interfaces vlan vlan_id •switchport mode trunk •switchport trunk allowed vlan vlan_list •switchport trunk native vlan vlan_id •no switchport trunk allowed vlan •no switchport trunk native vlan •show interfaces switchport • |
•no switchport access vlan vlan_id
•show interfaces trunk •show interfaces int_id trunk
|
Section 6.3
| •Legacy Inter-VLAN Routing
•Router-on-a-Stick Inter-VLAN Routing •interface interface_id.subinterface_id •encapsulation dot1q vlan_id •IEEE 802.1Q |
