Category: CCNA Security v1.2
CCNA Security Final Exam Answers (CCNAS v1.2 and v1.1) 1. What will be disabled as a result of the no service password-recovery command ? aaa new-model global configuration command. change to the configuration register. password encryption service. ability to access ROMmon. 2. What occurs after RSA keys are …
CCNA Security Chapter 9 Exam Answers (CCNAS v1.2 and v1.1) 1. Which three statements describe ethics in network security? (Choose three.) principles put into action in place of laws foundations for current laws set of moral principles that govern civil behavior standard that is higher than the law …
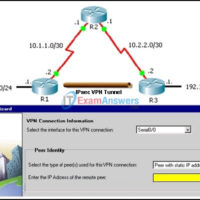
CCNA Security Chapter 8 Exam Answers (CCNAS v1.2 and v1.1) 1. What are two benefits of an SSL VPN? (Choose two.) It supports all client/server applications. It supports the same level of cryptographic security as an IPsec VPN. It has the option of only requiring an SSL-enabled web …
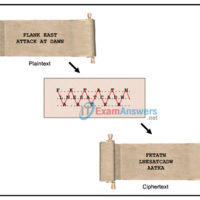
CCNA Security Chapter 7 Exam Answers (CCNAS v1.2 and v1.1) 1. Which symmetrical encryption algorithm is the most difficult to crack? 3DES AES DES RSA SHA 2. What is the basic method used by 3DES to encrypt plaintext? The data is encrypted three times with three different keys. …
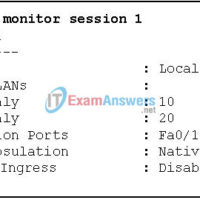
CCNA Security Chapter 6 Exam Answers (CCNAS v1.2 and v1.1) 1. Which two measures are recommended to mitigate VLAN hopping attacks? (Choose two.) Use a dedicated native VLAN for all trunk ports. Place all unused ports in a separate guest VLAN. Disable trunk negotiation on all ports connecting …
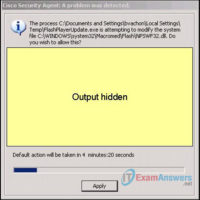
CCNA Security Chapter 5 Exam Answers (CCNAS v1.2 and v1.1) 1. An IPS sensor has detected the string confidential across multiple packets in a TCP session. Which type of signature trigger and signature type does this describe? Trigger: Anomaly-based detection Type: Atomic signature Trigger: Anomaly-based detection Type: Composite …
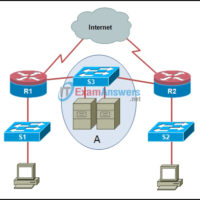
CCNA Security Chapter 4 Exam Answers (CCNAS v1.2 and v1.1) 1. Which statement accurately describes Cisco IOS zone-based policy firewall operation? The pass action works in only one direction. A router interface can belong to multiple zones. Service policies are applied in interface configuration mode. Router management interfaces …
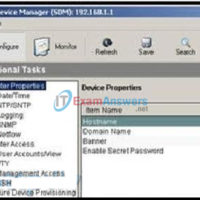
CCNA Security Chapter 3 Exam Answers (CCNAS v1.2 and v1.1) 1. Why is local database authentication preferred over a password-only login? It specifies a different password for each line or port. It provides for authentication and accountability. It requires a login and password combination on console, vty lines, …
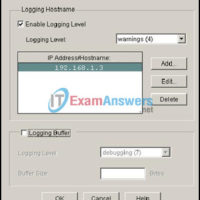
CCNA Security Chapter 2 Exam Answers (CCNAS v1.2 and v1.1) 1. Refer to the exhibit. What two pieces of information can be gathered from the generated message? (Choose two.) This message is a level five notification message. This message appeared because a minor error occurred requiring further investigation. …
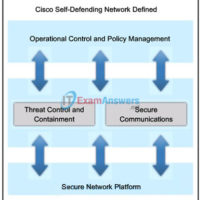
CCNA Security Chapter 1 Exam Answers (CCNAS v1.2 and v1.1) 1. What are the basic phases of attack that can be used by a virus or worm in sequential order? paralyze, probe, penetrate, persist, and propagate probe, penetrate, persist, propagate, and paralyze penetrate, persist, propagate, paralyze, and probe …