CCNA Security Chapter 2 Exam Answers (CCNAS v1.2 and v1.1)
1. Refer to the exhibit. What two pieces of information can be gathered from the generated message? (Choose two.)
![]()
- This message is a level five notification message.
- This message appeared because a minor error occurred requiring further investigation.
- This message appeared because a major error occurred requiring immediate action.
- This message indicates that service timestamps have been globally enabled.
- This message indicates that enhanced security was configured on the vty ports.
2. By default, how many seconds of delay between virtual login attempts is invoked when the login block-for command is configured?
- one
- two
- three
- four
- five
3. Refer to the exhibit. Routers R1 and R2 are connected via a serial link. One router is configured as the NTP master, and the other is an NTP client. Which two pieces of information can be obtained from the partial output of the show ntp associations detail command on R2? (Choose two.)
- Both routers are configured to use NTPv2.
- Router R1 is the master, and R2 is the client.
- Router R2 is the master, and R1 is the client.
- The IP address of R1 is 192.168.1.2.
- The IP address of R2 is 192.168.1.2.
4. What are two characteristics of the SDM Security Audit wizard? (Choose two.)
- It uses interactive dialogs and prompts to implement AAA.
- It automatically enables Cisco IOS firewall and implements Cisco IOS IPS security configurations to secure the router.
- It displays a screen with Fix-it check boxes to let you choose which potential security-related configuration changes to implement.
- It requires users to first identify which router interfaces connect to the inside network and which connect to the outside network.
- It is initiated from CLI and executes a script in which the managment plane functions and forwarding plane services are tested against known vulnerabilities.
5. If AAA is already enabled, which three CLI steps are required to configure a router with a specific view? (Choose three.)
- assign a secret password to the view
- assign commands to the view
- assign users who can use the view
- associate the view with the root view
- create a superview using the parser view view-name command
- create a view using the parser viewview-name command
6. Refer to the exhibit. Which statement regarding the JR-Admin account is true?
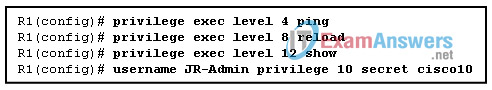
- JR-Admin can issue show, ping, and reload commands.
- JR-Admin can issue ping and reload commands.
- JR-Admin can issue only ping commands.
- JR-Admin can issue debug and reload commands.
- JR-Admin cannot issue any command because the privilege level does not match one of those defined.
7. Which recommended security practice prevents attackers from performing password recovery on a Cisco IOS router for the purpose of gaining access to the privileged EXEC mode?
- Keep a secure copy of the router Cisco IOS image and router configuration file as a backup.
- Disable all unused ports and interfaces to reduce the number of ways that the router can be accessed.
- Configure secure administrative control to ensure that only authorized personnel can access the router.
- Locate the router in a secure locked room that is accessible only to authorized personnel.
- Provision the router with the maximum amount of memory possible.
8. Which three options can be configured by Cisco AutoSecure? (Choose three.)
- CBAC
- SNMP
- syslog
- security banner
- interface IP address
- enable secret password
9. Refer to the exhibit. Based on the output of the show running-config command, which type of view is SUPPORT?
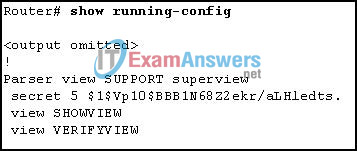
- secret view, with a level 5 encrypted password
- root view, with a level 5 encrypted secret password
- superview, containing SHOWVIEW and VERIFYVIEW views
- CLI view, containing SHOWVIEW and VERIFYVIEW commands
10. Which three services on a router does Cisco SDM One-Step Lockdown enable? (Choose three.)
- SNMP
- TCP intercepts
- SSH access to the router
- Cisco Discovery Protocol
- password encryption service
- firewall on all outside interfaces
11. An administrator defined a local user account with a secret password on router R1 for use with SSH. Which three additional steps are required to configure R1 to accept only encrypted SSH connections? (Choose three.)
- configure the IP domain name on the router
- enable inbound vty Telnet sessions
- generate the SSH keys
- configure DNS on the router
- enable inbound vty SSH sessions
- generate two-way pre-shared keys
12. Which statement describes the operation of the Cisco SDM Security Audit wizard?
- The wizard configures a router to prevent unauthorized access.
- The wizard compares a router configuration against recommended settings.
- The wizard monitors network data and logs possible unauthorized or malicious traffic.
- The wizard logs the effectiveness of network security measures for baseline comparisons.
13. An administrator needs to create a user account with custom access to most privileged EXEC commands. Which privilege command is used to create this custom account?
- privilege exec level 0
- privilege exec level 1
- privilege exec level 2
- privilege exec level 15
14. Which three areas of router security must be maintained to secure an edge router at the network perimeter? (Choose three.)
- physical security
- flash security
- operating system security
- remote access security
- router hardening
- zone isolation
15. Which service is enabled on a Cisco router by default that can reveal significant information about the router and potentially make it more vulnerable to attack?
- HTTP
- CDP
- FTP
- NTP
- TFTP
16. Which two operations are required to implement Cisco SDM One-Step Lockdown? (Choose two.)
- Choose the One-Step Lockdown feature.
- Apply the documented network policies.
- Deliver the configuration changes to the router.
- Compare the router configuration against recommended settings.
- Select the Firewall and ACL task on the SDM Configuration screen.
17. Which statement matches the CLI commands to the SDM wizard that performs similar configuration functions?
- aaa configuration commands and the SDM Basic Firewall wizard
- auto secure privileged EXEC command and the SDM One-Step Lockdown wizard
- class-maps, policy-maps, and service-policy configuration commands and the SDM IPS wizard
- setup privileged EXEC command and the SDM Security Audit wizard
18. Refer to the exhibit. What is the significance of secret 5 in the generated output?

- The ADMIN password is encrypted using DH group 5.
- The ADMIN password is encrypted via the service password-encryption command.
- The ADMIN password is hashed using MD5.
- The ADMIN password is hashed using SHA.
19. Which three commands are required to restore a primary bootset from a secure archive on a router on which Cisco IOS resilience is enabled? (Choose three.)
- Restart the router in ROM monitor mode and display the secure bootset Cisco IOS image name using the dir command.
- Restart the router, enter privileged EXEC mode, and display the secure bootset Cisco IOS image name using the show flash command.
- Boot the secure bootset Cisco IOS image using the boot command with the filename.
- Copy the secure bootset Cisco IOS image to flash using the copy IOS-backup-image flash command.
- Restore the secure configuration file using the copy config-backup flash command.
- Restore the secure configuration file using the secure boot-config restore filename command.
20. Which set of commands are required to create a username of admin, hash the password using MD5, and force the router to access the internal username database when a user attempts to access the console?
- R1(config)# username admin password Admin01pa55
R1(config)# line con 0
R1(config-line)# login local - R1(config)# username admin password Admin01pa55
R1(config)# line con 0
R1(config-line)# login internal - R1(config)# username admin Admin01pa55 encr md5
R1(config)# line con 0
R1(config-line)# login local - R1(config)# username admin secret Admin01pa55
R1(config)# line con 0
R1(config-line)# login local - R1(config)# username admin secret Admin01pa55
R1(config)# line con 0
R1(config-line)# login internal
21. Refer to the exhibit. Which two statements describe the current SDM logging setup? (Choose two.)
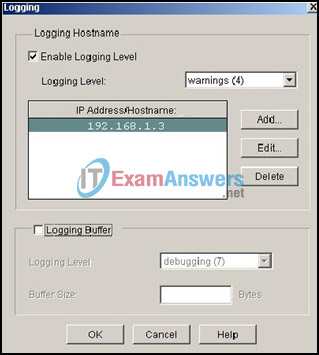
- Buffered logging will be enabled on the router for Logging Level 7 messages.
- Buffered logging will be enabled on the syslog server for Logging Level 7 messages.
- All messages with a trap level of 4 and higher (less critical) will be logged.
- All messages with a trap level of 4 and lower (more critical) will be logged.
- The router interface IP address that is connected to the syslog server is 192.168.1.3.
- The syslog server IP address is 192.168.1.3.
22. What are two characteristics of SNMP community strings? (Choose two.)
- A vulnerability of SNMPv1, SNMPv2, and SNMPv3 is that they send the community strings in plaintext.
- Commonly known community strings should be used when configuring secure SNMP.
- If the manager sends one of the correct read-only community strings, it can get information and set information in an agent.
- SNMP read-only community strings can be used to get information from an SNMP-enabled device.
- SNMP read-write community strings can be used to set information on an SNMP-enabled device.
23. What is the minimum recommended modulus key length for keys generated to use with SSH?
- 256
- 512
- 768
- 1024
- 2048
24. Which two characteristics apply to Role-Based CLI Access superviews? (Choose two.)
- CLI views have passwords, but superviews do not have passwords.
- Users logged in to a superview can access all commands specified within the associated CLI views.
- A single superview can be shared among multiple CLI views.
- Commands cannot be configured for a specific superview.
- Deleting a superview deletes all associated CLI views.
25. Refer to the exhibit. What two facts can be determined from the output? (Choose two.)

- The Cisco IOS image and configuration files have been properly secured.
- ROMmon mode will be inaccessible upon entering the privileged EXEC reload command.
- The Cisco IOS Resilient Configuration feature is enabled.
- The Cisco IOS Resilient Configuration feature has detected an image version mismatch.
- The Cisco IOS configuration files have been erased.
26. What are three requirements that must be met if an administrator wants to maintain device configurations via secure in-band management? (Choose three.)
- network devices configured to accommodate SSH
- a separate network segment connecting all management devices
- at least one router acting as a terminal server
- encryption of all remote access management traffic
- connection to network devices through a production network or the Internet
- direct access to the console ports of all network devices
27. Why is the usernamenamesecretpassword command preferred over the usernamenamepasswordpassword command?
- It uses the MD5 algorithm for encrypting passwords.
- It uses the standard type 7 algorithm for encrypting passwords.
- It allows the administrator to configure passwords of any length.
- It does not require the login local command to enable the local database for authentication.
28. Which two statements describe the initial deployed services of Cisco routers and recommended security configuration changes? (Choose two.)
- CDP is disabled by default and should be enabled on all interfaces, even when the service is not required.
- Configuration autoloading is disabled by default but should be enabled, even when the service is not required.
- ICMP mask reply is disabled by default but should be enabled on untrusted interfaces.
- ICMP unreachable notifications are enabled by default but should be disabled on untrusted interfaces.
- FTP is enabled by default and should be disabled.
- TCP keepalives are disabled by default but should be enabled globally to prevent certain DoS attacks.
29. Which command is used to verify the existence of a secure Cisco IOS image file?
- show version
- dir
- show flash
- show secure bootset
30. Which three types of views are available when configuring the Role-Based CLI Access feature? (Choose three.)
- superuser view
- root view
- superview
- CLI view
- admin view
- config view
31. Why is the username name secret password command preferred over the username name password password command?
- It uses the MD5 algorithm for encrypting passwords.
- It uses the standard type 7 algorithm for encrypting passwords.
- It allows the administrator to configure passwords of any length.
- It does not require the login local command to enable the local database for authentication.
32. Which statement describes the operation of the CCP Security Audit wizard?
- The wizard compares a router configuration against recommended settings.
- The wizard monitors network data and logs possible unauthorized or malicious traffic.
- The wizard logs the effectiveness of network security measures for baseline comparisons.
- The wizard performs an analysis of implemented security measures based on a saved baseline.
33. Which three services does CCP One-Step Lockdown enable? (Choose three.)
- SNMP
- TCP intercepts
- SSH access to the router
- Cisco Discovery Protocol
- password encryption
- firewall on all outside interfaces
34. Refer to the exhibit. Which three things occur if a user attempts to log in four times within 10 seconds and uses an incorrect password? (Choose three).
- Subsequent virtual login attempts from the user are blocked for 60 seconds.
- During the quiet mode, an administrator can virtually log in from any host on network 172.16.1.0/24.
- Subsequent console login attempts are blocked for 60 seconds.
- A message is generated that indicates the username and source IP address of the user.
- During the quiet mode, an administrator can log in from host 172.16.1.2.
- No user can log in virtually from any host for 60 seconds.
35. Which statement describes the CCP Security Audit wizard?
- After the wizard identifies the vulnerabilities, the CCP One-Step Lockdown feature must be used to make all security-related configuration changes.
- After the wizard identifies the vulnerabilities, it automatically makes all security-related configuration changes.
- The wizard autosenses the inside trusted and outside untrusted interfaces to determine possible security problems.
- The wizard is based on the Cisco IOS AutoSecure feature.
- The wizard is enabled by using the Intrusion Prevention task.
36. What command must be issued on a Cisco router that will serve as an authoritative NTP server?
- Ntp master 1
- Ntp server 172.16.0.1
- Ntp broadcast client
- Clock set 11:00:00 DEC 20 2010
