CCNA Security Chapter 5 Exam Answers (CCNAS v1.2 and v1.1)
1. An IPS sensor has detected the string confidential across multiple packets in a TCP session. Which type of signature trigger and signature type does this describe?
- Trigger: Anomaly-based detection
Type: Atomic signature - Trigger: Anomaly-based detection
Type: Composite signature - Trigger: Pattern-based detection
Type: Atomic signature - Trigger: Pattern-based detection
Type: Composite signature - Trigger: Policy-based detection
Type: Atomic signature - Trigger: Policy-based detection
Type: Composite signature
2. A network administrator tunes a signature to detect abnormal activity that might be malicious and likely to be an immediate threat. What is the perceived severity of the signature?
- high
- medium
- low
- informational
3. What are two major drawbacks to using HIPS? (Choose two.)
- HIPS has difficulty constructing an accurate network picture or coordinating the events happening across the entire network.
- HIPS installations are vulnerable to fragmentation attacks or variable TTL attacks.
- With HIPS, the network administor must verify support for all the different operating systems used in the network.
- If the network traffic stream is encrypted, HIPS is unable to access unencrypted forms of the traffic.
- With HIPS, the success or failure of an attack cannot be readily determined.
4. Which type of intrusion detection triggers an action if excessive activity occurs beyond a specified threshold of normal activity?
- pattern-based detection
- anomaly-based detection
- policy-based detection
- honey pot-based detection
5. Which two statements characterize a network-based IPS implementation? (Choose two.)
- It makes hosts visible to attackers.
- It is unable to examine encrypted traffic.
- It monitors to see if an attack was successful.
- It provides application-level encryption protection.
- It is independent of the operating system on hosts.
6. What information is provided by the show ip ips configuration configuration command?
- detailed IPS signatures
- alarms that were sent since the last reset
- the number of packets that are audited
- the default actions for attack signatures
7. When editing IPS signatures with SDM, which action drops all future packets from a TCP flow?
- Deny Packet Inline
- Deny TCP Connection
- Deny Attacker Inline
- Deny Connection Inline
8. Refer to the exhibit. A user was installing a Flash Player upgrade when the CSA displayed the dialog box shown. Which default action is taken by CSA if the user does not respond within 4 minutes and 20 seconds?
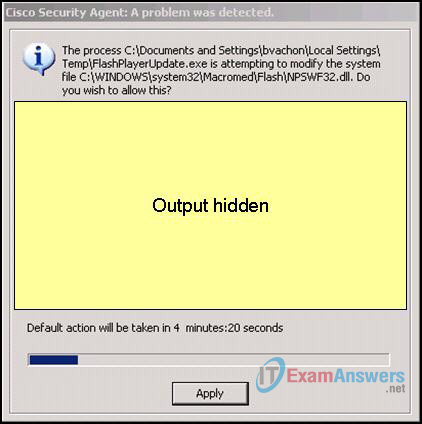
- The action is allowed, and a log entry is recorded.
- The action is allowed, and CSA does not prompt the user again.
- The action is denied, and a log entry is recorded.
- The action is denied, and the FlashPlayerUpdate.exe application is terminated.
9. Refer to the exhibit. When modifying an IPS signature action, which two check boxes should be selected to create an ACL that denies all traffic from the IP address that is considered the source of the attack and drops the packet and all future packets from the TCP flow? (Choose two.)
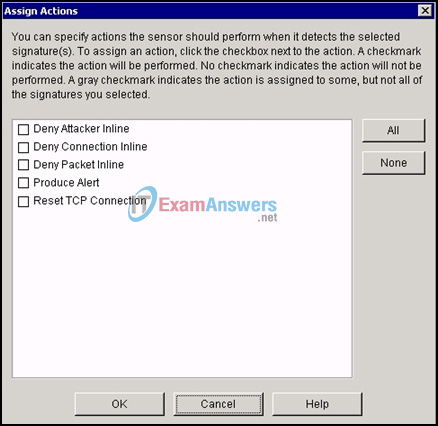
- Deny Attacker Inline
- Deny Connection Inline
- Deny Packet Inline
- Produce Alert
- Reset TCP Connection
10. Refer to the exhibit. What is the significance of the number 10 in the signature 6130 10 command?
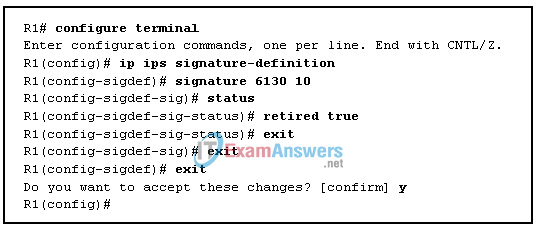
- It is the alert severity.
- It is the signature number.
- It is the signature version.
- It is the subsignature ID.
- It is the signature fidelity rating.
11. What is a disadvantage of network-based IPS as compared to host-based IPS?
- Network-based IPS is less cost-effective.
- Network-based IPS cannot examine encrypted traffic.
- Network-based IPS does not detect lower level network events.
- Network-based IPS should not be used with multiple operating systems.
12. Which two files could be used to implement Cisco IOS IPS with version 5.x format signatures? (Choose two.)
- IOS-Sxxx-CLI.bin
- IOS-Sxxx-CLI.pkg
- IOS-Sxxx-CLI.sdf
- realm-cisco.priv.key.txt
- realm-cisco.pub.key.txt
13. Why is a network that deploys only IDS particularly vulnerable to an atomic attack?
- The IDS must track the three-way handshake of established TCP connections.
- The IDS must track the three-way handshake of established UDP connections.
- The IDS permits malicious single packets into the network.
- The IDS requires significant router resources to maintain the event horizon.
- The stateful properties of atomic attacks usually require the IDS to have several pieces of data to match an attack signature.
14. Refer to the exhibit. Based on the SDM screen shown, which two actions will the signature take if an attack is detected? (Choose two.)
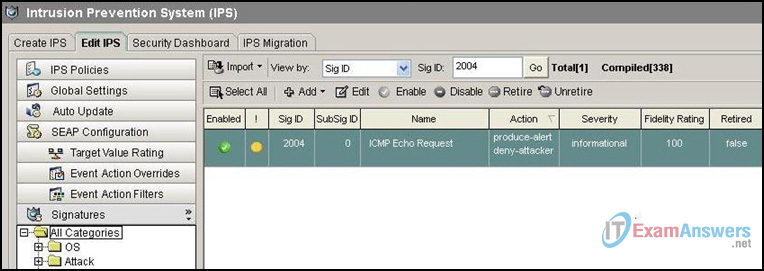
- Reset the TCP connection to terminate the TCP flow.
- Drop the packet and all future packets from this TCP flow.
- Generate an alarm message that can be sent to a syslog server.
- Drop the packet and permit remaining packets from this TCP flow.
- Create an ACL that denies traffic from the attacker IP address.
15. Which two Cisco IOS commands are required to enable IPS SDEE message logging? (Choose two.)
- logging on
- ip ips notify log
- ip http server
- ip ips notify sdee
- ip sdee events 500
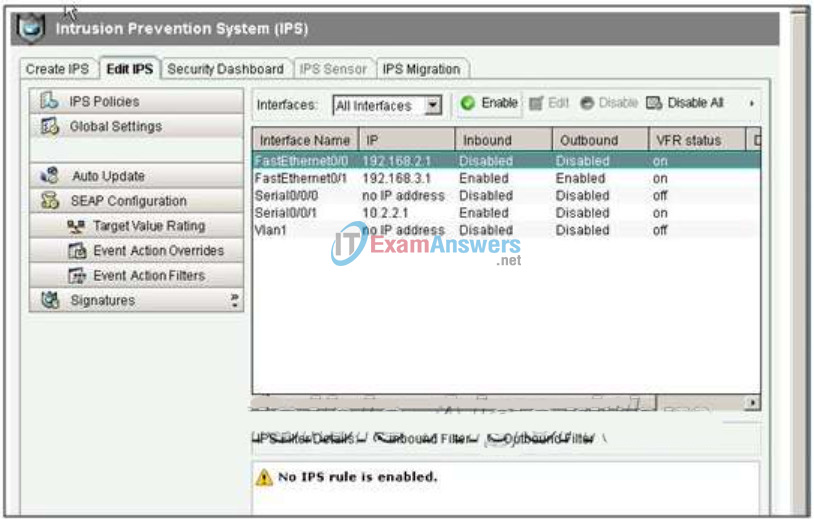
16. Refer to the exhibit. Which option tab on the SDM IPS screen is used to view the Top Threats table and deploy signatures associated with those threats?
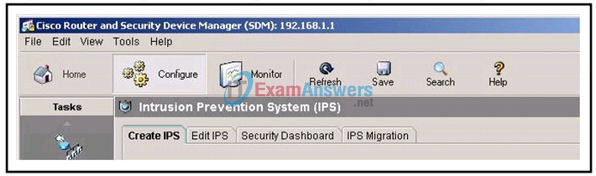
- Create IPS
- Edit IPS
- Security Dashboard
- IPS Migration
17. Which Cisco IOS configuration option instructs the IPS to compile a signature category named ios_ips into memory and use it to scan traffic?
- R1(config)# ip ips signature-category
R1(config-ips-category)# category all
R1(config-ips-category-action)# retired false - R1(config)# ip ips signature-category
R1(config-ips-category)# category ios_ips basic
R1(config-ips-category-action)# retired false - R1(config)# ip ips signature-category
R1(config-ips-category)# category all
R1(config-ips-category-action)# enabled true - R1(config)# ip ips signature-category
R1(config-ips-category)# category ios_ips basic
R1(config-ips-category-action)# enabled true
18. Refer to the exhibit. What is the result of issuing the Cisco IOS IPS commands on router R1?
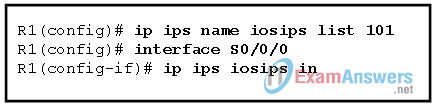
- A named ACL determines the traffic to be inspected.
- A numbered ACL is applied to S0/0/0 in the outbound direction.
- All traffic that is denied by the ACL is subject to inspection by the IPS.
- All traffic that is permitted by the ACL is subject to inspection by the IPS.
19. What are two IPS configuration best practices that can help improve IPS efficiency in a network? (Choose two.)
- Configure all sensors to check the server for new signature packs at the same time to ensure that they are all synchronized.
- Configure the sensors to simultaneously check the FTP server for new signature packs.
- Ensure that signature levels that are supported on the management console are synchronized with the signature packs on the sensors.
- Update signature packs manually rather than automatically to maintain close control when setting up a large deployment of sensors.
- Place signature packs on a dedicated FTP server within the management network.
20. Refer to the exhibit. What is the significance of the small red flag waving in the Windows system tray?
![]()
- Cisco Security Agent is installed but inactive.
- Network-based IPS is active and has detected a potential security problem.
- Cisco Security Agent is active and has detected a potential security problem.
- A network-based IPS sensor has pushed an alert to a host running Cisco Security Agent.
21. Which two benefits does the IPS version 5.x signature format provide over the version 4.x signature format? (Choose two.)
- addition of signature micro engines
- support for IPX and AppleTalk protocols
- addition of a signature risk rating
- support for comma-delimited data import
- support for encrypted signature parameters
22. Which statement is true about an atomic alert that is generated by an IPS?
- It is an alert that is generated every time a specific signature has been found.
- It is a single alert sent for multiple occurrences of the same signature.
- It is both a normal alarm and a summary alarm being sent simultaneously at set intervals.
- It is an alert that is used only when a logging attack has begun.
23. Which Cisco IPS feature allows for regular threat updates from the Cisco SensorBase Network database?
- event correlation
- global correlation
- IPS Manager Express
- honeypot-based detection
- security-independent operation
24. Which protocol is used when an IPS sends signature alarm messages?
- FTP
- SDEE
- SIO
- SNMP
25. Refer to the exhibit. Based on the configuration that is shown, which statement is true about the IPS signature category?
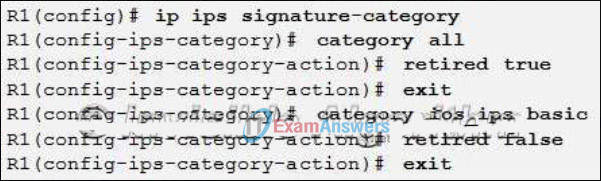
- Only signatures in the ios_ips basic category will be compiled into memory for scanning.
- Only signatures in the ios_ips advanced category will be compiled into memory for scanning.
- All signature categories will be compiled into memory for scanning, but only those signatures in the ios_ips basic category will be used for scanning purposes.
- All signatures categories will be compiled into memory for scanning, but only those signatures within the ios_ips advanced category will be used for scanning purposes.
26. A network security administrator would like to check the number of packets that have been audited by the IPS. What command should the administrator use?
- show ip ips signatures
- show ip ips interfaces
- show ip ips statistics
- show ip ips configuration
27. Refer to the exhibit. Based on the configuration commands that are shown, how will IPS event notifications be sent?

- HTTP format
- SDEE format
- syslog format
- TFTP format
28. Refer to the exhibit. What action will be taken if a signature match occurs?
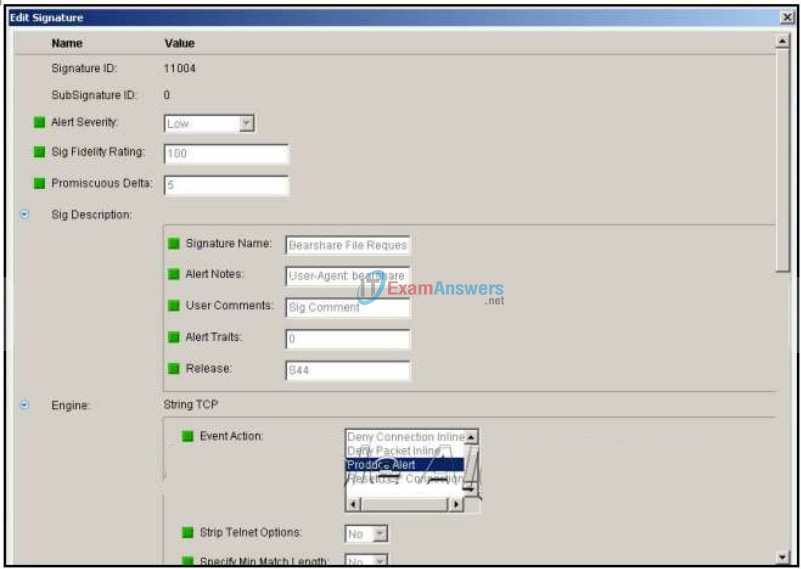
- An ACL will be created that denies all traffic from the IP address that is considered the source of the attack, and an alert will be generated.
- This packet and all future packets from this TCP flow will be dropped, and an alert will be generated.
- Only this packet will be dropped, and an alert will be generated.
- The packet will be allowed, and an alert will be generated.
- The packet will be allowed, and no alert will be generated.
29. An administrator is using CCP to modify a signature action so that if a match occurs, the packet and all future packets from the TCP flow are dropped. What action should the administrator select?
- deny-attacker-inline
- deny-connection-inline
- deny-packet-inline
- produce-alert
- reset-tcp-connection
30. Refer to the exhibit. Based on the configuration, what traffic is inspected by the IPS?
- only traffic entering the s0/0/1 interface
- all traffic entering or leaving the fa0/1 interface
- only traffic traveling from the s0/0/1 interface to the fa0/1 interface
- all traffic entering the s0/0/1 interface and all traffic leaving the fa0/1 interface
- all traffic entering the s0/0/1 interface and all traffic entering and leaving the fa0/1 interface
31. Refer to the exhibit. As an administrator is configuring an IPS, the error message that is shown appears. What does this error message indicate?
![]()
- The signature definition file is invalid or outdated.
- The public crypto key is invalid or entered incorrectly.
- The flash directory where the IPS signatures should be stored is corrupt or nonexistent.
- SDEE notification is disabled and must be explicitly enabled.
32. Refer to the exhibit. An administrator has configured router R1 as indicated. However, SDEE messages fail to log. Which solution corrects this problem?
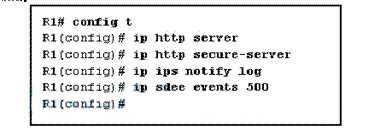
- Issue the logging on command in global configuration.
- Issue the ip audit notify log command in global configuration.
- Issue the clear ip ips sdee events command to clear the SDEE buffer.
- Issue the ip ips notify sdee command in global configuration.
33. What is a zero-day attack?
- an attack that targets software vulnerabilities unknown or unpatched by the software vendor
- an extortion threat directed against a bank, and demanding a huge amount of money within a short response time, typically within a day
- a type of DoS attack that launches within 24 hours after it first infects multiple computers around the world
- a rapid exploit attack of employee login credentials via the use of social engineering techniques
34. What is a disadvantage of a pattern-based detection mechanism?
- It cannot detect unknown attacks.
- Its configuration is complex.
- It is difficult to deploy in a large network.
- The normal network traffic pattern must be profiled first.
35. Refer to the exhibit. Which option tab on the CCP screen is used to view the Top Threats table and deploy signatures associated with those threats?
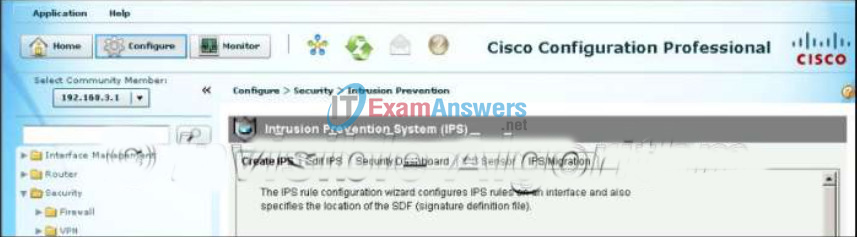
- IPS Migration
- IPS Sensor
- Edit IPS
- Security Dashboard
- Create IPS
