CCNA Security Final Exam Answers (CCNAS v1.2 and v1.1)
1. What will be disabled as a result of the no service password-recovery command ?
- aaa new-model global configuration command.
- change to the configuration register.
- password encryption service.
- ability to access ROMmon.
2. What occurs after RSA keys are generated on a Cisco router to prepare for secure device management?
- All vty ports are automatically configured for SSH to provide secure management.
- The general-purpose key size must be specified for authentication with the crypto key generate rsa general-keys mo command.
- The keys must be zeroized to reset secure shell before configuring other parameters.
- The generated keys can be used by SSH.
3. Which action best describe a MAC address spoofing attack?
- altering the MAC address of an attacking host to match that of a legitimate host.
- bombarding a switch with fake source MAC addresses.
- forcing the election of a rogue root bridge
- flooding the LAN with excessive traffic
4. What functionality is provided by Cisco SPAN in a switched network?
- It mitigates MAC address overflow attacks.
- It mirrors traffic that passes through a switch port or VLAN to another port for traffic analysis.
- It protects the switched network from receiving BPDUs on ports that should not be receiving them.
- It inspects voice protocols to ensure that SIP, SCCP, H.323, and MGCP requests conform to voice standards.
- It copies traffic that passes through a switch interface and sends the data directly to a syslog or SNMP server for analysis.
5. What precaution should be considered when the no service password–recovery command has been issued on an IOS device?
- The passwords in the configuration files are in clear text.
- IOS recovery requires a new system flash with the IOS image.
- When the password is lost, access to the device will be terminated.
- The device must use simple password authentication and cannot have user authentication.
6. A network technician is configuring SNMPv3 and has set a security level of auth. What is the effect of this setting?
- Authenticates a packet using the SHA algorithm only.
- Authenticates a packet by a string match of the username or community string.
- Authenticates a packet by using either the HMAC with MD5 method or the SHA method.
- Authenticates a packet by using either the HMAC MD5 or HMAC SHA algorithms and encrypts the packet using either the DES, 3DES or AES algorithms.
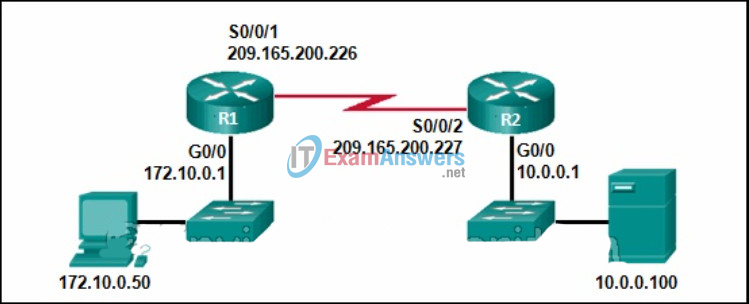
7. Refer to the exhibit. Which type of VPN is implemented?
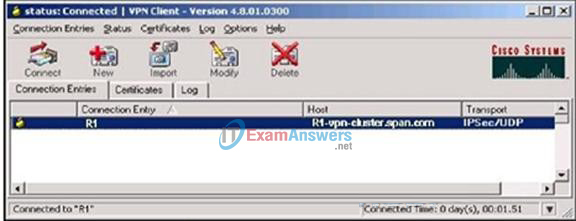
- remote-access GRE VPN
- remote-access IPsec VPN
- remote-access SSL VPN
- site-to-site GRE VPN
- site-to-site IPsec VPN
- site-to-site SSL VPN
8. Refer to the exhibit. What will be the effect of the commands that are shown on R1?
Router(config)# ntp authenticate Router(config)# ntp authentication-key 42 md5 aNiceKey Router(config)# ntp trusted-key 2
- Authentication with the NTP master will be successful, and R1 will get the time from the NTP master.
- Authentication with the NTP master will be successful, but R1 will not get the time from the NTP master.
- Authentication with the NTP master will fail, and R1 will get the time from the NTP master.
- Authentication with the NTP master will fail, and R1 will not get the time from the NTP master.
9. What login enhancement configuration command helps successive login DoS attacks?
- exec-timeout
- login block-for
- privilege exec level
- service password-encryption
10. What are access attacks?
- attacks that prevent users from accessing network services
- attacks that modify or corrupt traffic as that traffic travels across the network
- attacks that exploit vulnerabilities to gain access to sensitive information
- attacks that involve the unauthorized discovery and mapping of systems, services, and vulnerability
11. Refer to the exhibit. An administrator is examining the message in a syslog server. What can be determined from the message?
Nov 30 11:00:24 EST: %SYS-5-CONFIG-I: Configured from console by vty0 (10.64.2.2)
- This is a notification message for a normal but significant condition
- This is an alert message for which immediate action is needed
- This is an error message for which warning conditions exist.
- This is an error message indicating the system is unusable
12. Which three major subpolicies should comprise a comprehensive security policy that meets the security needs of a typical enterprise? (Choose three)
- end-user policies
- departmental policies
- governing policies
- human resource policies
- organizational policies
- technical policies
13. Refer to the exhibit. An administrator has entered the commands that are shown on router R1. At what trap level is the logging function set?
R1(config)# logging host 10.1.1.17 R1(config)# logging trap errors R1(config)# logging source-interface loopback 0 R1(config)# logging on
- 2
- 3
- 5
- 6
14. Which mitigation technique can help prevent MAC table overflow attacks?
- root guard
- BPDU guard
- storm control
- switchport security
15. An organization requires that individual users be authorized to issue specific Cisco IOS commands. Which AAA protocols support this requirement?
- TACACS+ because it separates authentication and authorization, allowing for more customization.
- RADIUS because it supports multiple protocols, including ARA and NetBEUI.
- TACACS+ because it supports extensive accounting on a per-user or per-group basis.
- RADIUS because it implements authentication and authorization as one process.
16. Refer to the exhibit. Based on the IPS configuration that is provided, which statement is true?
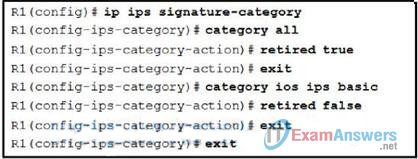
- The signatures in all categories will be retired and not be used by the IPS.
- The signatures in all categories will be compiled into memory and used by the IPS.
- Only the signatures in the ios_ips basic category will be compiled into memory and used by the IPS.
- The signatures in the ios_ips basic category will be retired and the remaining signatures will be compiled into memory and used by the IPS.
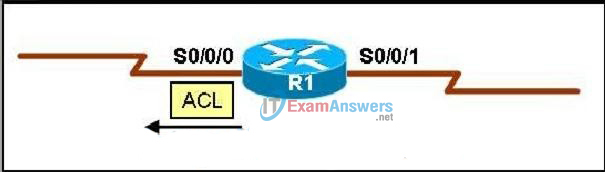
17. Refer to the exhibit. Based on the provided configuration, which traffic will be examined by the IPS that is configured on router R1?
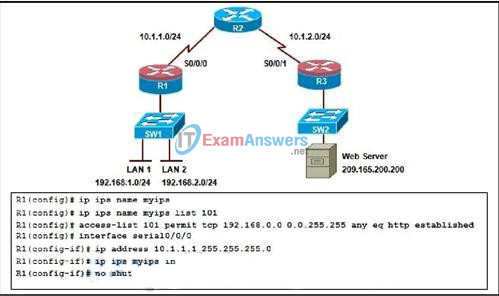
- Traffic that is initiated from LAN 1 and LAN 2
- http traffic that is initiated from LAN 1
- return traffic from the web server
- traffic that is destined to LAN 1 and LAN 2
- no traffic will be inspected
18. Refer to the exhibit. An administrator is configuring ZPF using the SDM Basic Firewall Configuration wizard. Which command is generated after the administrator selects the Finish button?
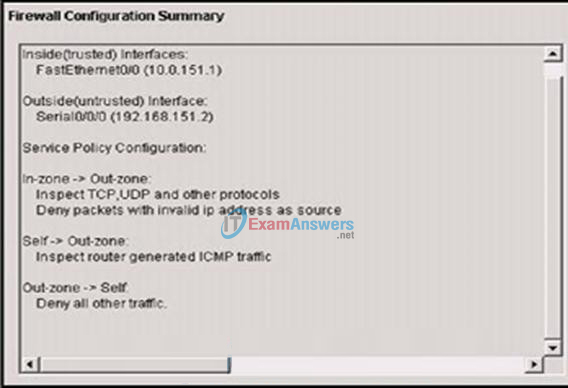
- zone security Out-zone on interface Fa0/0
- zone security Out-zone on interface S0/0/0
- zone member security Out-zone on interface Fa0/0
- zone member security Out-zone on interface s0/0/0
19. Which two statements describe appropriate general guidelines for configuring and applying ACLs? (Choose two)
- Multiple ACLs per protocol and per direction can be applied to an interface.
- If an ACL contains no permit statements, all traffic is denied by default.
- The most specific ACL statements should be entered first because of the top-down sequential nature of ACLs.
- Standard ACLs are placed closest to the source, whereas Extended ACLs are placed closest to the destination.
- If a single ACL is to be applied to multiple interfaces, it must be configured with a unique number for each interface.
20. Which three statements are characteristics of the IPsec protocol? (Choose three)
- IPsec is a framework of open standards.
- IPsec is implemented at Layer 4 of the OSI model.
- IPsec ensures data integrity by using a hash algorithm.
- IPsec uses digital certificates to guarantee confidentiality
- IPsec is bound to specific encryption algorithms, such as 3DES and AES.
- IPsec authenticates users and devices that communicate independently.
21. Which three additional precautions should be taken when remote access is required in addition to local access of networking devices? (Choose three)
- A legal notice should not be displayed when access is obtained.
- All activity to the specified ports that are required for access should be unrestricted.
- All configuration activities should required the use of SSH or HTTPS.
- All administrative traffic should be dedicated to the management network.
- The number of failed login attempts should not be limited, but the time between attempts should.
- Packet filtering should be required so that only identified administration hosts and protocols can gain access.
22. Which statement describes a factor to be considered when configuring a zone-based policy firewall?
- An interface can belong to multiple zones.
- The router always filters the traffic between interfaces in the same zone.
- The CBAC ip inspect command can coexist with ZPF as long as it is used on interfaces that are in the same security zones.
- A zone must be configured with the zone security global command before it can be used in the zone-member security command.
23. What is a result of securing the Cisco IOS image using the Cisco IOS Resilient Configuration feature?
- The Cisco IOS image file is not visible in the output of the show flash command.
- The Cisco IOS image is encrypted and then automatically backed up to a TFTP server.
- The Cisco IOS image is encrypted and then automatically backed up to the NVRAM.
- When the router boots up, the Cisco IOS image is loaded from a secure FTP location
24. What are three common examples of AAA implementation on Cisco routers? (Choose three)
- Authenticating administrator access to the router console port, and vty ports
- Authenticating remote users who are accessing the corporate LAN through IPsec VPN connections
- Implementing public key infrastructure to authenticate and authorize IPsec VPN peers using digital certificates
- Implementing command authorization with TACACS+
- Securing the router by locking down all unused services
- Tracking Cisco Netflow accounting statistics
25. When port security is enabled on a Cisco Catalyst switch, what is the default action when the maximum number of allowed MAC addresses is exceeded?
- The violation mode for the port is set to restrict.
- The MAC address table is cleared, and the new MAC address is entered into the table.
- The port remains enabled, but the bandwidth is throttled until the old MAC addresses are aged out.
- The port is shut down.
26. Which three statements describe the IPsec protocol framework? (Choose three)
- AH uses IP protocol 51.
- AH provides encryption and integrity.
- AH provides integrity and authentication.
- ESP uses UDP protocol 50.
- ESP requires both authentication and encryption.
- ESP provides encryption, authentication, and integrity.
27. Which three statements describe limitations in using privilege levels for assigning command authorization? (Choose three.)
- There is no access control to specific interfaces on a router.
- The root user must be assigned to each privilege level defined.
- Commands set on a higher privilege level are not available for lower privileged users
- Views are required to define the CLI commands that each user can access.
- Creating a user account that needs access to most but not all commands can be a tedious process
- It is required that all 16 privilege levels be defined, whether they are used
28. Which Cisco IOS configuration option instructs the IPS to compile a signature category named ios_ips into memory and use it to scan traffic?
- R1(config)# ip ips signature-category
R1(config-ips-category)# category all
R1(config-ips-category-action)# retired false - R1(config)# ip ips signature-category
R1(config-ips-category)# category ios_ips basic
R1(config-ips-category-action)# retired false - R1(config)# ip ips signature-category
R1(config-ips-category)# category all
R1(config-ips-category-action)# enabled true - R1(config)# ip ips signature-category
R1(config-ips-category)# category ios_ips basic
R1(config-ips-category-action)# enabled true
29. Refer to the exhibit. An administrator has configured router R1 as indicated. However, SDEE messages fail to log. Which solution corrects this problem?
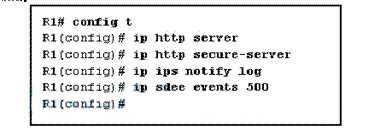
- Issue the logging on command in global configuration.
- Issue the ip ips notify sdee command in global configuration.
- Issue the ip audit notify log command in global configuration.
- Issue the clear ip ips sdee events command to clear the SDEE buffer.
30. Which three principles are enabled by a Cisco Self-Defending Network? (Choose three.)
- adaptability
- collaboration
- insulation
- integration
- mitigation
- scalability
31. What are two disadvantages of using network IPS?(Choose two.)
- Network IPS has a difficult time reconstructing fragmented traffic to determine if an attack was successful.
- Network IPS is incapable of examining encrypted traffic.
- Network IPS is operating system-dependent and must be customized for each platform.
- Network IPS is unable to provide a clear indication of the extent to which the network is being attacked.
- Network IPS sensors are difficult to deploy whennew networks are added.
32. Which access list statement permits HTTP traffic that is sourced from host 10.1.129.100 port 4300 and destined to host 192.168.30.10?
- access-list 101 permit tcp any eq 4300
- access-list 101 permit tcp 192.168.30.10 0.0.0.0 eq 80 10.1.0.0 0.0.255.255
- access-list 101 permit tcp 10.1.129.0 0.0.0.255 eq www 192.168.30.10 0.0.0.0 eq www
- access-list 101 permit tcp 10.1.128.0 0.0.1.255 eq 4300 192.168.30.0 0.0.0.15 eq www
- access-list 101 permit tcp host 192.168.30.10 eq 80 10.1.0.0 0.0.255.255 eq 4300
33. Which type of SDM rule is created to govern the traffic that can enter and leave the network based on protocol and port number?
- NAC rule
- NAT rule
- IPsec rule
- access rule
34. Refer to the exhibit. When configuring SSH on a router using SDM from the Configure menu, which two steps are required? (Choose two.)
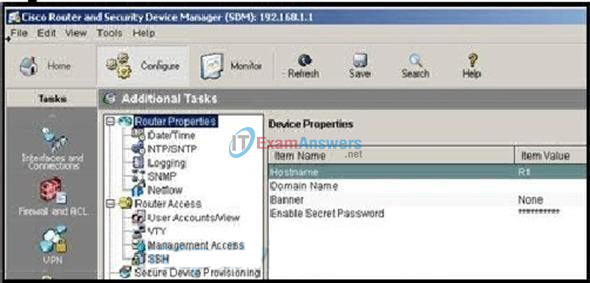
- Choose Additional Tasks > Router Access > SSH to generate the RSA keys.
- Choose Additional Tasks > Router Access > VTY to specify SSH as the input and output protocol.
- Choose Additional Tasks > Router Properties > Netflow to generate the RSA keys.
- Choose Additional Tasks > Router Properties > Logging to specify SSH as the input and output protocol.
- Choose Additional Tasks > Router Access > AAA to generate the RSA keys.
- Choose Additional Tasks > Router Access > Management Access to specify SSH as the input and output protocol
35. Refer to the exhibit. Which two statements are correct regarding the configuration on switch S1? (Choose two.)
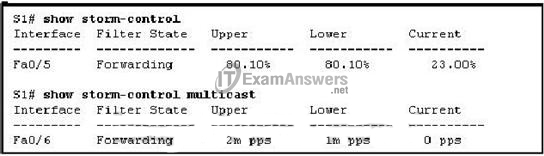
- Port Fa0/5 storm control for broadcasts will be activated if traffic exceeds 80.1 percent of the total bandwidth.
- Port Fa0/6 storm control for multicasts and broadcasts will be activated if traffic exceeds 2,000,000 packets per second.
- Port Fa0/6 storm control for multicasts will be activated if traffic exceeds 2,000,000 packets per second.
- Port Fa0/5 storm control for multicasts will be activated if traffic exceeds 80.1 percent of the total bandwidth.
- Port Fa0/5 storm control for broadcasts and multicasts will be activated if traffic exceeds 80.1 percent of 2,000,000 packets per second.
36. Refer to the exhibit. Which three things occur if a user attempts to log in four times within 10 seconds using an incorrect password? (Choose three.)
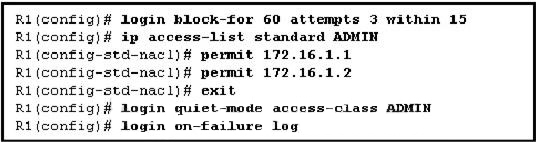
- Subsequent virtual login attempts from the user are blocked for 60 seconds.
- During the quiet mode, an administrator can virtually log in from any host on network 172.16.1.0/24.
- Subsequent console login attempts are blocked for 60 seconds.
- A message is generated indicating the username and source IP address of the user.
- During the quiet mode, an administrator can log in from host 172.16.1.2.
- No user can log in virtually from any host for 60 seconds.
37. Which type of Layer 2 attack makes a host appear as the root bridge for a LAN?
- LAN storm
- MAC address spoofing
- MAC address table overflow
- STP manipulation
- VLAN attack
38. What occurs after RSA keys are generated on a Cisco router to prepare for secure device management?
- All vty ports are automatically configured for SSH to provide secure management.
- The general-purpose key size must be specified for authentication with the crypto key generate rsa general-keys mo command.
- The keys must be zeroized to reset secure shell before configuring other parameters.
- The generated keys can be used by SSH.
39. An organization has mobile workers who usecorporate-owned laptops at customer sites to view inventory and place orders.Which type of VPN allows these workers to securely access all of theclient/server applications of the organization?
- clientless SSL VPN
- remote-access IPsec VPN
- site-to-site IPsec VPN
- HTTPS-enabled SSL VPN
40. Which two guidelines relate to in-band networkmanagement? (Choose two.)
- Apply in-band management only to devices that must be managed on the production network.
- Implement separate network segments for the production network and the management network.
- Attach all network devices to the same management network.
- Use IPSec, SSH,or SSL
41. Which three commands are required to configure SSH ona Cisco router? (Choose three.)
- ip domain-name name in global configuration mode
- transport input ssh on a vty line
- no ip domain-lookup in global configuration mode
- passwordpassword on a vty line
- service password-encryption in global configuration mode
- crypto keygenerate rsa in global configuration mode
42. An administrator needs to create a user account with custom access to most privileged EXEC commands. Which privilege command is used to create this custom account?
- privilege exec level 0
- privilege exec level 1
- privilege exec level 2
- privilege exec level 15
43. Refer to the exhibit. An administrator has configureda standard ACL on R1 and applied it to interface serial 0/0/0 in the outbounddirection. What happens to traffic leaving interface serial 0/0/0 that does notmatch the configured ACL statements?
- The resulting action is determined by the destination IP address.
- The resulting action is determined by the destination IP address and portnumber.
- The source IP address is checked and, if a match is not found, traffic isrouted out interface serial 0/0/1.
- The traffic is dropped
44. When configuring router security, which statement describes the most effective way to use ACLs to control Telnet traffic that is destined to the router itself?
- Apply the ACL to the vty lines without the in or out option required when applying ACLs to interfaces.
- The ACL is applied to the Telnet port with the ip access-group command.
- The ACL must be applied to each vty line individually.
- The ACL should be applied to all vty lines in the in direction to prevent an unwanted user from connecting to an unsecured port.
45. Which three statements describe SSL-based VPNs? (Choose three.)
- A symmetric algorithms are used for authentication and key exchange.
- It is impossible to configure SSL and IPsec VPNs concurrently on the samerouter.
- Special-purpose client software is required on the client machine.
- Symmetric algorithms are used for bulk encryption.
- The authentication process uses hashing technologies.
- The application programming interface is used to extensively modify the SSLclient software.
- The primary restriction of SSL VPNs is that they are currently supported onlyin hardware.
46. Refer to the exhibit. What information can be obtained from the AAAconfiguration statements?
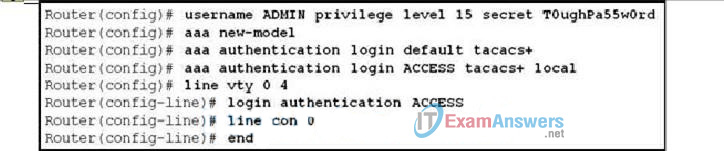
- The authentication method list used for Telnet is named ACCESS.
- The authentication method list used by the consoleport is named ACCESS.
- The local database is checked first whenauthenticating console and Telnet access to the router.
- If the TACACS+ AAA server is not available, nousers can establish a Telnet session with the router.
- If the TACACS+ AAA server is not available, consoleaccess to the router can be authenticated using the local database.
47. Which two Cisco IPSmanagement and monitoring tools are examples of GUI-based, centrally managedIPS solutions? (Choose two.)
- Cisco Adaptive Security Device Manager
- Cisco IPS Device Manager
- Cisco Router and Security Device Manager
- Cisco Security Manager
- Cisco Security Monitoring, Analysis, and Response System.
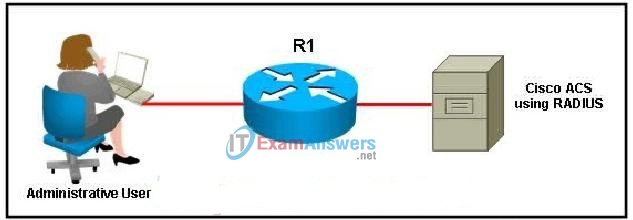
48. Refer to the exhibit.Which AAA function and protocol is in use in the network?
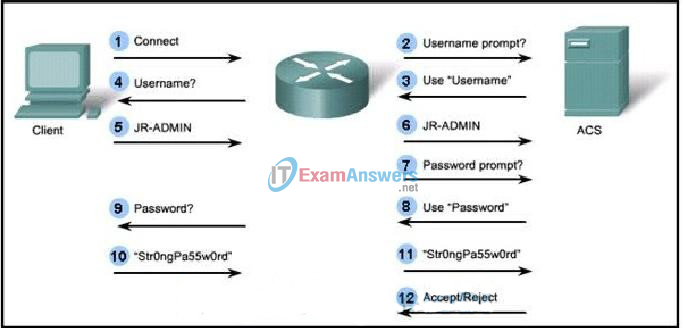
- The client is authorizing commands using the TACACS+protocol.
- The client is authorizing commands using the RADIUS protocol.
- The client is authenticating using the RADIUS protocol.
- The client is authenticating using the TACACS+protocol
49. Which three OSI layers can be filtered by a stateful firewall? (Choose three.)
- Layer 2
- Layer 3
- Layer 4
- Layer 5
- Layer 6
- Layer 7
50. Refer to the exhibit. Based on the SDM screenshown, which two actions will the signature take if an attack is detected?(Choose two.)
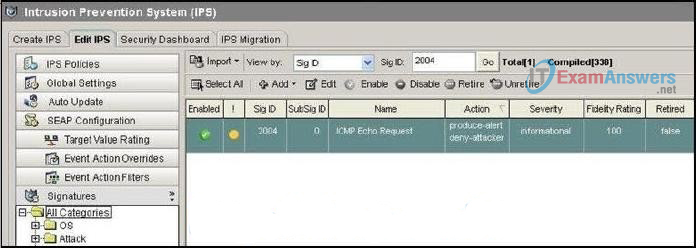
- Reset the TCP connection to terminate the TCP flow.
- Drop the packet and all future packets from thisTCP flow.
- Generatean alarm message that can be sent to a syslog server.
- Drop the packet and permit remaining packets from this TCP flow.
- Create an ACL that denies traffic from the attacker IP address.
51. Which three switch security commands are required to enable port security on a portso that it will dynamically learn a single MAC address and disable the port if a host with any other MAC address is connected? (Choose three.)
- switchport mode access
- switchport mode trunk
- switchportport-security
- switchport port-security maximum 2
- switchportport-security mac-address sticky
- switchport port-security mac-addressmac-address
52. Which statement describes the SDM Security Audit wizard?
- After the wizard identifies the vulnerabilities, theSDM One-Step Lockdown feature must be used to make all security-relatedconfiguration changes.
- After the wizardidentifies the vulnerabilities, it automatically makes all security-relatedconfiguration changes.
- The wizard autosenses the inside trusted and outside untrusted interfaces todetermine possible security problems that might exist.
- The wizard is based on the Cisco IOS AutoSecure feature.
- The wizard is enabled using the Intrusion Prevention task.
53. Which component of AAA is used to determine which resources a user can access and which operations the user is allowed to perform?
- Auditing
- accounting
- authorization
- authentication
54. Which two protocols allow SDM to gather IPS alertsfrom a Cisco ISR router? (Choose two.)
- FTP
- HTTPS
- SDEE
- SSH
- Syslog
- TFTP
55. Refer to the exhibit. Which AAA command logs the activity of a PPP session?
- aaa accounting connection start-stop group radius
- aaa accounting connection start-stop group tacacs+
- aaa accounting exec start-stop group radius
- aaa accounting exec start-stop group tacacs+
- aaa accounting network start-stop group radius
- aaa accounting network start-stop group tacacs+
56. What is a feature of the TACACS+ protocol?
- It combines authentication and authorization as one process.
- It encrypts the entire body of the packet for more secure communications.
- It utilizes UDP to provide more efficient packet transfer.
- It hides passwords during transmission using PAP and sends the rest of the packet in plain text.
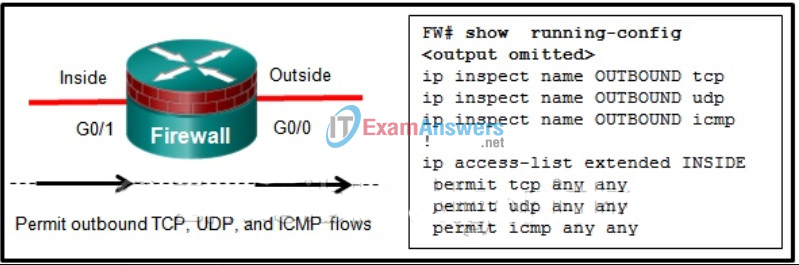
57. Refer to the exhibit. Which interface configuration completes the CBACconfiguration on router R1?
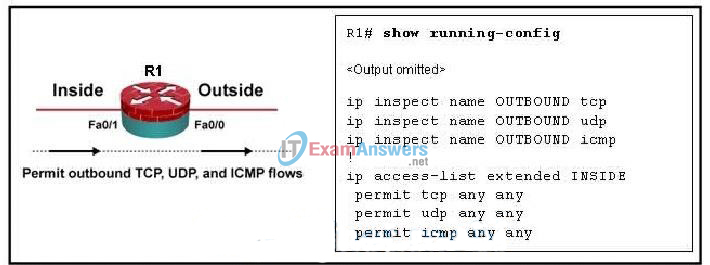
- R1(config)# interface fa0/0
R1(config-if)# ip inspect INSIDE in
R1(config-if)# ip access-group OUTBOUND in - R1(config)# interface fa0/1
R1(config-if)# ip inspect INSIDE in
R1(config-if)# ip access-group OUTBOUND in - R1(config)# interface fa0/1
R1(config-if)# ip inspect OUTBOUND in
R1(config-if)# ip access-group INSIDE out - R1(config)# interface fa0/0
R1(config-if)# ip inspect OUTBOUND in
R1(config-if)# ip access-group INSIDE in - R1(config)#interface fa0/1
R1(config-if)# ip inspect OUTBOUND in
R1(config-if)#ip access-group INSIDE in
58. Refer to the exhibit. Which Cisco IOS security feature is implemented onrouter R2?
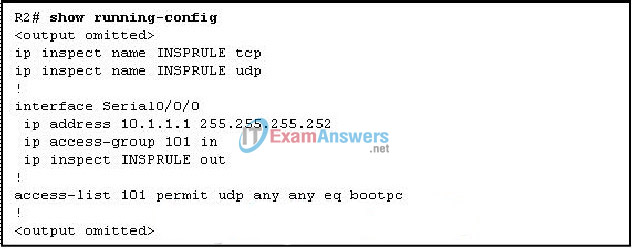
- CBAC firewall
- reflexive ACL firewall
- zone-based policy firewall
- AAA access control firewall
59. Which Cisco IOS privileged EXEC command can be used to verify that theCisco IOS image and configuration files have been properly backed up and secured?
- Router# dir
- Router# show archive
- Router# show secure bootset
- Router# show flash
60. Which device supports the use of SPAN to enable monitoring of malicious activity?
- Cisco NAC
- Cisco IronPort
- Cisco Security Agent
- Cisco Catalyst switch
61. Which three statements describe zone-based policy firewall rules that govern interface behavior and the traffic moving between zone member interfaces? (Choose three.)
- An interface can be assigned to multiple security zones.
- Interfaces can be assigned to a zone before the zone is created.
- Pass, inspect, and drop options can only be applied between two zones.
- If traffic is to flow between all interfaces in a router, each interface must be a member of a zone.
- Traffic is implicitly prevented from flowing by default among interfaces that are members of the same zone.
- To permit traffic to and from a zone member interface, a policy allowing or inspecting traffic must be configured between that zone and any other zone.
62. Refer to the exhibit. Based on the SDM screen shown, which twoconclusions can be drawn about the IKE policy being configured? (Choose two.)

- It will use digital certificates for authentication.
- It will use apredefined key for authentication.
- It will use a very strong encryption algorithm.
- It will be the default policy with the highest priority.
63. The use of 3DES within the IPsec framework is anexample of which of the five IPsec building blocks?
- authentication
- confidentiality
- Diffie-Hellman
- integrity
- nonrepudiation
64. Which statement describes the operation of the IKE protocol?
- It uses IPsec to establish the key exchange process.
- It uses sophisticated hashing algorithms to transmit keys directly across a network.
- It calculates shared keys based on the exchange of a series of data packets.
- It uses TCP port 50 to exchange IKE information between the security gateways
65. Which three types of views are available when configuring the Role-BasedCLI Access feature? (Choose three.)
- superuser view
- root view
- superview
- CLI view
- admin view
- config view
66. Which statement describes a MAC address table overflow attack?
- An attacker alters the MAC address in a frame to match the address of a target host.
- Frames flood the LAN, creating excessive traffic and degrading network performance.
- The attacking host broadcasts STP configuration and topology change BPDUs to force spanning-tree recalculations.
- A software tool floods a switch with frames containing randomly generated source and destination MAC and IP addresses.
67. When configuring a class map for zone-based policy firewall, how are the match criteria applied when using the match-all parameter?
- Traffic must match all of the match criteria specified in the statement.
- Traffic must match the first criteria in the statement.
- Traffic must match at least one of the match criteria statements.
- Traffic must match according to an exclusive disjunction criteria.
68. Which algorithm is used to automatically generate a shared secret for two systems to use in establishing an IPsec VPN?
- DES
- DH
- 3DES
- ESP
- AH
- SSL
69. What is an important difference between network-based and host-based intrusion prevention?
- Host-based IPS is more scalable than network-based IPS.
- Host-based IPS can work in promiscuous mode or inline mode.
- Network-based IPS is better suited for inspection of SSL and TLS encrypted dataflows.
- Network-based IPS provides better protection against OS kernel-level attacks on hosts and servers.
- Network-basedIPS can provide protection to hosts without the need of installing specialized software on each one.
70. Refer to the exhibit. Based on the output from the show secure bootset command on router R1, which three conclusions can be drawn regarding Cisco IOS Resilience? (Choose three.)
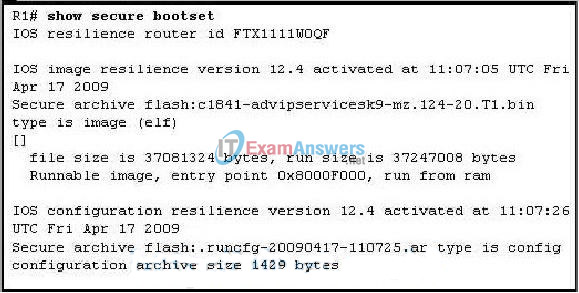
- A copy of the Cisco IOS image file has been made.
- A copy of the router configuration file has been made.
- The Cisco IOS image file is hidden and cannot be copied, modified, or deleted.
- The Cisco IOS image filename will be listed when the show flash command isissued on R1.
- The copy tftp flash command was issued on R1.
- The secure boot-config command was issued on R1.
71. Which element ofthe Cisco Threat Control and Containment solution defends against attempts toattack servers by exploiting application and operating system vulnerabilities?
- threat control for email
- threat control for endpoints
- threat controlfor infrastructure
- threat control for systems
72. Refer to the exhibit. Based on the SDM NTP Server Details screen, which two conclusions can be drawn from the information entered and check boxes checked? (Choose two.)
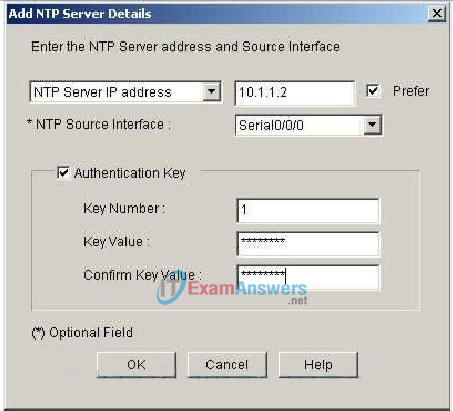
- NTPv1 is being configured.
- The IP address of the NTP server is 10.1.1.2.
- The IP address of the NTP client is 10.1.1.2.
- NTP messages will be sent and received on interface Serial0/0/0 for this router.
- NTP routing updates will be sent and received on interface Serial0/0/0 of the NTP server.
73. Which two statements match a type of attack with an appropriate example?(Choose two.)
- To conduct an access attack, an attacker uses L0phtCrack to obtain a Windows server password.
- To conduct an access attack, an attacker uses Wireshark to capture interesting network traffic.
- To conduct a reconnaissance attack, an attacker initiates a ping of death attack to a targeted server.
- To conduct a DoS attack, an attacker uses handler systems and zombies to obtain a Windows server password.
- To conducta DoS attack, an attacker initiates a smurf attack by sending a large number ofICMP requests to directed broadcast addresses.
- To conduct a reconnaissance attack, an attacker creates a TCP SYN flood causing the server to spawn many half-open connections and become unresponsive.
74. The use of which two options are required for IPsec operation? (Choose two.)
- AH protocols for encryption and authentication
- Diffie-Hellmanto establish a shared-secret key
- IKE to negotiate the SA
- PKI for pre-shared-key authentication
- SHA for encryption
75. Which three security services are provided by digital signatures? (Choose three.)
- authenticatesthe source
- authenticates the destination
- guarantees data has not changed in transit
- provides nonrepudiation of transactions
- provides nonrepudiation using HMAC functions
- provides confidentiality of digitally signed data
76. Which three statements should be considered when applying ACLs to a Cisco router? (Choose three.)
- Place generic ACL entries at the top of the ACL.
- Place more specific ACL entries at the top of the ACL.
- Router-generated packets pass through ACLs on the router without filtering.
- ACLs always search for the most specific entry before taking any filtering action.
- A maximum of three IP access lists can be assigned to an interface perdirection (in or out).
- An access list applied to any interface without a configured ACL allows all traffic to pass.
77. Which consideration is important when implementing syslog in a network?
- Enable the highest level of syslog available to ensure logging of all possible event messages.
- Log all messages to the system buffer so that they can be displayed when accessing the router.
- Synchronize clocks on all network devices with a protocol such as Network Time Protocol.
- Use SSH to access syslog information.
78. When logging is enabled for an ACL entry, how does the router switch packets filtered by the ACL?
- topology-based switching
- autonomous switching
- process switching
- optimum switching
79. Which statement is true about the One-Step lockdown feature of the CCP Security Audit wizard?
- It enables the Secure Copy Protocol (SCP).
- It supports AAA configuration.
- It enables TCP intercepts.
- It sets an access class ACL on vty lines.
- It provides an option for configuring SNMPv3 on all routers.
80. Refer to the exhibit. The administrator can ping the S0/0/1 interface of RouterB but is unable to gain Telnet access to the router using the password cisco123. What is a possible cause of the problem?
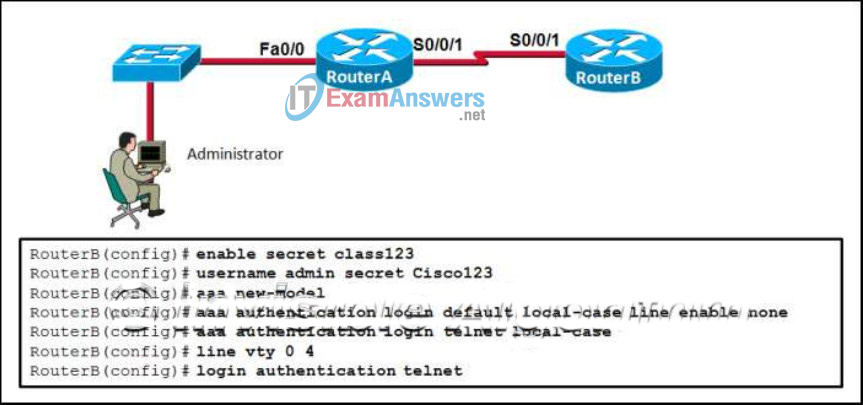
- The Telnet connection between RouterA and RouterB is not working correctly.
- The password cisco123 is wrong.
- The enable password and the Telnet password need to be the same.
- The administrator does not have enough rights on the PC that is being used.
81. If a switch is configured with the storm-control command and the action shutdown and action trap parameters, which two actions does the switch take when a storm occurs on a port? (Choose two.)
- The port is disabled.
- The switch is rebooted.
- An SNMP log message is sent.
- The port is placed in a blocking state.
- The switch forwards control traffic only.
82. Why does a worm pose a greater threat than a virus poses?
- Worms run within a host program.
- Worms are not detected by antivirus programs.
- Worms directly attack the network devices.
- Worms are more network-based than viruses are.
83. Which type of encryption algorithm uses public and private keys to provide authentication, integrity, and confidentiality?
- IPsec
- symmetric
- asymmetric
- shared secret
84. Which two configuration requirements are needed for remote access VPNs using Cisco Easy VPN Server, but are not required for site-to-site VPNs? (Choose two.)
- group policy lookup
- IPsec translations
- virtual template interface
- IKE policies
- transform sets
85. What can be used as a VPN gateway when setting up a site-to-site VPN?
- Cisco Catalyst switch
- Cisco router
- Cisco Unified Communications Manager
- Cisco AnyConnect
86. What is a characteristic of AAA accounting?
- Accounting can only be enabled for network connections.
- Users are not required to be authenticated before AAA accounting logs their activities on the network.
- Possible triggers for the aaa accounting exec default command include start-stop and stop-only.
- Accounting is concerned with allowing and disallowing authenticated users access to certain areas and programs on the network.
87. When configuring a site-to-site IPsec VPN using the CLI, the authentication pre-share command is configured in the ISAKMP policy. Which additional peer authentication configuration is required?
- Configure the message encryption algorithm with the encryptiontype ISAKMP policy configuration command.
- Configure the DH group identifier with the groupnumber ISAKMP policy configuration command.
- Configure a hostname with the crypto isakmp identity hostname global configuration command.
- Configure a PSK with the crypto isakmp key global configuration command.
88. What are three characteristics of the ASA routed mode? (Choose three.)
- This mode does not support VPNs, QoS, or DHCP Relay.
- The interfaces of the ASA separate Layer 3 networks and require different IP addresses in different subnets.
- It is the traditional firewall deployment mode.
- NAT can be implemented between connected networks.
- This mode is referred to as a “bump in the wire.”
- In this mode, the ASA is invisible to an attacker.
89. Which authentication method is available when specifying a method list for group policy lookup using the CCP Easy VPN Server wizard?
- Active Directory
- Kerberos
- Certificate Authority
- RADIUS
- TACACS+
90. Refer to the exhibit. What conclusion can be drawn from the exhibited window when it is displayed on a remote user computer screen?
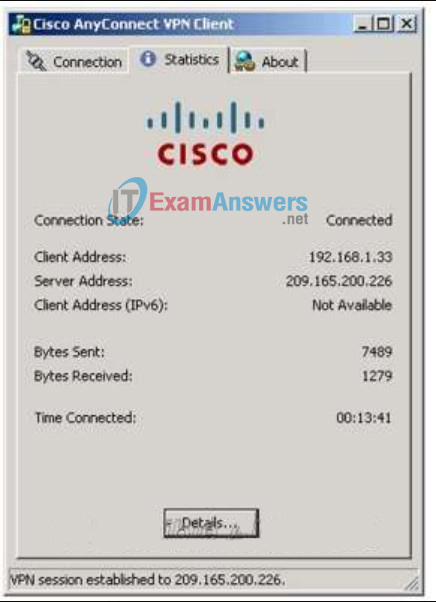
- The user has connected to a secure web server.
- The user has established a client-based VPN connection.
- The user has logged out of the AnyConnect VPN client.
- The user is installing the AnyConnect VPN client.
- The user is using a web browser to connect to a clientless SSL VPN.
91. Which type of IPS signature detection is used to distract and confuse attackers?
- pattern-based detection
- anomaly-based detection
- policy-based detection
- honey pot-based detection
92. Which attack allows the attacker to see all frames on a broadcast network by causing a switch to flood all incoming traffic?
- LAN storm
- VLAN hopping
- STP manipulation
- MAC table overflow
- 802.1q double tagging
93. Refer to the exhibit. The indicated window has appeared in the web browser of a remote user. What is the cause of this message?
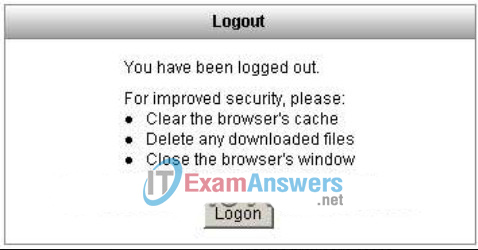
- The user has timed out of an AnyConnect SSL VPN installation.
- The user has logged out of a clientless SSL VPN session.
- The user has logged out of a Cisco VPN Client session.
- The user has logged out of an AnyConnect IPsec VPN session.
- The user has logged out of an AnyConnect SSL VPN session.
94. An administrator has been asked to configure basic access security on a router, including creating secure passwords and disabling unattended connections. Which three actions accomplish this using recommended security practices? (Choose three.)
- Create passwords with only alphanumeric characters.
- Set the minimum password length to 10 characters.
- Set the executive timeout parameters on the console port to 120 and 0.
- Set the executive timeout parameters on the vty lines to 3 and 0.
- Enable the password encryption service for the router.
- Enable login using the Aux port with the executive timeout set to 0 and 0.
95. Which type of intrusion prevention technology is primarily used by Cisco IPS security appliances?
- rule-based
- profile-based
- signature-based
- NetFlow anomaly-based
- protocol analysis-based
96. Which type of packets exiting the network of an organization should be blocked by an ACL?
- packets that are not encrypted
- packets that are not translated with NAT
- packets with source IP addresses outside of the organization’s network address space
- packets with destination IP addresses outside of the organization’s network address space
97. An administrator wants to prevent a rogue Layer 2 device from intercepting traffic from multiple VLANs on a network. Which two actions help mitigate this type of activity? (Choose two.)
- Disable DTP on ports that require trunking.
- Place unused active ports in an unused VLAN.
- Secure the native VLAN, VLAN 1, with encryption.
- Set the native VLAN on the trunk ports to an unused VLAN.
- Turn off trunking on all trunk ports and manually configure each VLAN as required on each port.
98. Which command would an administrator use to clear generated crypto keys?
- Router(config)# crypto key decrypt
- Router(config-line)# transport input ssh clear
- Router(config)# crypto key rsa
- Router(config)# crypto key zeroize rsa
99. Refer to the exhibit. An administrator has configured an ASA 5505 as indicated but is still unable to ping the inside interface from an inside host. What is the cause of this problem?
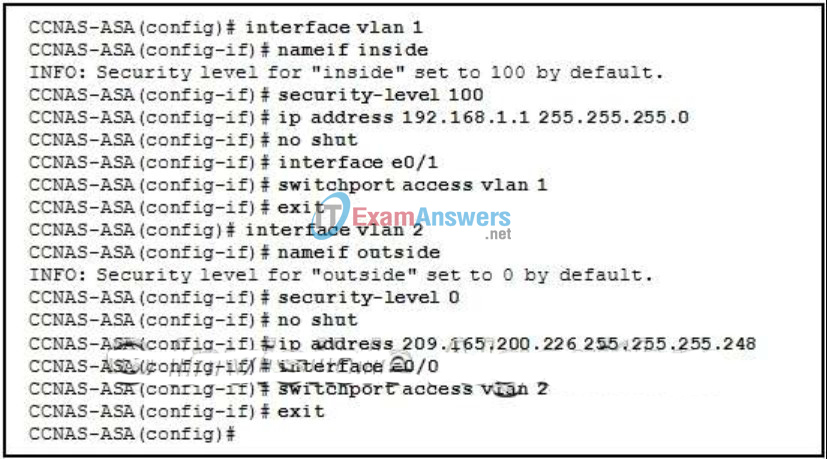
- An IP address should be configured on the Ethernet 0/0 and 0/1 interfaces.
- The no shutdown command should be entered on interface Ethernet 0/1.
- The security level of the inside interface should be 0 and the outside interface should be 100.
- VLAN 1 should be assigned to interface Ethernet 0/0 and VLAN 2 to Ethernet 0/1.
- VLAN 1 should be the outside interface and VLAN 2 should be the inside interface.
100. Which two commands are needed on every IPv6 ACL to allow IPv6 neighbor discovery? (Choose two.)
- permit tcp any any ack
- permit icmp any any nd-na
- permit icmp any any echo-reply
- permit icmp any any nd-ns
- permit ipv6 any any fragments
- permit ipv6 any any routing
101. Which technology does CCP require for configuring remote access VPN support with the Easy VPN Server wizard?
- AutoSecure
- Role-Based CLI Access
- AAA
- port forwarding
102. What are three goals of a port scan attack? (Choose three.)
- disable used ports and services
- determine potential vulnerabilities
- identify active services
- identify peripheral configurations
- identify operating systems
- discover system passwords
103. Refer to the exhibit. An administrator is implementing VPN support on an ASA 5505. What type of VPN support is being implemented?
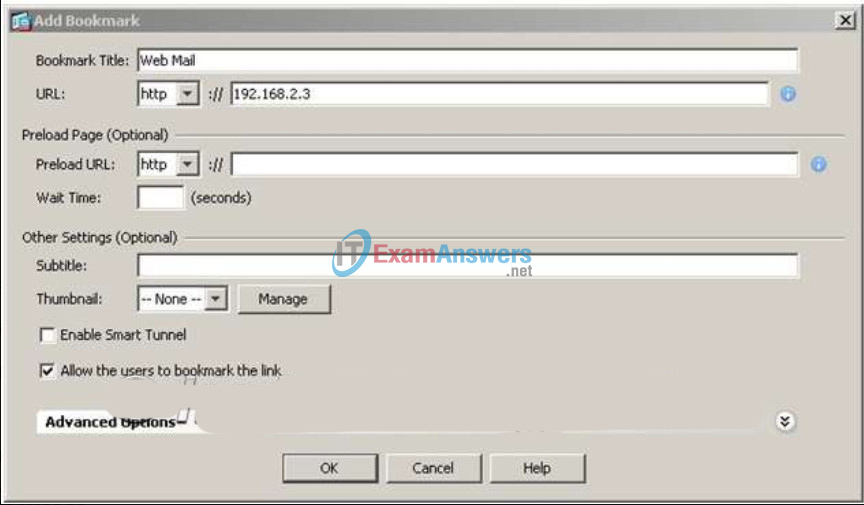
- client-based IPsec VPN using Cisco VPN Client
- client-based IPsec VPN using AnyConnect
- client-based SSL VPN using AnyConnect
- clientless IPsec VPN
- clientless SSL VPN
- site-to-site IPsec VPN
104. Which type of VPN may require the Cisco VPN Client software?
- remote access VPN
- SSL VPN
- site-to-site VPN
- MPLS VPN
105. Sales representatives of an organization use computers in hotel business centers to occasionally access corporate e-mail and the inventory database. What would be the best VPN solution to implement on an ASA to support these users?
- client-based IPsec VPN using Cisco VPN Client
- client-based IPsec VPN using AnyConnect
- client-based SSL VPN using AnyConnect
- clientless IPsec VPN using a web browser
- clientless SSL VPN using a web browser
- site-to-site IPsec VPN
106. What must be configured before any Role-Based CLI views can be created?
- aaa new-model command
- multiple privilege levels
- secret password for the root user
- usernames and passwords
107. Refer to the exhibit. Which option tab on the CCP screen is used to view the Top Threats table and deploy signatures associated with those threats?
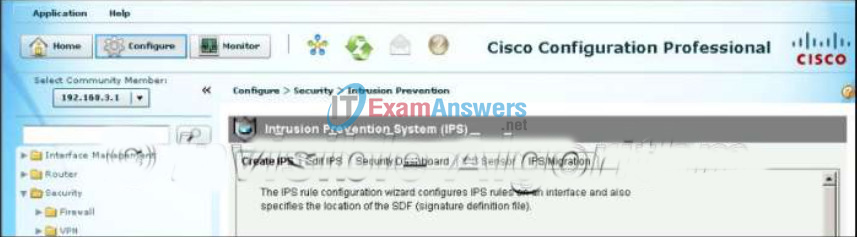
- Create IPS
- Edit IPS
- Security Dashboard
- IPS Sensor
- IPS Migration
108. Which statement correctly describes a type of filtering firewall?
- A transparent firewall is typically implemented on a PC or server with firewall software running on it.
- A packet-filtering firewall expands the number of IP addresses available and hides network addressing design.
- An application gateway firewall (proxy firewall) is typically implemented on a router to filter Layer 3 and Layer 4 information.
- A stateful firewall monitors the state of connections, whether the connection is in an initiation, data transfer, or termination state.
109. With the Cisco AnyConnect VPN wizard, which two protocols can be used for tunnel group configuration? (Choose two.)
- MPLS
- SSH
- PPTP
- ESP
- IPsec
110. What are two benefits of an SSL VPN? (Choose two.)
- The thin client mode functions without requiring any downloads or software.
- It supports all client/server applications.
- It is compatible with DMVPNs, Cisco IOS Firewall, IPsec, IPS, Cisco Easy VPN, and NAT.
- It has the option of only requiring an SSL-enabled web browser.
- It supports the same level of cryptographic security as an IPsec VPN.
111. Refer to the exhibit. A network administrator is configuring the security level for the ASA. Which statement describes the default result if the administrator tries to assign the Inside interface with the same security level as the DMZ interface?
- The ASA console will display an error message.
- The ASA will not allow traffic in either direction between the Inside interface and the DMZ.
- The ASA allows traffic from the Inside to the DMZ, but blocks traffic initiated on the DMZ to the Inside interface.
- The ASA allows inbound traffic initiated on the Internet to the DMZ, but not to the Inside interface.
112. What is an advantage of using SSL VPNs compared to IPsec VPNs on an ASA?
- SSL VPNs provide support for more applications.
- SSL VPNs do not require any pre-installed client software.
- SSL VPNs provide superior authentication.
- SSL VPNs provide stronger encryption as a remote-access solution.
113. Refer to the exhibit. Which interface configuration completes the classic firewall configuration on the firewall?
- FW(config)# interface g0/1
FW(config-if)# ip inspect OUTBOUND in
FW(config-if)# ip access-group INSIDE out - FW(config)# interface g0/1
FW(config-if)# ip inspect OUTBOUND in
FW(config-if)# ip access-group INSIDE in - FW(config)# interface g0/0
FW(config-if)# ip inspect OUTBOUND in
FW(config-if)# ip access-group INSIDE in - FW(config)# interface g0/0
FW(config-if)# ip inspect INSIDE in
FW(config-if)# ip access-group OUTBOUND in - FW(config)# interface g0/1
FW(config-if)# ip inspect INSIDE in
FW(config-if)# ip access-group OUTBOUND in
114. What is a type of SSL VPN that provides access to a network without requiring VPN software or a Java applet on the client?
- clientless mode
- Cisco VPN client mode
- full client mode
- thin client mode
115. What are two reasons for a company to migrate from a classic firewall to the ZPF model? (Choose two.)
- The classic firewall will perform the same inspection on all traffic that goes through a specific interface.
- The classic firewall can only have one policy that affects any given traffic.
- The classic firewall security posture is to block unless explicitly allowed.
- The classic firewall is limited to two interfaces.
- The classic firewall relies heavily on ACLs.
116. What is the main difference between the implementation of IDS and IPS devices?
- An IDS uses signature-based technology to detect malicious packets, whereas an IPS uses profile-based technology.
- An IDS would allow malicious traffic to pass before it is addressed, whereas an IPS stops it immediately.
- An IDS can negatively impact the packet flow, whereas an IPS can not.
- An IDS needs to be deployed together with a firewall device, whereas an IPS can replace a firewall.
117. What information must an IPS track in order to detect attacks matching a composite signature?
- the state of packets related to the attack
- the total number of packets in the attack
- the network bandwidth consumed by all packets
- the attacking period used by the attacker
118. What method is used to authenticate SNMPv2 messages between the manager and the agent?
- RSA keys
- trusted keys
- encrypted passwords
- community strings
119. Which statement describes the characteristics of packet-filtering and stateful firewalls as they relate to the OSI model?
- A packet-filtering firewall typically can filter up to the transport layer, whereas a stateful firewall can filter up to the session layer.
- Both stateful and packet-filtering firewalls can filter at the application layer.
- A packet-filtering firewall uses session layer information to track the state of a connection, whereas a stateful firewall uses application layer information to track the state of a connection.
- A stateful firewall can filter application layer information, whereas a packet-filtering firewall cannot filter beyond the network layer.
120. What is a difference between ASA IPv4 ACLs and IOS IPv4 ACLs?
- ASA ACLs use the subnet mask in defining a network, whereas IOS ACLs use the wildcard mask.
- ASA ACLs do not have an implicit deny all at the end, whereas IOS ACLs do.
- ASA ACLs use forward and drop ACEs, whereas IOS ACLs use permit and deny ACEs.
- Multiple ASA ACLs can be applied on an interface in the ingress direction, whereas only one IOS ACL can be applied.
- ASA ACLs are always named, whereas IOS ACLs can be named or numbered.
121. What is the best way to prevent a VLAN hopping attack?
- Use ISL encapsulation on all trunk links.
- Disable STP on all nontrunk ports.
- Disable trunk negotiation for trunk ports and statically set nontrunk ports as access ports.
- Use VLAN 1 as the native VLAN on trunk ports.
122. Why have corporations been shifting remote access security policies to include support for ASA SSL VPNs?
- to have stronger encryption options
- to support secure access for users on a multitude of devices
- to have stronger authentication options
- to provide stronger overall security
123. Refer to the exhibit. What is the purpose of the object group-based ACL?
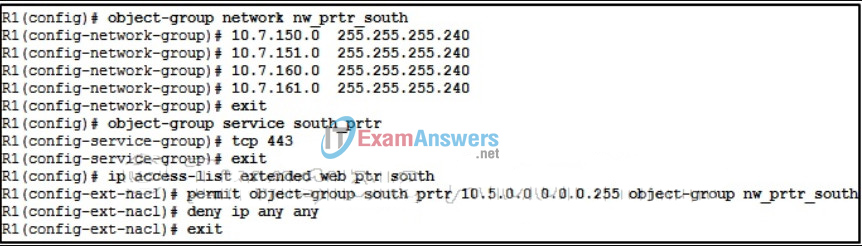
- It allows users on the 10.5.0.0/24 network access via HTTPS to remote devices on the 10.7.150.0/28, 10.7.151.0/28, 10.7.160.0/28, and 10.7.161.0/28 networks.
- It allows devices on the 10.7.150.0/28, 10.7.151.0/28, 10.7.160.0/28, 10.7.161.0/28 networks to receive TCP-based broadcasts.
- It allows any TCP traffic with port 443 from the 10.7.150.0/28, 10.7.151.0/28, 10.7.160.0/28, and 10.7.161.0/28 networks access to the 10.5.0.0/24 network.
- It allows devices on the 10.5.0.0/24 network to have telnet and web access to the 10.7.150.0/28, 10.7.151.0/28, 10.7.160.0/28, and 10.7.161.0/28 networks.
124. How would a network security professional mitigate a DoS attack?
- Implement a strong password policy.
- Deploy antisniffer software.
- Include a firewall and IPS in the network security design.
- Design the network by using the principle of minimum trust.
125. What type of security key is generated by the local user software when a user is connecting to a Cisco ASA through a remote-access SSL VPN?
- asymmetric key
- digitally signed private key
- shared-secret key
- digitally signed public key
126. What is one advantage of using a Cisco ASA for remote networking VPN deployment compared to a Cisco ISR?
- support for SSL VPNs
- support for more concurrent user sessions
- support for IPsec VPNs
- support for AAA external authentication
127. In what two phases of the system development life cycle does risk assessment take place? (Choose two.)
- operation and maintenance
- disposition
- implementation
- initiation
- acquisition and development
128. What is one benefit of implementing a secure email service by using the Cisco Email Security Appliance (ESA)?
- ESA provides isolation between processes.
- It obtains real-time updates from the Cisco SIO.
- It uses the network infrastructure to enforce security policy compliance.
- It combines advanced threat defense and secure mobility for email.
129. A network administrator configures the alert generation of an IPS device in such a way that when multiple attack packets that match the same signature are detected, a single alert for the first packet is generated and the remaining duplicate alarms are counted, but not sent, for a specific time period. When the specified time period is reached, an alert is sent that indicates the number of alarms that occurred during the time interval. What kind of alert generation pattern is configured?
- composite alerts
- atomic alerts
- summary alerts
- advanced alerts
130. Which STP port type is permitted to forward traffic, but is not the port closest to the root bridge?
- root port
- designated port
- backup port
- alternate port
131. Refer to the exhibit. What is the purpose of the ACLs?
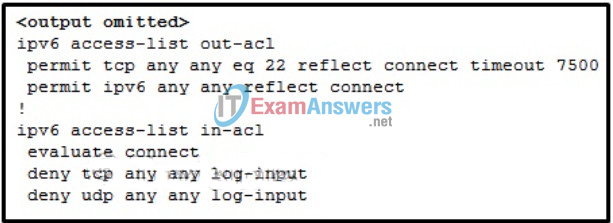
- to deny inbound IPv6 and SSH traffic unless it originates from within the organization
- to allow inbound traffic from only designated sources
- to allow SSH connections initiated from the Internet to enter the network
- to deny all inbound traffic and log TCP and UDP transmissions
132. What is the basic method used by 3DES to encrypt plaintext?
- The data is divided into three blocks of equal length for encryption.
- The data is encrypted using a key length that is three times longer than the key used for DES.
- The data is encrypted three times with three different keys.
- The data is encrypted, decrypted, and encrypted using three different keys.
133. Refer to the exhibit. A network administrator configures AAA authentication on R1. The administrator then tests the configuration by telneting to R1. The ACS servers are configured and running. What will happen if the authentication fails?
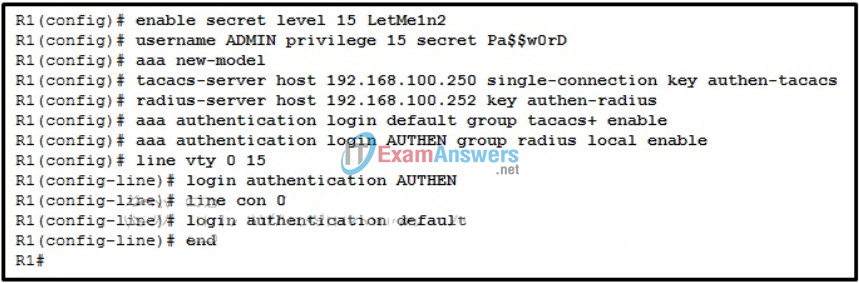
- The enable secret password could be used in the next login attempt.
- The authentication process stops.
- The enable secret password and a random username could be used in the next login attempt.
- The username and password of the local user database could be used in the next login attempt.
134. Which two security features can cause a switch port to become error-disabled? (Choose two.)
- storm control with the trap option
- PortFast with BPDU guard enabled
- port security with the shutdown violation mode
- root guard
- protected ports
135. Which security policy component would contain procedures for handling an issue where someone followed a network administrator into the server room without the administrator noticing and the person removed some storage drives?
- information preservation policy
- security policy
- operations and maintenance document
- security initiation document
136. What question is answered by the risk analysis component of security policy development?
- What is the cost versus benefit analysis of implementing various security technologies?
- What are the reliable, well-understood, and recommended security practices that similar organizations currently employ?
- What are the current procedures for incident response, monitoring, maintenance, and auditing of the system for compliance?
- What are the most likely types of threats given the purpose of the organization?
137. What are two characteristics of an acceptable use policy? (Choose two.)
- It should be as explicit as possible to avoid misunderstanding.
- It should specify who is authorized to access network resources.
- It should identify how remote users will access the network.
- It should identify what network applications and usages are acceptable.
- It should enforce minimum password requirements for users.
- It should be vague to allow maximum user flexibility.
138. Refer to the exhibit. Which pair of crypto isakmp key commands would correctly configure PSK on the two routers?
- R1# crypto isakmp key ciscopass address 209.165.200.226
R2# crypto isakmp key secure address 209.165.200.227 - R1# crypto isakmp key ciscopass address 209.165.200.227
R2# crypto isakmp key ciscopass address 209.165.200.226 - R1# crypto isakmp key ciscopass hostname R1
R2# crypto isakmp key ciscopass hostname R2 - R1# crypto isakmp key ciscopass address 209.165.200.226
R2# crypto isakmp key ciscopass address 209.165.200.227
139. What are two features of Cisco Easy VPN Server? (Choose two.)
- It requires Cisco routers to act as remote VPN clients.
- It enables complete access to the corporate network over an SSL VPN tunnel.
- It enables an ASA firewall to act as the VPN head-end device in remote-access VPNs.
- It requires remote access to the corporate network via a web browser and SSL.
- Cisco Easy VPN Server enables VPN client remote access to a company intranet through creation of secure IPsec tunnels.
140. Refer to the exhibit. A network administrator is troubleshooting a GRE VPN tunnel between R1 and R2. Assuming the R2 GRE configuration is correct and based on the running configuration of R1, what must the administrator do to fix the problem?
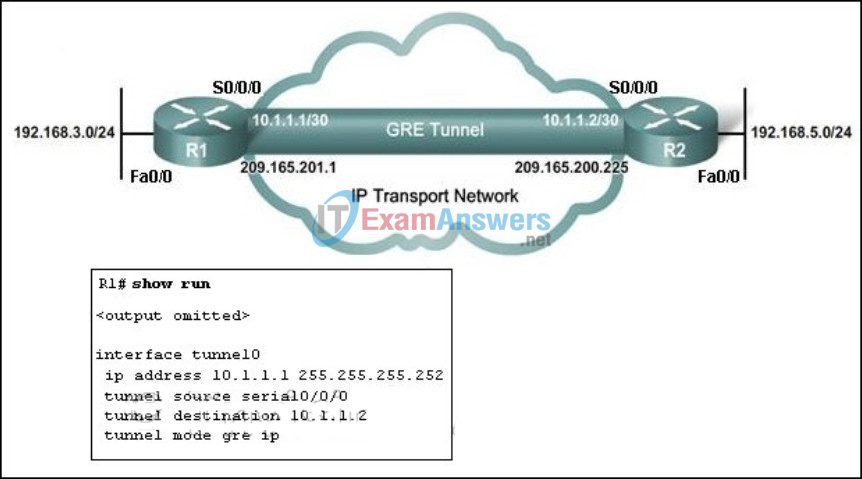
- Change the tunnel IP address to 209.165.201.1.
- Change the tunnel destination to 192.168.5.1.
- Change the tunnel IP address to 192.168.3.1.
- Change the tunnel source interface to Fa0/0.
- Change the tunnel destination to 209.165.200.225.
141. Which spanning-tree enhancement prevents the spanning-tree topology from changing by blocking a port that receives a superior BPDU?
- PortFast
- BPDU guard
- root guard
- BDPU filter
142. In deploying an IPS in a corporate network, system operators first create a profile of normal network operation by monitoring network activities in normal network uses. After the profile is incorporated into the IPS triggering mechanism, alarms will be generated when the IPS detects excessive activity that is beyond the scope of the profile. Which signature detection mechanism is deployed?
- pattern-based detection
- policy-based detection
- honey pot-based detection
- anomaly-based detection
143. Which security feature would be commonly implemented as part of a large enterprise wireless policy but would not typically be used in a small office/home office network?
- not broadcasting the SSID
- using WPA2
- not allowing personal wireless devices
- using an authentication server
144. A network technician has been asked to design a virtual private network between two branch routers. Which type of cryptographic key should be used in this scenario?
- asymmetric key
- hash key
- symmetric key
- digital signature
145. A company is designing its strategy of deploying Cisco Secure ACS to manage user access. The company is currently using a Windows server for the internal authentication service. The network administrator needs to configure the ACS to contact the Windows server when it cannot find the user in its local database. Which option of external user database setup should be configured on ACS?
- by specific user assignment
- by unknown user policy
- by administrator privilege
- by user priority
146. Refer to the exhibit. What is the purpose of the highlighted inspect line?
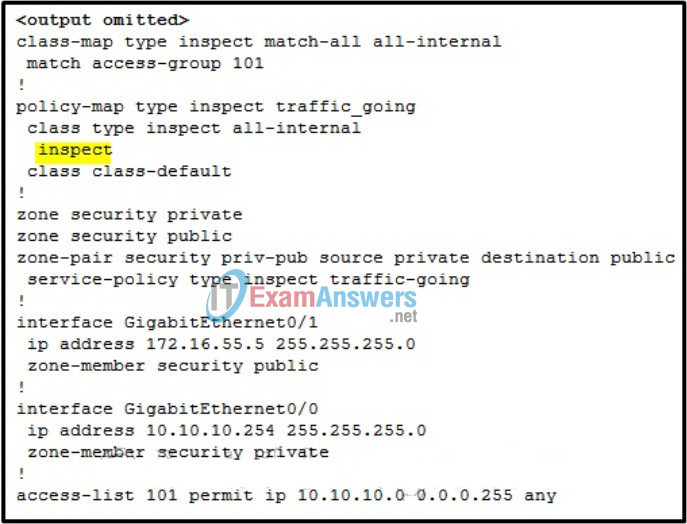
- It is the action to take on the traffic from the 10.10.10.0/24 network. [Rahul and Zepo]
- It specifies the named class-map to apply to the traffic_going policy.
- It dictates to the firewall to track all outgoing sessions no matter the source in order to determine whether a return packet is allowed. [Dimented]
- It is the command used to apply a rate limit to a specific class of traffic.
147. Which two options are offered through the Cisco TrustSec Solution for enterprise networks? (Choose two.)
- Easy VPN solution
- IPsec VPN solution
- 802.1X-Based Infrastructure solution
- NAC Appliance-Based Overlay solution
- Firewall and IDS integrated solution
148. Which statement accurately describes Cisco IOS zone-based policy firewall operation?
- Router management interfaces must be manually assigned to the self zone.
- A router interface can belong to multiple zones.
- The pass action works in only one direction.
- Service policies are applied in interface configuration mode.
149. Two devices that are connected to the same switch need to be totally isolated from one another. Which Cisco switch security feature will provide this isolation?
- DTP
- BPDU guard
- PVLAN Edge
- SPAN
150. Why is a reflexive ACL harder to spoof compared to an extended ACL that uses the established keyword?
- It provides a secure tunnel for returning traffic.
- A reflexive ACL provides a lock-and-key function.
- It allows incoming packets only after the 3-way handshake is completed.
- It provides more detailed filter criteria to match an incoming packet before the packet is allowed through.
151. Which security feature helps protect a VoIP system from SPIT attacks?
- AES
- BPDU guard
- WPA2
- authenticated TLS
152. What are two protocols that are used by AAA to authenticate users against a central database of usernames and password? (Choose two.)
- TACACS+
- NTP
- SSH
- RADIUS
- HTTPS
- CHAP
153. Which security organization updates the training material that helps prepare for the Global Information Assurance Certification (GIAC)?
- CERT
- CIS
- SANS
- (ISC)2
154. Which three wizards are included in Cisco ASDM 6.4? (Choose three.)
- ADSL Connection wizard
- Advanced Firewall wizard
- High Availability and Scalability wizard
- Security Audit wizard
- Startup wizard
- VPN wizard
155. Refer to the exhibit. What will be displayed in the output of the show running-config object command after the exhibited configuration commands are entered on an ASA 5505?
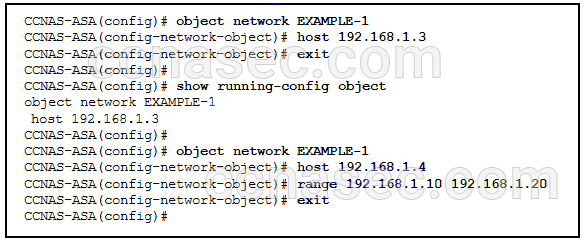
- host 192.168.1.3
- range 192.168.1.10 192.168.1.20
- host 192.168.1.4 and range 192.168.1.10 192.168.1.20
- host 192.168.1.3 and host 192.168.1.4
- host 192.168.1.4
- host 192.168.1.3, host 192.168.1.4, and range 192.168.1.10 192.168.1.20
156. Refer to the exhibit. According to the command output, which three statements are true about the DHCP options entered on the ASA 5505? (Choose three.)
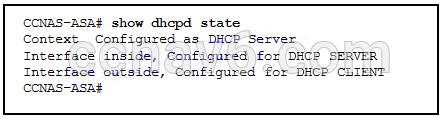
- The dhcpd auto-config outside command was issued to enable the DHCP client.
- The dhcpd enable inside command was issued to enable the DHCP server.
- The dhcpd address [start-of-pool]-[end-of-pool] inside command was issued to enable the DHCP client.
- The dhcpd auto-config outside command was issued to enable the DHCP server.
- The dhcpd enable inside command was issued to enable the DHCP client.
- The dhcpd address [start-of-pool]-[end-of-pool] inside command was issued to enable the DHCP server.
157. Fill in the blank.
In a syslog implementation, a router that generates and forwards syslog messages is known as a syslog clients
158. Which three types of remote access VPNs are supported on ASA devices? (Choose three.)
- Clientless SSL VPN using the Cisco AnyConnect Client
- SSL or IPsec (IKEv2) VPN using the Cisco AnyConnect Client
- IPsec (IKEv1) VPN using a web browser
- SSL or IPsec (IKEv2) VPN using the Cisco VPN Client
- Clientless SSL VPN using a web browser
- IPsec (IKEv1) VPN using the Cisco VPN Client
159. Refer to the exhibit. The network administrator is configuring the port security feature on switch SWC. The administrator issued the command show port-security interface fa 0/2 to verify the configuration. What can be concluded from the output that is shown? (Choose three.)
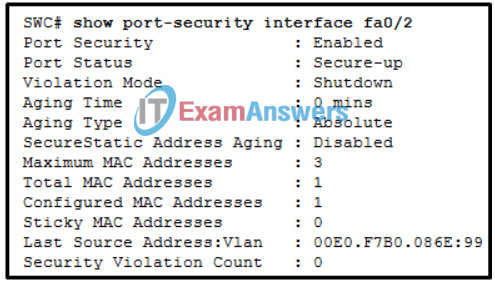
- The switch port mode for this interface is access mode.
- The port is configured as a trunk link.
- Three security violations have been detected on this interface.
- This port is currently up.
- Security violations will cause this port to shut down immediately.
- There is no device currently connected to this port.
160. What is an advantage of using CCP rather than the CLI to configure an ACL?
- IPsec is supported.
- CCP applies the read-only quality to manually created access rules so that accidental modification cannot be made.
- CCP automatically applies a rule to the interface or zone most appropriate.
- Traffic rules do not have to be configured when CCP is being used.
- CCP provides default rules.
161. What is a CLI initiated script that locks down the control plane of a Cisco router in one step?
- Control Plane Protection
- Cisco AutoSecure
- IP Source Guard
- Control Plane Policing
162. What is one way to prevent attackers from eavesdropping on VoIP conversations?
- Use Forced Authorization Codes.
- Implement separate voice VLANs.
- Configure IP phones to use only signed firmware files.
- Create ACLs to allow only VoIP protocols.
163. A large company deploys several network-based IPS sensors for its headquarters network. Which network service configuration will help the process of correlating attack events happening simultaneously in different points of the network?
- Multiple DNS servers with fault tolerance
- Distributed DHCP servers
- A syslog server for each IPS sensor
- A centralized NTP server
164. What is the role of the Cisco NAC Manager in implementing a secure networking infrastructure?
- to assess and enforce security policy compliance in the NAC environment
- to perform deep inspection of device security profiles
- to provide post-connection monitoring of all endpoint devices
- to define role-based user access and endpoint security policies
165. What command must be issued to enable login enhancements on a Cisco router?
- privilege exec level
- banner motd
- login delay
- login block-for
166. Refer to the exhibit. An administrator creates three zones (A, B, and C) in an ASA that filters traffic. Traffic originating from Zone A going to Zone C is denied, and traffic originating from Zone B going to Zone C is denied. What is a possible scenario for Zones A, B, and C?
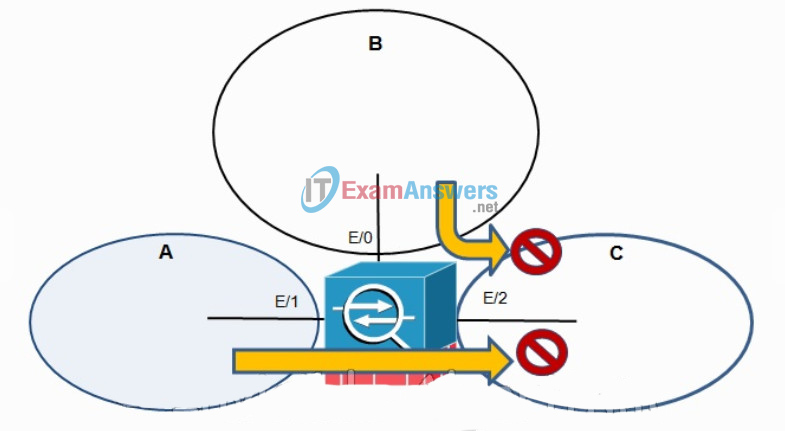
- A – DMZ, B – Inside, C – Outside
- A – DMZ, B – Outside, C – Inside
- A – Inside, B – DMZ, C – Outside
- A – Outside, B – Inside, C – DMZ
167. In a corporate network where SAN is deployed, what happens if the SAN fabric is compromised?
- Data is compromised.
- Server CPUs become overloaded.
- Configurations can be changed or lost.
- End devices become infected.
168. What three phases would be addressed as part of doing business continuity planning? (Choose three.)
- a recovery phase
- an emergency response phase
- a quarantine or containment phase
- a return to normal operation phase
- a reaction phase
- an initiation phase
169. Logging into a computer as the administrator just to surf the web is a violation of which security technique?
- process isolation
- utilizing a reference monitor
- access control to resources
- least privilege
170. What is an example of toll fraud?
- the use of a telephony system to send unsolicited and unwanted bulk messages
- the use of a telephony system to make unauthorized long distance calls
- the use of a telephony system to get information, such as account details, directly from users
- the use of a telephony system to illegally intercept voice packets in order to listen in on a call
171. A user complains about not being able to gain access to the network. What command would be used by the network administrator to determine which AAA method list is being used for this particular user as the user logs on?
- debug aaa accounting
- debug aaa authorization
- debug aaa authentication
- debug aaa protocol
172. Place the system development cycle (SDLC) phases in the order they occur (Not all options are used)
(Drag and drop)
1st -> Initiation
2nd -> Acqusition and Development
3rd -> Implementation
4th -> Operations and Maintenance
5th -> Disposition
173. Fill in the blank.
When role-based CLI is used, only the _____________ view has the ability to add or remove commands from existing views.
Answer: Root
174. Which type of NAT would be used on an ASA where 10.0.1.0/24 inside addresses are to be translated only if traffic from these addresses is destined for the 198.133.219.0/24 network?
- static NAT
- dynamic PAT
- dynamic NAT
- policy NAT
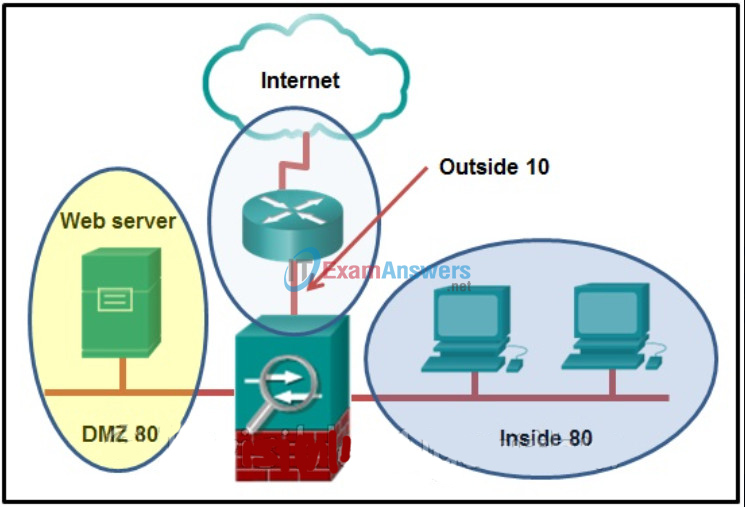
175. Refer to the exhibit. A network administrator is configuring the security level for the ASA. What is a best practice for assigning the security level on the three interfaces?
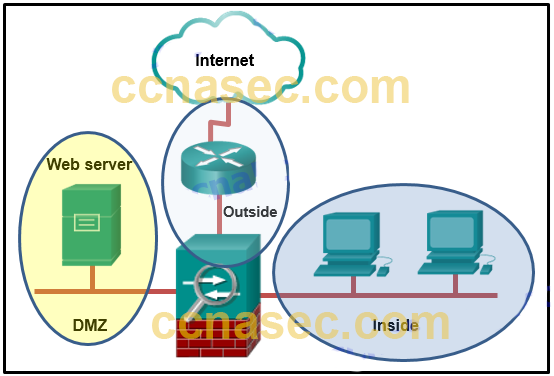
- Outside 0, Inside 35, DMZ 90
- Outside 40, Inside 100, DMZ 0
- Outside 100, Inside 10, DMZ 40
- Outside 0, Inside 100, DMZ 50
