Instructor Planning Guide
Activities
What activities are associated with this chapter?
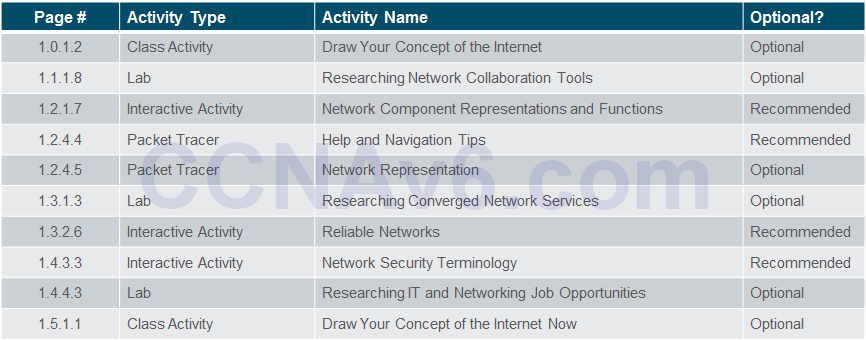
Assessment
Students should complete Chapter 1, “Assessment” after completing Chapter 1.
Quizzes, labs, Packet Tracers and other activities can be used to informally assess student progress.
Introduction to Networks
1.1 Globally Connected
Explain how multiple networks are used in every day life.
Explain how networks affect the way we interact, learn, work and play.
Explain how host devices can be used as clients, servers, or both.
1.2 LANs, WANs, and the Internet
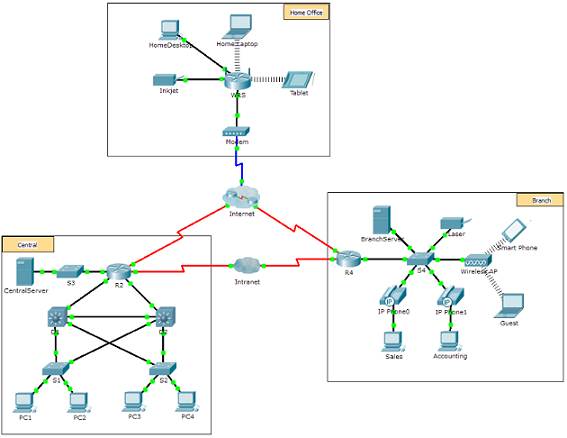
Explain how topologies and devices are connected in a small to medium-sized business network.
Explain the use of network devices..
Compare the devices and topologies of a LAN to the devices and topologies of a WAN.
Describe the basic structure of the Internet.
Explain how LANs and WANs interconnect to the Internet.
1.3 The Network as a Platform
Explain the basic characteristics of a network that supports communication in a small to medium-sized business.
Explain the concept of a converged network.
Describe the four basic requirements of a reliable network.
1.4 The Changing Network Environment
Explain trends in networking that will affect the use of networks in small to medium-sized businesses.
Explain how trends such as BYOD, online collaboration, video, and cloud computing are changing the way we interact.
Explain how networking technologies are changing the home environment.
Identify some basic security threats and solutions for both small and large networks.
Explain why it is important to understand the switching and routing infrastructure of a network.
Explore the Network
1.1 Globally Connected
1.1.1 Networking Today
1.1.1.1 Networks in Our Daily Lives
Welcome to a world where we are more powerful together, than we ever could be apart.
Welcome to the human network.

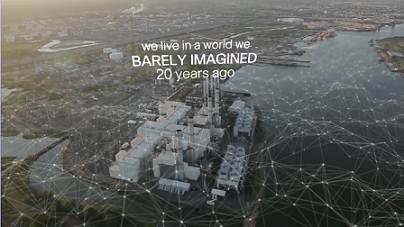
1.1.1.2 Technology Then and Now
We live in a world we barely imagined 20 years ago.
What wouldn’t we have without the Internet?
What will be possible in the future using the network as the platform?

1.1.1.3 No Boundaries
Advancements in networking technologies are helping create a world without boundaries.
The immediate nature of communications over the Internet encourages global communities.
Cisco refers to the impact of the Internet and networks on people the “human network”.

1.1.1.4 Networks Support the Way We Learn
Do you remember sitting in a classroom, like this?
You don’t have to be in school anymore to take a class. You don’t have to be in a classroom to have a teacher.


1.1.1.5 Networks Support the Way We Work
The globalization of the Internet has empowered individuals to create information that can be accessed globally.
Forms of communication:
♦ Texting
♦ Social Media
♦ Collaboration Tools
♦ Blogs
♦ Wikis
♦ Podcasting

Data networks have evolved into helping support the way we work.
Online learning opportunities decrease costly and time consuming travel.
Employee training is becoming more cost effective.

1.1.1.6 Networks Support the Way We Play
We listen to music, watch movies, read books, and download material for future offline access.
Networks allow online gaming in ways that were not possible 20 years ago.
Offline activities have also been enhanced by networks including global communities for a wide range of hobbies and interests.
How do you play on the Internet?

1.1.1.7 – Lab – Researching Network Collaboration Tools
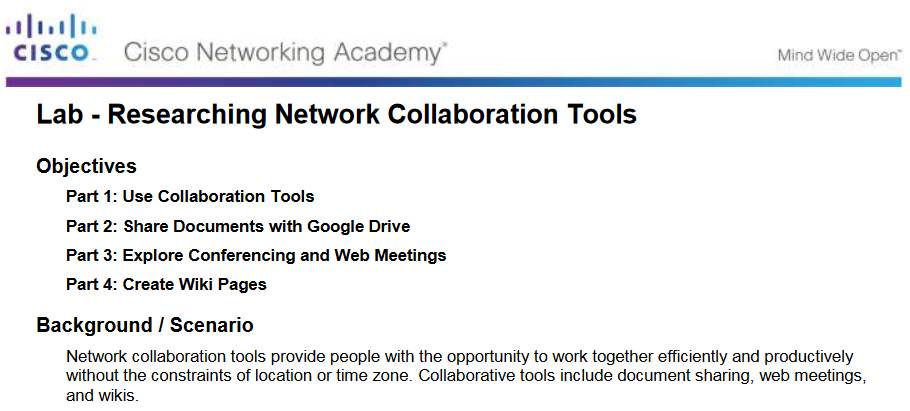
1.1.1.8 Lab – Researching Network Collaboration Tools
1.1.1.8 Lab – Researching Network Collaboration Tools
1.1.2– Providing Resources in a Network
1.1.2.1 – Networks of Many Sizes
Small Home Networks – connect a few computers to each other and the Internet
Small Office/Home Office – enables computer within a home or remote office to connect to a corporate network
Medium to Large Networks – many locations with hundreds or thousands of interconnected computers
World Wide Networks – connects hundreds of millions of computers world-wide – such as the Internet

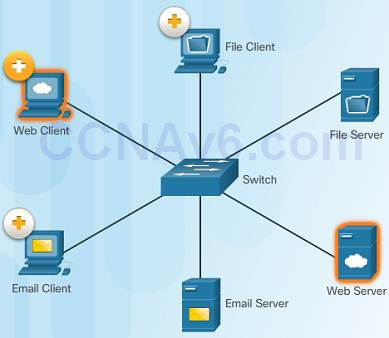
1.1.2.2 – Clients and Servers
Every computer connected to a network is called a host or end device.
Servers are computers that provide information to end devices on the network. For example, email servers, web servers, or file server
Clients are computers that send requests to the servers to retrieve information such as a web page from a web server or email from an email server.
1.1.2.3 – Peer-to-Peer
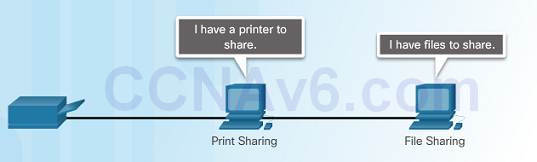
Client and server software usually run on separate computers.
However, in small businesses or homes, it is typical for a client to also function as the server. These networks are called peer-to-peer networks.
Peer-to-peer networking advantages: easy to set up, less complex, and lower cost.
Disadvantages: no centralized administration, not as secure, not scalable, and slower performance.
1.2 LANs, WANs, and the Internet
1.2.1 – Network Components
1.2.1.1 – Overview of Network Components
A network can be as simple as a single cable connecting two computers or as complex as a collection of networks that span the globe.
Network infrastructure contains three broad categories of network components:
♦ Devices
♦ Media
♦ Services

1.2.1.2 – End Devices
An end device is where a message originates from or where it is received.
Data originates with an end device, flows through the network, and arrives at an end device
1.2.1.3 – Intermediary Network Devices
An intermediary device interconnects end devices in a network. Examples include: switches, wireless access points, routers, and firewalls.
The management of data as it flows through a network is also the role of an intermediary device including:
♦ Regenerate and retransmit data signals.
♦ Maintain information about what pathways exist through the network and internetwork.
♦ Notify other devices of errors and communication failures.

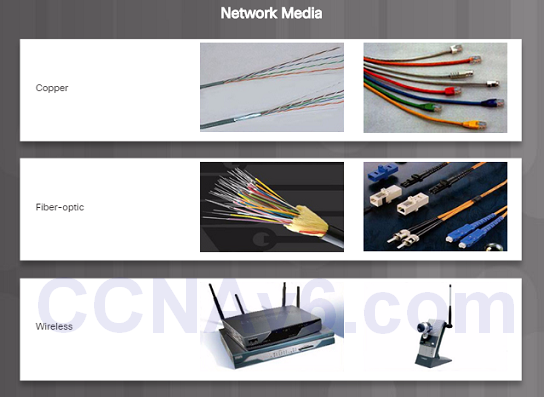
1.2.1.4 – Network Media
Communication across a network is carried through a medium which allows a message to travel from source to destination.
Networks typically use three types of media:
♦ Metallic wires within cables, such as copper
♦ Glass, such as fiber optic cables
♦ Wireless transmission
1.2.1.5 – Network Representations
Network diagrams, often called topology diagrams, use symbols to represent devices within the network.
In addition to the device representations on the right, it is important to remember and understand the following terms:
♦ Network Interface Card (NIC)
♦ Physical Port
♦ Interface

1.2.1.6 – Topology Diagrams
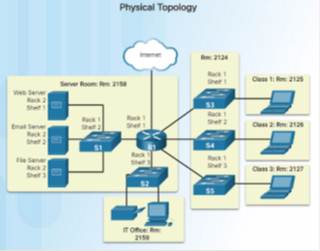
Note the key differences between the two topology diagrams (physical location of devices vs. ports and network addressing schemes)

1.2.2 – LANs and WANs
1.2.2.1 – Types of Networks
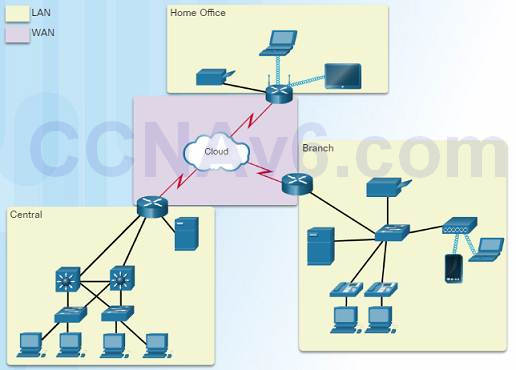
Two most common types of networks:
♦ Local Area Network (LAN) – spans a small geographic area owned or operated by an individual or IT department.
♦ Wide Area Network (WAN) – spans a large geographic area typically involving a telecommunications service provider.
♦ Other types of networks:
♦ Metropolitan Area Network (MAN)
♦ Wireless LAN (WLAN)
♦ Storage Area Network (SAN)
1.2.2.2 – Local Area Networks
Three characteristics of LANs:
♦ Spans a small geographic area such as a home, school, office building, or campus.
♦ Usually administered by a single organization or individual.
♦ Provides high speed bandwidth to end and intermediary devices within the network.

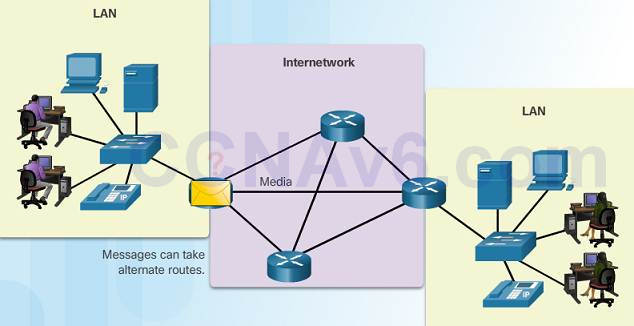
1.2.2.3 – Wide Area Networks
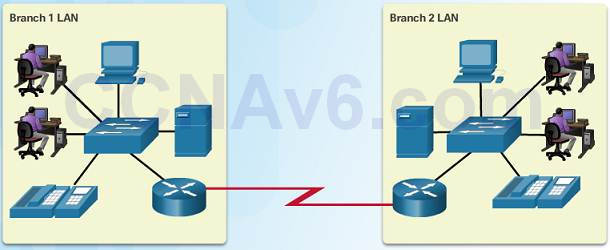
Three characteristics of WANs:
♦ WANs interconnect LANs over wide geographical areas such as between cities, states, or countries.
♦ Usually administered by multiple service providers.
♦ WANs typically provide slower speed links between LANs.
1.2.3 – The Internet, Intranets, and Extranets
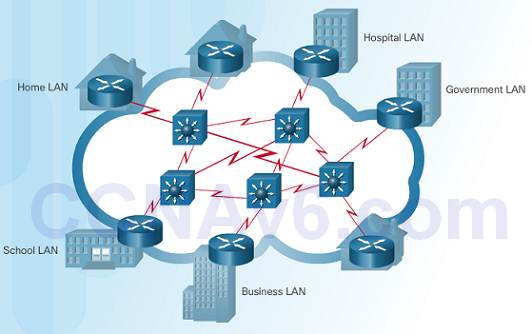
1.2.3.1 – The Internet
The Internet is a worldwide collection of interconnected LANs and WANs.
LANs are connected to each other using WANs.
WANs are then connected to each other using copper wires, fiber optic cables, and wireless transmissions.
The Internet is not owned by any individual or group, however, the following groups were developed to help maintain structure:
♦ IETF
♦ ICANN
♦ IAB
1.2.3.2 – Intranets and Extranets
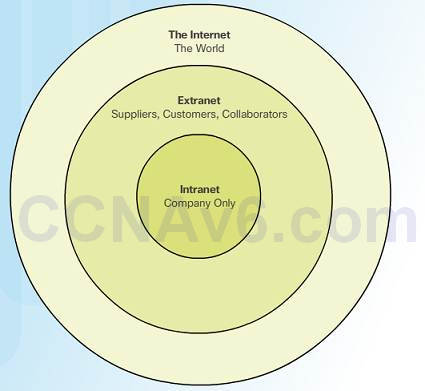
Unlike the Internet, an intranet is a private collection of LANs and WANs internal to an organization that is meant to be accessible only to the organizations members or others with authorization.
An organization might use an extranet to provide secure access to their network for individuals who work for a different organization that need access to their data on their network.
1.2.4 – Internet Connections
1.2.4.1 – Internet Access Technologies

There are many ways to connect users and organizations to the Internet:
♦ Popular services for home users and small offices include broadband cable, broadband digital subscriber line (DSL), wireless WANs, and mobile services.
♦ Organizations need faster connections to support IP phones, video conferencing and data center storage.
♦ Business-class interconnections are usually provided by service providers (SP) and may include: business DSL, leased lines, and Metro Ethernet.
1.2.4.2 – Home and Small Office Internet Connections
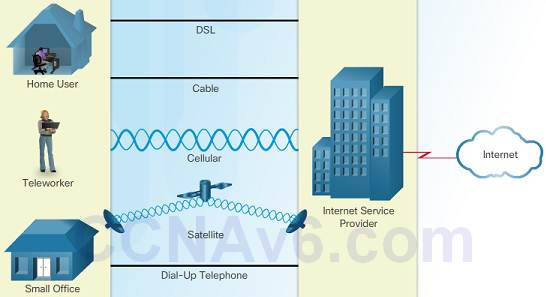
Cable – high bandwidth, always on, Internet connection offered by cable television service providers.
DSL – high bandwidth, always on, Internet connection that runs over a telephone line.
Cellular – uses a cell phone network to connect to the Internet; only available where you can get a cellular signal.
Satellite – major benefit to rural areas without Internet Service Providers.
Dial-up telephone – an inexpensive, low bandwidth option using a modem.
1.2.4.3 – Businesses Internet Connections
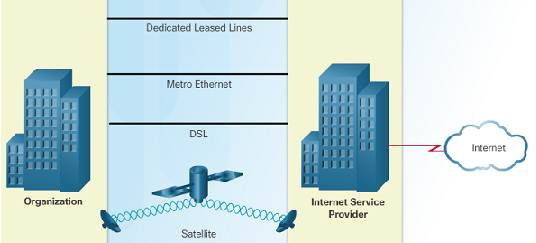
Corporate business connections may require higher bandwidth, dedicated connections, or managed services. Typical connection options for businesses:
♦ Dedicated Leased Line – reserved circuits within the service provider’s network that connect distant offices with private voice and/or data networking.
♦ Ethernet WAN – extends LAN access technology into the WAN.
♦ DSL – Business DSL is available in various formats including Symmetric Digital Subscriber Lines (SDSL).
♦ Satellite – can provide a connection when a wired solution is not available.
1.2.4.4 – Packet Tracer – Help and Navigation Tips
1.2.4.4 Packet Tracer – Help and Navigation Tips
♦ Overview of the Packet Tracer Program
♦ Packet Tracer is a fun software program which will help you with your CCNA studies by allowing you to experiment with network behavior, build networks, and find the answers to your “what if” questions.
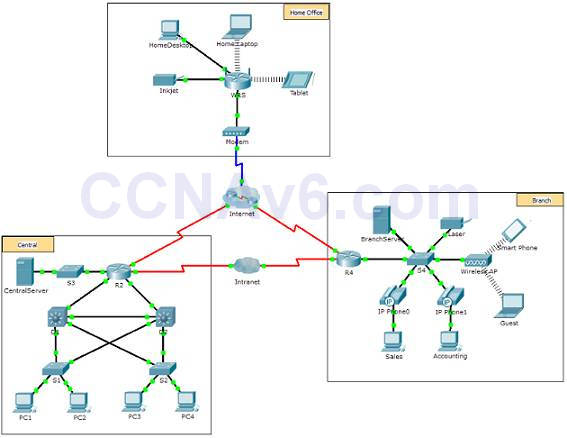
1.2.4.5 – Packet Tracer – Network Representation
1.2.4.5 Packet Tracer – Network Representation
This activity will allow you to explore how Packet Tracer serves as a modeling tool for network representations.
The network model in this activity incorporates many of the technologies you will need to master in your CCNA studies.
1.3 – The Network as a Platform
1.3.1 – Converged Networks
1.3.1.1 – Traditional Separate Networks
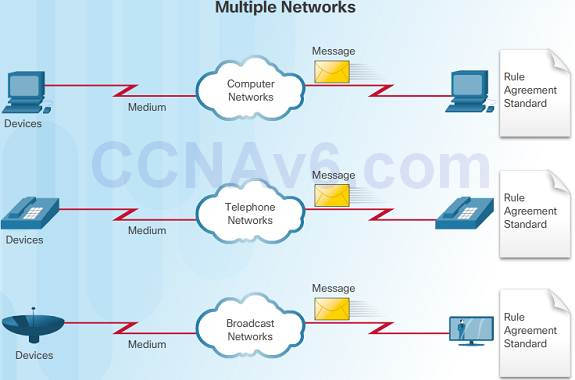
An example of multiple networks might be a school 30 years ago. Some classrooms were cabled for data networks. Those same classrooms were cabled for telephone networks, and also cabled separately for video.
Each of these networks used different technologies to carry the communication signals using a different set of rules and standards.
1.3.1.2 – The Converging Network
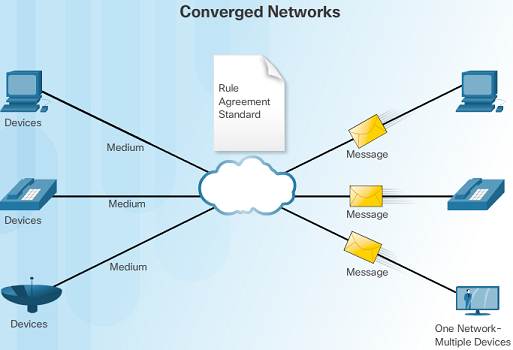
Converged data networks carry multiple services on one link including data, voice, and video.
Unlike dedicated networks, converged networks can deliver data, voice, and video between different types of devices over the same network infrastructure.
The network infrastructure uses the same set of rules and standards.
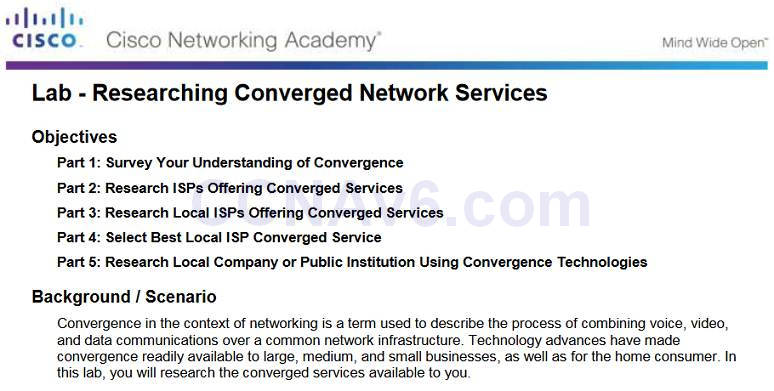
1.3.1.3 – Lab – Researching Converged Network Services
1.3.1.3 Lab – Researching Converged Network Services
1.3.2 – Reliable Network
1.3.2.1 – Network Architecture
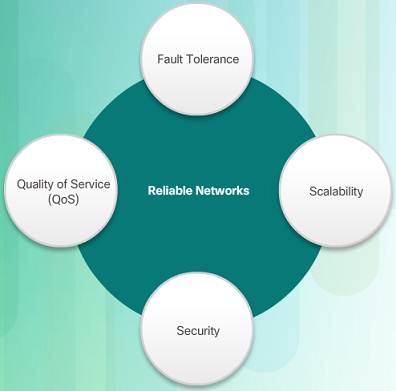
Network Architecture refers to the technologies that support the infrastructure that moves data across the network.
There are four basic characteristics that the underlying architectures need to address to meet user expectations:
♦ Fault Tolerance
♦ Scalability
♦ Quality of Service (QoS)
♦ Security
1.3.2.2 – Fault Tolerance

A fault tolerant network limits the impact of a failure by limiting the number of affected devices.
Multiple paths are required for fault tolerance.
Reliable networks provide redundancy by implementing a packet switched network. Packet switching splits traffic into packets that are routed over a network. Each packet could theoretically take a different path to the destination.
This is not possible with circuit-switched networks which establish dedicated circuits.
1.3.2.3 – Scalability
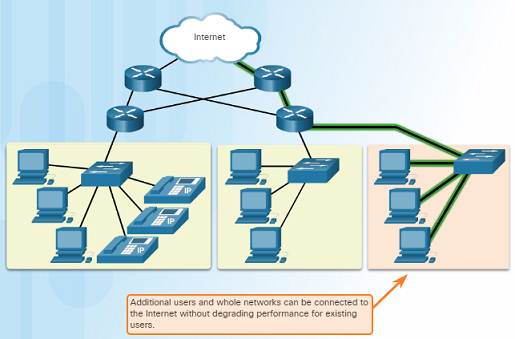
A scalable network can expand quickly and easily to support new users and applications without impacting the performance of services to existing users.
Network designers follow accepted standards and protocols in order to make the networks scalable.
1.3.2.4 – Quality of Service
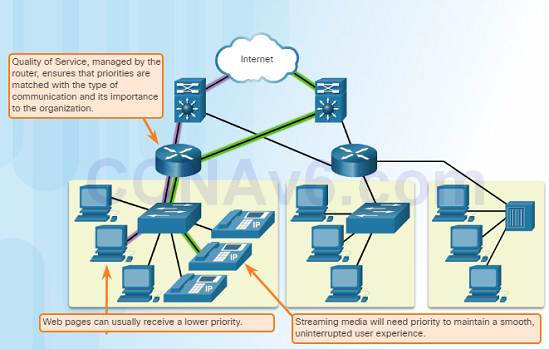
Voice and live video transmissions require higher expectations for those services being delivered.
Have you ever watched a live video with constant breaks and pauses? This is caused when there is a higher demand for bandwidth than available – and QoS isn’t configured.
Quality of Service (QoS) is the primary mechanism used to ensure reliable delivery of content for all users.
With a QoS policy in place, the router can more easily manage the flow of data and voice traffic.
1.3.2.5 – Security
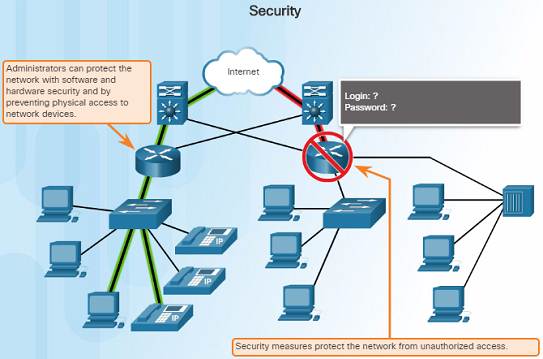
There are two main types of network security that must be addressed:
♦ Network infrastructure security
◊ Physical security of network devices
◊ Preventing unauthorized access to the management software on those devices
♦ Information Security
◊ Protection of the information or data transmitted over the network
♦ Three goals of network security:
◊ Confidentiality – only intended recipients can read the data
◊ Integrity – assurance that the data has not be altered with during transmission
◊ Availability – assurance of timely and reliable access to data for authorized users
1.4 – The Changing Network Environment
1.4.1 – Network Trends
1.4.1.1 – New Trends

The role of the network must adjust and continually transform in order to be able to keep up with new technologies and end user devices as they constantly come to the market.
Several new networking trends that effect organizations and consumers:
♦ Bring Your Own Device (BYOD)
♦ Online collaboration
♦ Video communications
♦ Cloud computing
1.4.1.2 – Bring Your Own Device

Bring Your Own Device (BYOD) is a major global trend that allows users to use their own devices giving them more opportunities and greater flexibility.
BYOD allows end users to have the freedom to use personal tools to access information and communicate using their:
♦ Laptops
♦ Netbooks
♦ Tablets
♦ Smartphones
♦ E-readers
1.4.1.3 – Online Collaboration
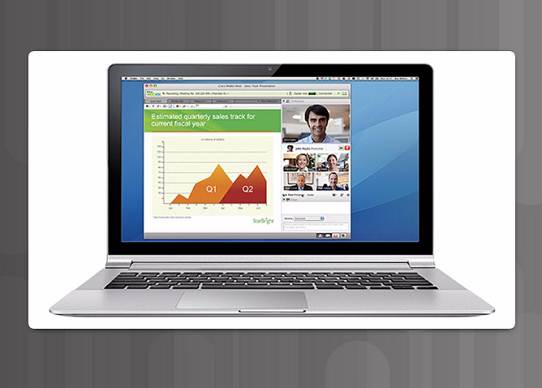
Individuals want to collaborate and work with others over the network on joint projects.
Collaboration tools including Cisco WebEx (shown in the figure) gives users a way to instantly connect, interact and achieve their objectives.
Collaboration is a very high priority for businesses and in education.
1.4.1.4 – Video Communication
Cisco TelePresence powers the new way of working where everyone, everywhere, can be more productive through face to face collaboration.
Around the world each day, we transform organizations by transforming our customer experiences.

1.4.1.5 – Cloud Computing
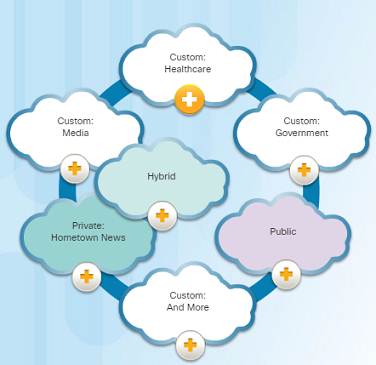
Cloud computing is a global trend that allows us to store personal files or backup our data on servers over the Internet.
Applications such as word processing and photo editing can also be accessed using the Cloud.
Cloud computing also allows businesses to extend their capabilities on demand and delivered automatically to any device anywhere in the world.
Cloud computing is made possible by data centers. Smaller companies that can’t afford their own data centers, lease server and storage services from larger data center organizations in the Cloud.
Four types of Clouds:
♦ Public Clouds
♦ Services and applications are made available to the general public through a pay-per-use model or for free.
♦ Private Clouds
♦ Applications and services are intended for a specific organization or entity such as the government.
♦ Hybrid Clouds
♦ Made up of two or more Cloud types – for example, part custom and part public. Each part remains a distinctive object but both are connected using the same architecture.
♦ Custom Clouds
1.4.2 – Network Trends
1.4.2.1 – Technology Trends in the Home
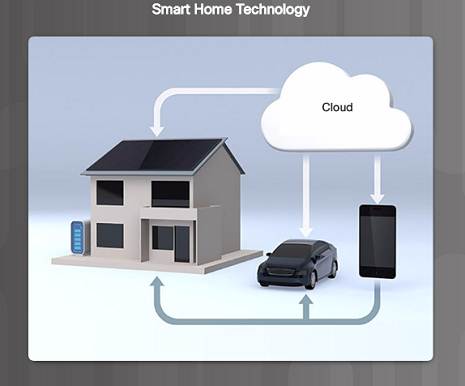
Smart home technology is a growing trend that allows technology to be integrated into every-day appliances which allows them to interconnect with other devices.
Ovens might know what time to cook a meal for you by communicating with your calendar on what time you are scheduled to be home.
1.4.2.2 – Powerline Networking
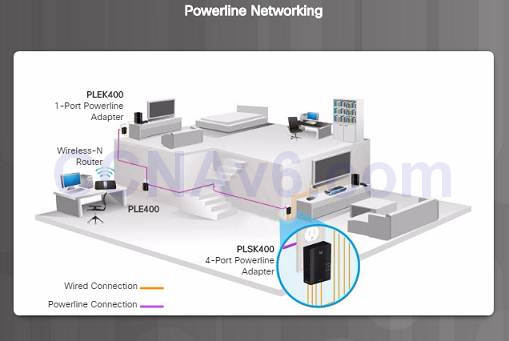
Powerline networking can allow devices to connect to a LAN where data network cables or wireless communications are not a viable option.
Using a standard powerline adapter, devices can connect to the LAN wherever there is an electrical outlet by sending data on certain frequencies.
1.4.2.3 – Wireless Broadband
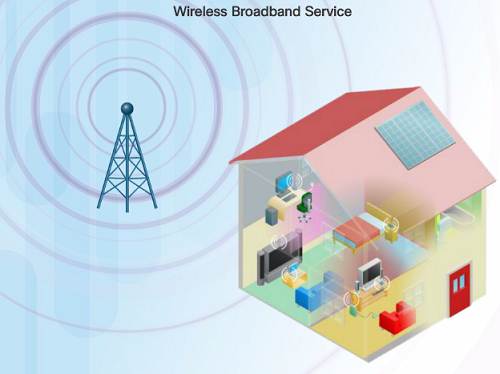
In addition to DSL and cable, wireless is another option used to connect homes and small businesses to the Internet.
More commonly found in rural environments, a Wireless Internet Service Provider (WISP) is an ISP that connects subscribers to designated access points or hotspots.
Wireless broadband is another solution for the home and small businesses.
♦ Uses the same cellular technology used by a smart phone.
♦ An antenna is installed outside the house providing wireless or wired connectivity for devices in the home.
1.4.3 – Network Security
1.4.3.1 – Security Threats
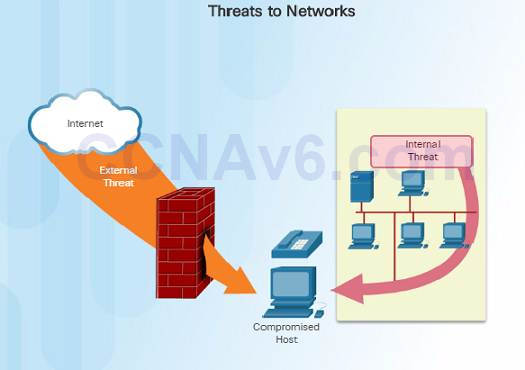
Network security is an integral part of networking regardless of the size of the network.
The network security that is implemented must take into account the environment while securing the data, but still allowing for quality of service that is expected of the network.
Securing a network involves many protocols, technologies, devices, tools, and techniques in order to secure data and mitigate threats.
Threat vectors might be external or internal.
External threats:
♦ Viruses, worms, and Trojan horses
♦ Spyware and adware
♦ Zero-day attacks, also called zero-hour attacks
♦ Hacker attacks
♦ Denial of Service attacks
♦ Data interception and theft
♦ Identify Theft
Internal threats:
♦ Whether intentional or not, many studies show that the internal users of the network cause the most security breaches.
♦ With BYOD strategies, corporate data is more vulnerable.
1.4.3.2 – Security Solutions
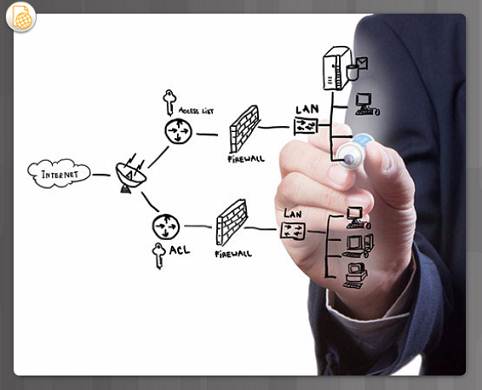
Security must be implemented in multiple layers using more than one security solution.
Network security components for home or small office network:
♦ Antivirus and antispyware software should be installed on end devices.
♦ Firewall filtering used to block unauthorized access to the network.
Larger networks have additional security requirements:
♦ Dedicated firewall system to provide more advanced firewall capabilities.
♦ Access control lists (ACL) – used to further filter access and traffic forwarding.
♦ Intrusion prevention systems (IPS) – used to identify fast-spreading threats such as zero-day attacks.
♦ Virtual private networks (VPN) – used to provide secure access for remote workers.
1.4.4 – Network Architecture
1.4.4.1 – Cisco Network Architecture

In order for networks to function while efficiently supporting connections of people, devices, and information in a media rich converged environment, the network must be built upon a standard network architecture.
Network architecture refers to the devices, connections, and products that are integrated to support the necessary technologies and applications.
The foundation of all network architectures including the Internet are routers and switches.
1.4.4.2 – CCENT and CCNA Certification
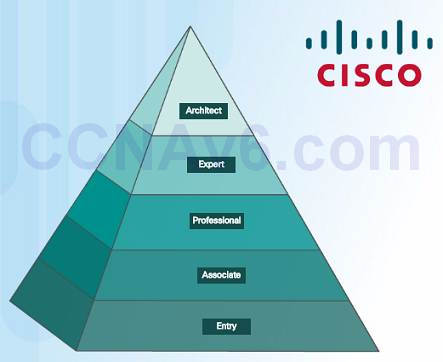
Cisco Certified Network Associate (CCNA)
♦ Routing and Switching Certification
♦ Requires you to pass two exams:
♦ First exam: Cisco Certified Entry Network Technician (CCENT)
♦ Second exam focuses on IPv4 and IPv6 routing and WAN technologies as well as LAN switching and infrastructure services/maintenance
1.4.4.3 – Lab – Researching IT and Networking Job Opportunities
1.4.4.3 Lab – Researching IT and Networking Job Opportunities
1.5 Chapter Summary
1.5.1 – Conclusion
1.5.1.1 – Warriors of the Net
1.5.1.1 Class Activity – Draw Your Concept of the Internet Now
The animated video below will help you visualize networking concepts.
1.5.1.2 – Exploring the Network

Networks and the Internet have dramatic impact on our lives.
A network can consist of two devices, or can be as large as the Internet, consisting of millions of devices.
The network infrastructure is the platform that supports the network.
Networks must be:
♦ Fault tolerant
♦ Scalable
♦ Support Quality of Service
♦ Secure
1.5.2 – Conclusion
1.5.2.1 Chapter 1: Introduction to Networks
Explain how multiple networks are used in every day life.
Explain how topologies and devices are connected in a small to medium-sized business network.
Explain the basic characteristics of a network that support communication in a small to medium-sized business.
Explain trends in networking that will affect the use of networks in small to medium-sized businesses.
1.5.2.2 New Terms and Commands
| Peer-to-Peer File SharingSmall Office/Home Office or SOHO
Medium to large network Server Client Peer-to-Peer network End device Intermediary device Medium Network Interface Card (NIC) Physical Port Interface Physical topology diagram |
Logical topology diagram
Local Area Network (LAN) Wide Area Network (WAN) Internet Intranet Extranet Internet Service Provider (ISP) Converged networks Network architecture Fault tolerant network Packet-switched network Circuit-switched network Scalable network Quality of Service (Qos) |
Network bandwidth
Bring Your Own Device (BYOD) Collaboration Cloud computing Private clouds Hybrid clouds Public clouds Custom clouds Data center Smart home technology Powerline networking Wireless Internet Service Provider (WISP) Network architecture |
