Section 49 Tasks
- Take the exam below
- Complete the challenge lab
- Review IPv6/OSPF/Syslog/SNMP/Netflow/EIGRP
- Read the ICND2 cram guide (and the ICND1 cram guide, if taking the CCNA exam)
- Spend 15 minutes on the subnetting.org website
Section 49 Exam
- What service and port does DNS use?
- How would you block EIGRP with an ACL?
- How does EIGRP and OSPF offer a way of sending route updates securely?
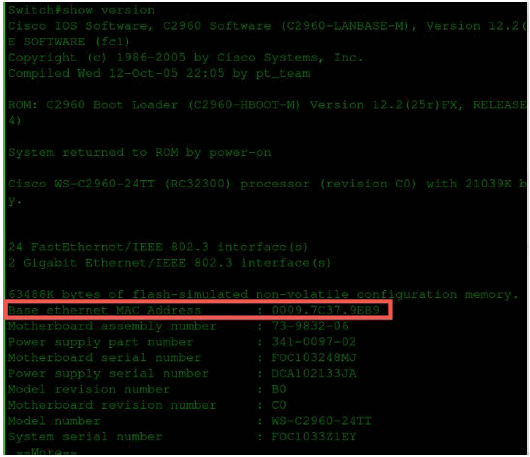
- Where do switches get their base MAC address from? How would you find it?
- Does PPP work with asynchronous links, or just synchronous?
- How would you join OSPF Area 2 to the OSPF domain if it was connected only to Area 1?
Section 49 Answers
- TCP/UDP port 53.
- Issue the acces-list x deny eigrp any any command.
- EIGRP: Interface mode authentication; and OSPF: authentication under router OSPF and under interface configuration.
- From the show version command (see below).
- Both types of links.
- Use the virtual-link command (this is not in the CCNA syallbus but I thought I’d add it just in case).
Section 49 Lab – OSPF and ACL
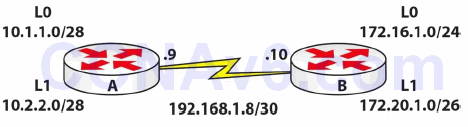
Topology
Instructions
Connect two routers together with a serial or crossover cable:
- Add IP addresses to the routers and a Loopback interface on Router A and Router B, according to the diagram
- Ping between Router A and Router B to test the serial line (remember clock rates)
- Configure OSPF on both routers
- Ensure that you add all the correct wildcard masks (which subnet is the WAN link in?)
- Put all networks into an area, but put 172.20.1.0/26 into Area 1 and 10.2.2.0/28 into Area 20
- Check the routing table and ping all IP addresses
- Configure an extended ACL on Router B
- Block www traffic into Router B destined for the 172.20.1.0/26 network; permit all other IP traffic
- You can only test this if you have a web server behind the router OR on live routers by adding the ip http server command to the router and Telnetting on port 80:
RouterA#telnet 172.20.1.0 80 [this won’t work on Packet Tracer]
Solution Hints and Commands
- Use the router ospf x command to configure OSPF
- network x.x.x.x y.y.y.y area z
- access-list 100 deny tcp any 172.20.1.0 0.0.0.63 eq www
