7.3.2.7 Packet Tracer – Cable a Simple Network (Answers) Objectives Develop an understanding of the basic functions of Packet Tracer. Create a simple network with two hosts. Observe the importance of using the correct cable type to connect PCs. Hint: To ensure that the instructions always remain visible …
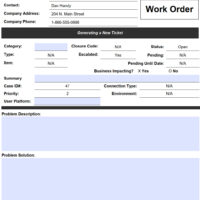
14.4.1.3 Lab – Remote Technician – Fix a Security Problem (Answers) Introduction You will gather data from the customer to begin the troubleshooting process. You will document the customer’s problem and possible solution in the work order. Lab Setup Answers Note: You must prepare a wireless router for …
14.4.1.2 Lab – Troubleshoot Security Problems (Answers) Introduction In this lab, you will diagnose the cause of various access security problems and solve them. Recommended Equipment One computer running Windows Scenario Company XYZ has hired Devon to manage the training department. Shawna was also hired as a temporary …
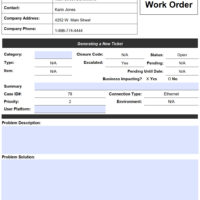
14.3.1.3 Lab – Remote Technician – Fix a Network Problem (Answers) Introduction In this lab, you will gather data from the customer, and then instruct the customer to fix a computer that does not connect to the network. Document the customer’s problem in the work order below. Lab …
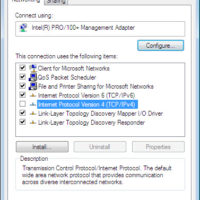
14.3.1.2 Lab – Troubleshoot Network Problems (Answers) Introduction In this lab, you will diagnose the causes and solve the network problems. Recommended Equipment Two computers running Windows A wireless router Two Ethernet cables Internet access Scenario You must solve network problems for a customer. You may need to …
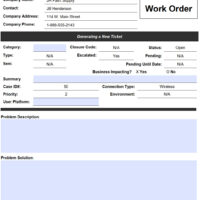
14.2.1.3 Lab – Remote Technician – Fix an Operating System Problem (Answers) Introduction In this lab, you will gather data from the customer, and then instruct the customer to fix a computer that does not connect to the network. Document the customer’s problem in the work order below. …
14.2.1.2 Lab – Troubleshoot Operating System Problems (Answers) Introduction In this lab, you will diagnose the cause of various operating system problems and solve them. Recommended Equipment A computer with Windows installed Windows installation media Scenario You must solve operating system problems for a customer. Make sure you …
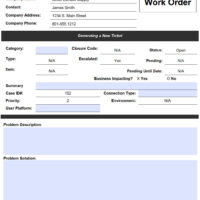
14.1.1.3 Lab – Remote Technician – Fix a Hardware Problem (Answers) Introduction In this lab, you will gather data from the customer, and then instruct the customer to fix a computer that does not boot. Document the customer’s problem in the work order below. Answers Note: In this …
14.1.1.2 Lab – Troubleshoot Hardware Problems (Answers) Introduction In this lab, you will diagnose the cause of various hardware problems and solve them. Recommended Equipment A computer with an operating system installed Additional hardware that is either broken or in a working condition. You may wish to use …
13.1.1.3 Lab – Technician Resources (Answers) In this lab, you will use the Internet to find resources for a specific computer component. Search online for resources that can help you troubleshoot the component. In the table below, list at least one website for each of the following types …