12.0 – Introduction
12.0.1 – Welcome
12.0.1.1 – Chapter 12: Mobile, Linux, and OSX Operating Systems
The use of mobile devices has grown very rapidly. IT technicians and professionals must be familiar with the operating systems on these devices. Like desktops and laptops, mobile devices also use operating systems to interface with the hardware and to run software. The two most commonly used mobile operating systems are Android and iOS. There are also desktop operating systems other than Windows, the two most popular being Linux and macOS.
In this chapter, you will learn about the components, functions, and terminology related to mobile, Linux, and macOS operating systems. First you will learn about the differences between the Android and iOS mobile operating systems, Linux being open source and customizable, and iOS being proprietary to Apple and closed source. You will also learn about common mobile device features like screen orientation, screen calibration, Wi-Fi calling, virtual assistants, and GPS. You will work with both the Android and iOS operating systems as part of lab exercises.
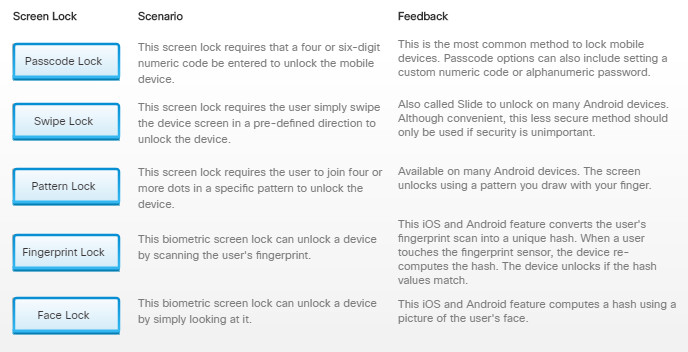
The portable nature of mobile devices makes them at risk for theft and loss. You will learn about mobile security features such as screen lock, biometric authentication, remote lock, remote wipe, and patching and upgrading. You also learned that mobile OSs can be configured to disable access if too many failed login attempts are made. This can prevent someone from trying to guess a passcode. Most mobile devices also have a remote lock and remote wipe feature that can be activated if the device is stolen. You will perform a lab exercise securing a mobile device using passcode locks.
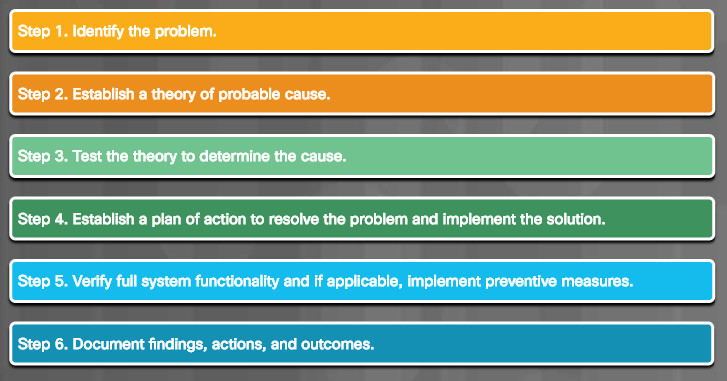
Finally, you will learn the six steps in the troubleshooting process as they are applied to mobile, Linux, and macOS operating systems.
12.1 – Mobile Operating Systems
12.1.1 – Android vs. iOS
12.1.1.1 – Open Source vs. Closed Source
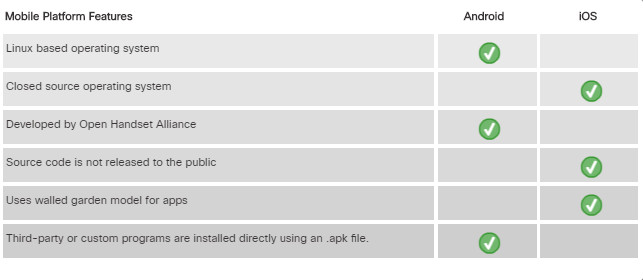
Like desktops and laptops, mobile devices use an operating system (OS) to run software. This chapter focuses on the two most commonly used mobile operating systems: Android and iOS. Android is developed by Google, and iOS is developed by Apple.
Before users can analyze and modify software, they must be able to see the source code. Source code is the sequence of instructions that is written in human readable language, before it is turned into machine language (zeroes and ones). The source code is an important component of free software as it allows the users to analyze and eventually modify the code. When the developer chooses to provide the source code, the software is said to be open source. If the program’s source code is not published, the software is said to be closed source.

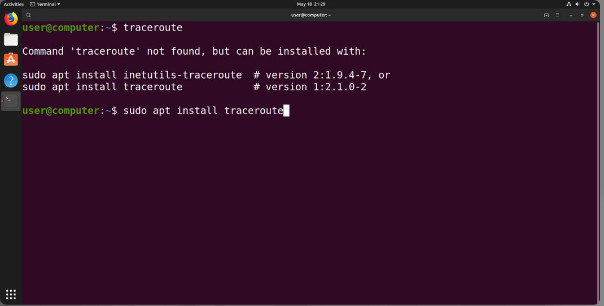
Android is an open source, Linux based smartphone/tablet operating system developed by the Open Handset Alliance, primarily driven by Google. Released in 2008 on the HTC Dream, the Android OS has been customized for use on a wide range of electronic devices. Because Android is open and customizable, programmers can use it to operate devices like laptops, smart TVs, and e-book readers. There have even been Android installations in devices like cameras, navigation systems, and portable media players. The figure shows Android running on a tablet.
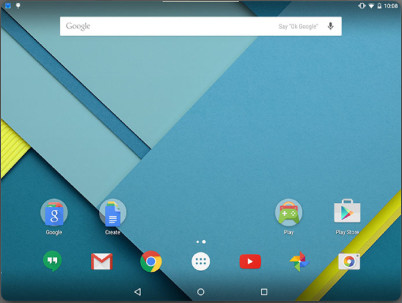
iOS is a closed source Unix based operating system for Apple’s iPhone smartphone and iPad tablet. Released in 2007 on the first iPhone, the Apple iOS source code was not released to the public. To copy, modify or redistribute iOS requires permission from Apple. The figure shows iOS running on an iPhone.

iOS is not the only closed source OS for mobile devices. Microsoft also created a version of Windows for their mobile devices. This includes Windows CE, Windows Phone 7, shown in the figure, and Windows Phone 8. With the development of Windows 10 Mobile, Microsoft provides a very similar user interface and use of code an all of their devices. This includes their Windows 10 Mobile phones and tablets they develop under the name Surface.

12.1.1.2 – Applications and Content Sources
Apps are the programs that are executed on mobile devices. Apps are written and compiled for a specific mobile operating system such as Apple iOS, Android, or Windows. Mobile devices come with a number of different apps preinstalled to provide basic functionality. There are apps to make phone calls, send and receive email, listen to music, take pictures, and play video or video games.
Apps are used on mobile devices the same way that programs are used on computers. Instead of being installed from an optical disk, apps are downloaded from a content source. Some apps can be downloaded for free, and others must be purchased.

Apps for Apple iOS mobile devices are available for free or purchase from the App Store. Apple uses a walled garden model for their apps meaning the apps must be submitted to and approved by Apple before they are released to users. This helps prevent the spread of malware and malicious code. Third-party developers can create apps for iOS devices by using Apple’s Software Development Kit (SDK) Xcode and the Swift programming language. Note that Xcode can only be installed on computers running OS X.
Android apps are available from both Google PlayTM and third-party sites, such as Amazon’s App store. Android Studio, a Java-based SDK, is available on Linux, Windows, and OS X. Android apps run in a sandbox and have only the privileges enabled by the user. A prompt will appear if an app needs to obtain permissions. Permissions are granted via the app’s Settings page.
Third-party or custom programs are installed directly using an Android Application Package (apk) file. This gives users the ability to directly install apps without going through the storefront interface. This is known as sideloading.
12.1.1.3 – Check Your Understanding – Compare Android and iOS
12.1.1.3 – Check Your Understanding – Compare Android and iOS
12.1.2 – Android Touch Interface
12.1.2.1 – Home Screen Items
Much like a desktop or laptop computer, mobile devices organize icons and widgets on multiple screens for easy access.
One screen is designated as the home screen. Additional screens are accessed by sliding the home screen to the left or right. Each screen contains navigation icons, the main area where icons and widgets are accessed, and notification and system icons. The screen indicator displays which screen is currently active.
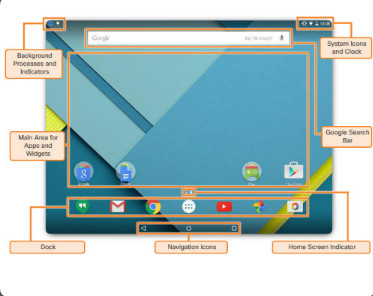
The Android® OS uses the system bar to navigate apps and screens. The system bar is always displayed at the bottom of every screen.
The system bar contains the following buttons:
- Back – Returns to the previous screen. If the on-screen keyboard is displayed, this button closes it. Continuing to press the Back button navigates through each previous screen until the home screen is displayed.
- Home – Returns to the home screen.
- Recent Apps – Opens thumbnail images of recently used apps. To open an app, touch its thumbnail. Swipe a thumbnail to remove it from the list.
- Menu – If available, Menu shows additional options for the current screen.
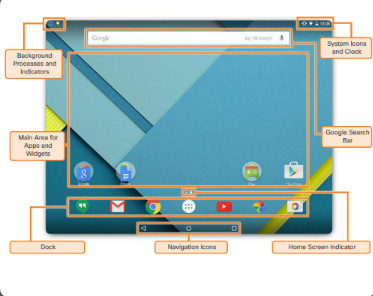
Each Android® device has an area that contains system icons, such as the clock, battery status, and radio signal status for Wi-Fi and provider networks. Apps such as email, text messaging, and Facebook® often display status icons to indicate communication activity.
To open the notification area on Android® devices, swipe down from the top of the screen. You can do the following when notifications are open:
- Respond to a notification by touching it.
- Dismiss a notification by swiping it off the screen to either side.
- Dismiss all notifications with the icon.
- Toggle often-used settings.
- Adjust the brightness of the screen.
- Open the Settings menu with the quick settings icon.
12.1.2.2 – Lab – Working with Android
In this lab, you will work with the Android operating system.
12.1.2.2 – Lab – Working with Android
12.1.3 – iOS Touch Interface
12.1.3.1 – Home Screen Items
The iOS interface works in much the same way as the Android interface. Screens are used to organize apps, and apps are launched with a touch. There are some very important differences:
- No navigation icons – A physical button may have to be pressed instead of touching navigation icons.
- No widgets – Only apps and other content can be installed on iOS device screens.
- No app shortcuts – Each app on a home screen is the actual app, not a shortcut.
Unlike Android, iOS devices do not use navigation icons to perform functions. On iPhone versions prior to the iPhone X, a single physical button called the Home button performs many of the same functions as the Android navigation buttons. The Home button is at the bottom of the device and can perform many functions. Some common functions performed by the home button with explanations of how these functions are performed on the iPhone X, which has eliminated the home button, are shown below:
- Wake the device – When the device’s screen is off, press the Home button once to turn it on. On iPhone X you can wake the device using either facial recognition or by raising the phone and tapping the screen. (Raise to wake is also available on iPhone versions 6s or later.)
- Return to the home screen – Press the Home button while using an app to return to the last home screen that was used. On iPhone X return to the home screen by swiping the screen up from the bottom.
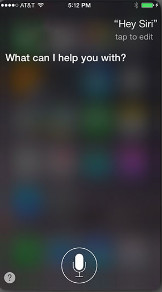
- Start Siri or voice control – Press and hold the Home button to start Siri or voice control. Siri is special software that understands advanced voice controls. On iPhone X Siri is launched by pressing and holding the side button.

iOS® devices have a notification center that displays all alerts in one location. To open the notification area on iOS devices, touch the top center of the screen and swipe down. Once in Notification Center you can browse notifications and alerts, dismiss them, clear them, and adjust them as necessary.
iOS devices allow the user to quickly access common settings and switches, even if the device is locked. To access the commonly used settings menu, swipe up from the very bottom of any screen. From the commonly used settings screen a user can:
-
- Toggle often used settings such as airplane mode, Wi-Fi, Bluetooth, do not disturb mode and screen rotation lock
-
- Adjust screen brightness
-
- Control the music player
-
- Access Airdrop
-
- Access Flashlight, Clock, Calendar and Camera

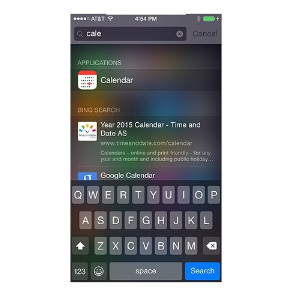
From any screen of an iOS device, touch the screen and drag down to reveal the Spotlight search field. Any part of the screen except the very top or the very bottom should work. When Spotlight search field is revealed, type what you’re looking for. Spotlight shows suggestions from many sources including the Internet, iTunes, App Store, movie show times, and nearby locations. Spotlight also automatically updates the results as you type.
12.1.3.2 – Lab – Working with iOS
In this lab, you will work with the iOS operating system.
12.1.3.2 – Lab – Working with iOS
12.1.4 – Common Mobile Device Features
12.1.4.1 – Screen Orientation
Most mobile devices can be used in either portrait or landscape mode. A sensor inside the device known as an accelerometer, detects how it is being held and will change the screen orientation appropriately. Users can choose the viewing mode that is the most comfortable for them for different types of content or applications. Content is automatically rotated to the position of the device. This feature is useful, for example, when taking a photograph. When the device is turned to landscape mode, the camera app also turns to landscape mode. Also, when a user is writing a text, turning the device to landscape mode automatically turns the app to landscape mode, making the keyboard larger and wider.
Some devices also have gyroscopes to provide more accurate movement readings. Gyroscopes allow a device to be used as a control mechanism for driving games where the phone or tablet itself functions as a steering wheel.

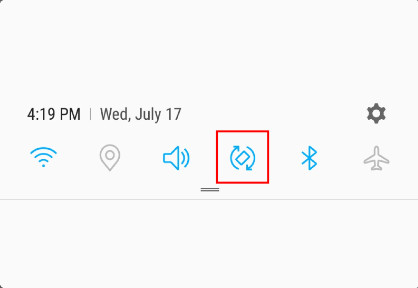
When using an Android device, to enable auto rotation, open the notifications panel and turn on the auto-rotate function by tapping the screen rotation icon, indicated in the figure.
When using an iOS device, to enable automatic rotation use the following procedure:
Swipe up from the bottom or down from the top to open the control center, depending on your device. > tap the lock icon.

12.1.4.2 – Screen Calibration
When using a mobile device, you may need to adjust the brightness of the screen. When bright sunlight makes the screen difficult to read, increase the brightness level. Inversely, very low brightness is helpful when reading a book on a mobile device at night. Some mobile devices can be configured to auto-adjust the brightness depending on the amount of surrounding light. The device must have a light sensor to use auto-brightness.
The LCD screen for most mobile devices uses the most battery power. Lowering the brightness or using auto-brightness helps conserve battery power. Set the brightness to the lowest setting to get the most battery life from the device.

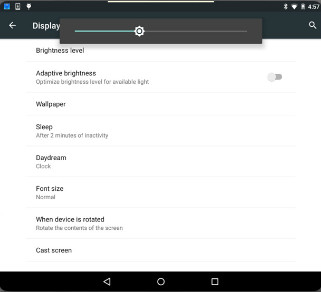
When using an Android device, to configure screen brightness use the following path:
Swipe down from the very top of the screen > Display > Brightness > slide the brightness to the desired level
Alternatively, tap the Adaptive Brightness toggle to allow the device to decide the optimal screen brightness based on the amount of ambient light.
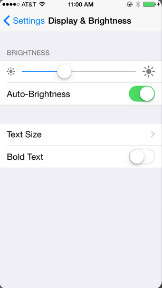
When using an iOS device, to configure screen brightness, use the following path:
Swipe up from the very bottom of the screen > slide the brightness bar up or down to vary the brightness.
Alternatively, to configure brightness in the Settings menu, use the following path:
Settings > Display & Brightness > slide the brightness to the desired level.
12.1.4.3 – GPS
Another common feature of mobile devices is the Global Positioning System (GPS). GPS is a navigation system that determines the time and geographical location of the device by using messages from satellites in space and a receiver on Earth. A GPS radio receiver uses at least four satellites to calculate its position based on the messages. GPS is very accurate and can be used under most weather conditions. However, dense foliage, tunnels, and tall buildings can interrupt satellite signals. GPS receivers must have line-of-sight to GPS satellites and do not work indoors. Indoor Positioning Systems (IPS) can determine device location by triangulating its proximity to other radio signals such as Wi-Fi access-points.
GPS services allow app vendors and website to know the location of a device and offer location-specific services (such as local weather and advertising). This is called geotracking.

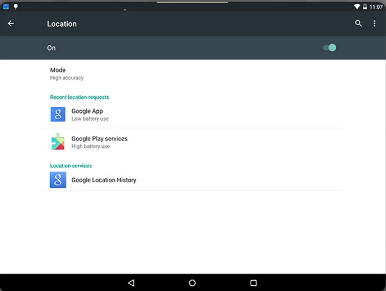
To enable GPS on Android devices use the following path:
Settings > Location > Tap on the toggle to turn location services on
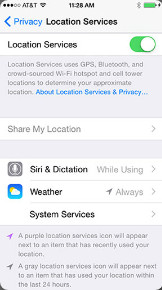
To enable GPS on iOS devices use the following path:
Settings > Privacy > Location services > Turn location services on
12.1.4.4 – Lab – Mobile Device Features
In this lab, you will learn about mobile device features.
12.1.4.4 – Lab – Mobile Device Features
12.1.4.5 – Wi-Fi Calling
Instead of using the cellular carrier’s network, modern smartphones can use the internet to transport voice calls by taking advantage of a local Wi-Fi hotspot. This is called Wi-Fi calling. Locations, such as coffee shops, work places, libraries, or homes, usually have Wi-Fi networks connected to the internet. The phone can transport voice calls through the local Wi-Fi hotspot. If there is no Wi-Fi hotspot within reach, the phone will use the cellular carrier’s network to transport voice calls.
Wi-Fi calling is very useful in areas with poor cellular coverage because it uses a local Wi-Fi hotspot to fill the gaps. The Wi-Fi hotspot must be able to guarantee a throughput of at least 1Mbps to the internet for a good quality call. When Wi-Fi calling is enabled and in use during a voice call, the phone will display “Wi-Fi” next to the carrier name.

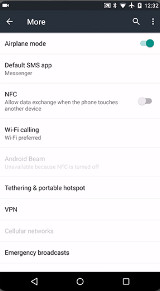
To enable Wi-Fi calling on Android use the following path:
Settings > More (under Wireless & networks section) > Wi-Fi Calling > Tap on the toggle to turn it on
To enable Wi-Fi calling on iOS use the following path:
Settings > Phone and turn on Wi-Fi Calling
Note: Not all cellular carriers allow Wi-Fi calling. If you cannot enable it on your phone, your carrier or mobile device probably does not support it.

12.1.4.6 – NFC Payment
Premium SMS based transactional payments
Consumers send an SMS message to a carrier’s special phone number containing a payment request. The seller is informed the payment has been received and is cleared to release the goods. The charge is then added to the customer’s phone bill. Slow speed, poor reliability, and poor security are a few shortcomings of this method.
Direct Mobile Billing
Using a mobile billing option during check-out, a user identifies their self (usually through two-factor authentication) and allows the charge to be added to the mobile service bill. This is very popular in Asia and has the following benefits: security, convenience, and no need for bank cards or credit cards.
Mobile Web Payments
The consumer uses the web or dedicated apps to complete the transaction. This method relies on the Wireless Application Protocol (WAP) and usually requires the use of credit cards or a pre-registered online payment solution, such as PayPal.
Contactless NFC (Near Field Communication)
This method is used mostly in physical store transactions. A consumer pays for good or services by waving the phone near the payment system. Based on a unique ID, the payment is charged directly against a pre-paid account or bank account. NFC is also used in mass-transportation services, the public parking sector, and many other consumer areas.
12.1.4.7 – Virtual Private Network
A Virtual Private Network (VPN) is a private network that uses a public network (usually the internet) to connect remote sites or users together. Instead of using a dedicated leased line, a VPN uses “virtual” connections routed through the internet from the company’s private network to the remote site or employee.
Many companies create their own VPNs to accommodate the needs of remote employees and distant offices. With the proliferation of mobile devices, it was a natural move to add VPN clients to smartphones and tablets.
When a VPN is established from a client to a server, the client accesses the network behind the server as if it was connected directly to that network. Because VPN protocols also allow for data encryption, the communication between client and server is secure.
When the VPN information has been added to the device, that device must be started before traffic can be sent and received through it.

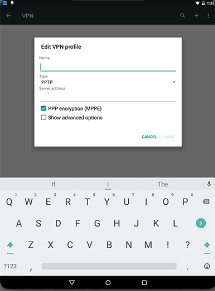
To create a new VPN connection on Android use the following path:
Settings > More (under Wireless & networks section) > VPN > Tap on the + sign to add a VPN connection
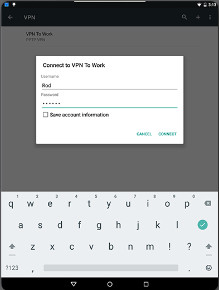
To start a VPN on Android use the following path:
Settings > General > VPN > Select the desired VPN connection > enter username and password > tap CONNECT
To create a new VPN connection on iOS use the following path:
Settings > General > VPN > Add VPN Configuration…
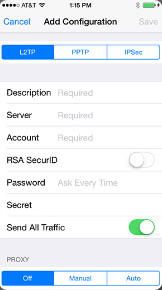
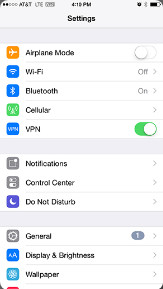
To start a VPN on iOS use the following path:
Settings > Toggle VPN to on
12.1.4.8 – Virtual Assistants
A digital assistant, sometimes called a virtual assistant, is a program that can understand natural conversational language and perform tasks for the end user. Modern mobile devices are powerful computers, making them the perfect platform for digital assistants. Popular digital assistants currently include Google Now for Android, Siri for iOS, and Cortana for Windows Phone 8.1.
These digital assistants rely on artificial intelligence, machine learning, and voice recognition technology to understand conversational-style voice commands. As the end user interacts with these digital assistants, sophisticated algorithms predict the user’s needs and fulfill requests. By pairing simple voice requests with other inputs, such as GPS location, these assistants can perform several tasks, including playing a specific song, performing a web search, taking a note, or sending an email.

To access Google Now on an Android device simply say “Okay google” and Google Now will activate and start listening to requests.

To access Siri on an iOS device, press and hold the Home button. Siri will activate and start listening to requests. Alternatively, Siri can be configured to start listening to commands when it hears “Hey Siri”. To enable “Hey Siri”, use the following path:
Settings > Siri & Search > Toggle Listen for “Hey Siri”.
12.2 – Methods for Securing Mobile Devices
12.2.1 – Screen Locks and Biometric Authentication
12.2.1.1 – What Do You Already Know? – Locks
12.2.1.1 – What Do You Already Know? – Locks
12.2.1.2 – Lab – Passcode Locks
In this lab, you will use passcode locks.
12.2.1.2 – Lab – Passcode Locks
12.2.1.3 – Restrictions on Failed Login Attempts
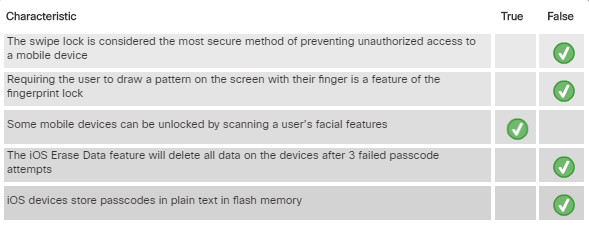
When a passcode has been properly implemented unlocking a mobile device requires entering the correct PIN, password, pattern, or another passcode type. In theory, a passcode, such as a PIN, could be guessed given enough time and perseverance. To prevent someone from trying to guess a passcode, mobile devices can be set to perform defined actions after a certain number of incorrect attempts have been made.
For Android devices, the number of failed attempts before lockout depends on the device and version of Android OS. It is common that an Android device will lock when a passcode has failed from 4 to 12 times. After a device is locked, you can unlock it by entering the Gmail account information used to set up the device.

For iOS devices, you can turn on the Erase data option as shown. If the passcode fails 10 times, the screen goes black, and all data on the device is deleted. To restore the iOS device and data, if you have backups, use either the Restore and Backup option in iTunes or the Manage Storage option in iCloud.
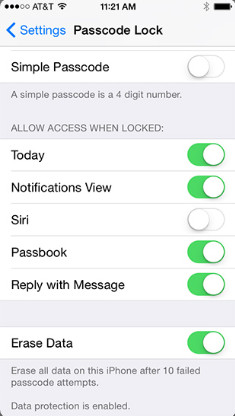
On iOS, to increase security, the passcode is used as part of the encryption key for the entire system. Because the passcode is not stored anywhere, no one can gain access to the user data on iOS devices, including Apple. The system depends on the user to provide the passcode before the system can be unlocked and decrypted for use. A forgotten passcode will render user data unreachable, forcing the user to perform a full restore from a backup saved in iTunes or iCloud.

12.2.1.4 – Check your Understanding – Screen Locks and Biometric Authentication
12.2.1.4 – Check your Understanding – Screen Locks and Biometric Authentication
12.2.2 – Cloud-Enabled Services for Mobile Devices
12.2.2.1 – Remote Backup
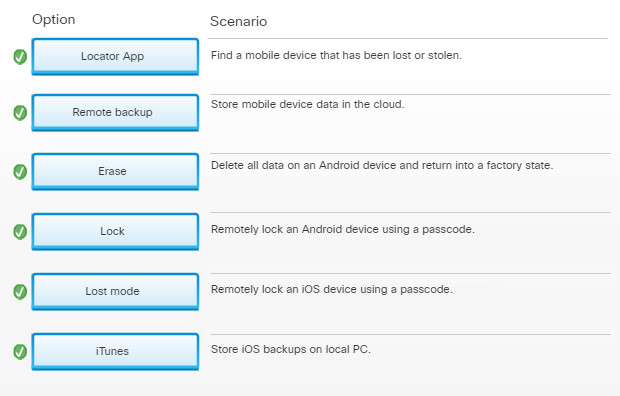
Mobile device data can be lost due to device failures or the loss or theft of the device. Data must be backed up periodically to ensure that it can be recovered if needed. With mobile devices, storage is often limited and not removable. To overcome these limitations, remote backups can be performed. A remote backup is when a device copies its data to cloud storage using a backup app. If data needs to be restored, run the backup app and access the website to retrieve the data.
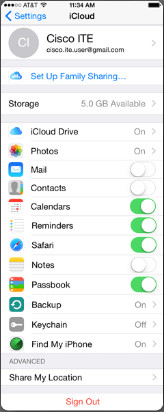
iCloud on iOS
Most mobile operating systems come with a user account linked to the vendor’s cloud services, such as iCloud for iOS, Google Sync for Android, and OneDrive for Microsoft. The user can enable automatic backups to the cloud for data, apps, and settings. There are also third-party back providers, such as Dropbox, that can be used. Mobile devices can also be backed up to a PC. iOS supports backups on iTunes running on a PC. Another option is to configure Mobile Device Management (MDM) software to automatically backup user devices.
12.2.2.2 – Locator Applications
If a mobile device is misplaced or stolen, it is possible to find it using a locator app. A locator app should be installed and configured on each mobile device before it is lost. Both Android and iOS have apps for remotely locating a device.
Similar to Apple’s Find My iPhone, Android Device Manager allows a user to locate, ring, or lock a lost Android device, or to erase data from the device. To manage a lost device, the user must visit Android Device Manager Dashboard hosted at https://www.google.com/android/devicemanager and log in with the Google account used on the Android device. Android Device Manager is included and enabled by default on Android 5.x and can be found under Settings > Security > Device Administration.
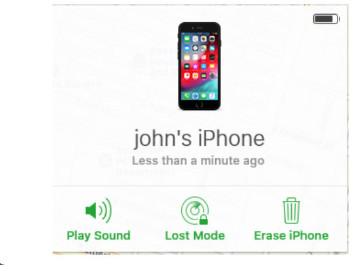
iOS users can use the Find My iPhone app, as shown in the figure. The first step is to install the app, start it, and follow the instructions to configure the software. The Find My iPhone app can be installed on different iOS devices to locate the lost device.
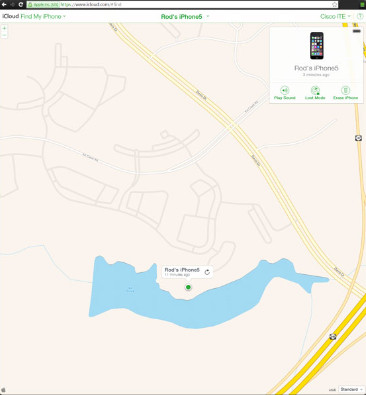
iOS Find My Phone
Note: If the app is unable to locate the lost device, the device might be turned off or disconnected. The device must be connected to a cellular or wireless network to receive commands from the app, or to send location information to the user.
After the device is located, you might be able to perform additional functions, such as sending a message or playing a sound. These options are useful if you have misplaced your device. If the device is close by, playing a sound indicates exactly where it is. If the device is at another location, sending a message to display on the screen allows someone to contact you if it has been found.
12.2.2.3 – Remote Lock and Remote Wipe
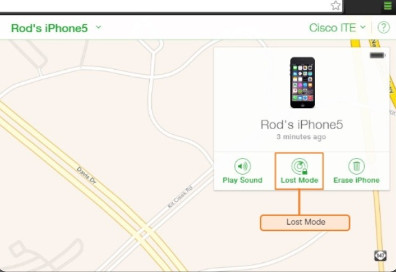
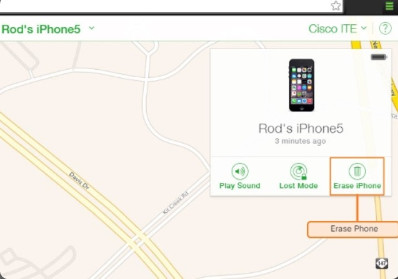
If attempts to locate a mobile device have failed, there are other security features that can prevent data on the device from being compromised. Usually, the same apps that perform remote location have security features. Two of the most common remote security features are remote lock and remote wipe.
Note: For these remote security measures to function, the device must be powered on and connected to a cellular or Wi-Fi network.
Click each button to learn more.
The remote lock feature for iOS devices is called lost mode. The Android Device Manager calls this feature Lock. It allows you to lock the device with a passcode, so others cannot gain access to the data in the device. For example, the user can display custom messages, or keep the phone from ringing due to incoming calls or text messages.
The remote wipe feature for iOS devices is called erase phone. The Android Device Manager calls this feature Erase. It deletes all data from the device and returns it to a factory state. To restore data to the device, Android users must set up the device using a Gmail account, and iOS users must synchronize their device to iTunes.
Most mobile device operating systems provide a full device encryption feature. Full device encryption can prevent anyone in possession of the device from circumventing the device’s access controls and reading the raw data stored in memory.
All user data on an iOS device is always encrypted and the key is stored on the device. When used to “wipe” the device, the OS deletes the key, and the data becomes inaccessible. Data Protection encryption is enabled automatically when a password lock is configured on the device.
On Android OS, encryption is enabled through Settings > Security. Android uses full-disk encryption with a passcode-derived key.
12.2.2.4 – Check Your Understanding – Cloud-Enabled Services for Mobile Devices
12.2.2.4 – Check Your Understanding – Cloud-Enabled Services for Mobile Devices
12.2.3 – Software Security
12.2.3.1 – Antivirus

Antivirus
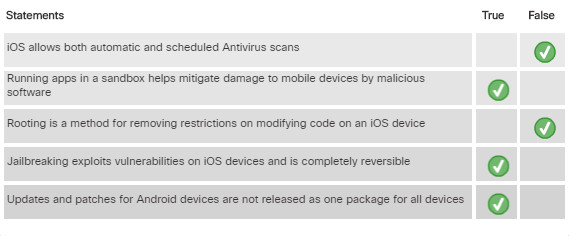
All computers are vulnerable to malicious software. Smartphones and other mobile devices are computers and are also vulnerable. Antivirus apps are available for both Android and iOS. Depending on the permissions granted to antivirus apps when they are installed on an Android device, the app might not be able to scan files automatically or run scheduled scans. File scans must be initiated manually. iOS does not allow automatic or scheduled scans. This is a safety feature to prevent malicious programs from using unauthorized resources or contaminating other apps or the OS. Some antivirus apps also provide locator services, remote lock, or remote wipe.
Mobile device apps run in a sandbox. A sandbox is a location of the OS that keeps code isolated from other resources and other code. It is difficult for malicious programs to infect a mobile device because apps are run inside the sandbox. An Android app asks for permission to access certain resources upon installation. A malicious app has access to any resources that were allowed permission during installation. This is another reason why it is important to download apps only from trusted sources. A trusted app source is one that is authenticated and authorized by a service provider. The service provider issues the developer a certificate to use to sign their apps and identify them as trusted.
Due to the nature of the sandbox, malicious software does not usually damage mobile devices; it is far more likely for a mobile device to transfer a malicious program to another device, such as a laptop or desktop. For example, if a malicious program is downloaded from email, the Internet, or another device, the malicious program could be placed on a laptop the next time it is connected to the mobile device.
To prevent the malicious program from infecting additional devices, a firewall can be used. Firewall apps for mobile devices can Monitor app activity and prevent connections to specific ports or IP addresses. Because mobile device firewall must be able to control other apps they logically work at a higher (root) permission level. No root firewalls work by creating a virtual private network (VPN) and then controlling app access to the VPN.
12.2.3.2 – Rooting and Jailbreaking
Mobile operating systems are usually protected by a number of software restrictions. An unmodified copy of iOS, for example, will only execute authorized code and allow very limited user access to its file system.
Rooting and Jailbreaking are two methods for removing restrictions and protections added to mobile operating systems. They are a means of circumventing the usual operating of the device operating system to gain super-user or root administrator permissions. Rooting is used on Android devices to gain privileged or root level access for modifying code or installing software that is not intended for the device. Jailbreaking is typically used on iOS devices to remove manufacturer restrictions allowing them to run arbitrary user-code, grant users full access to the file system and full access to kernel modules.

Rooting and Jailbreaking
Rooting or jailbreaking a mobile device usually voids the manufacturer’s warranty. It is not recommended that you modify a customer’s mobile device in this way. Nevertheless, a large group of users choose to remove their own devices’ restrictions. By rooting or jailbreaking a mobile device the GUI can be heavily customized, modifications can be made to the OS to improve the speed and responsiveness of the device, and apps can be installed from secondary or unsupported sources.
Jailbreaking exploits vulnerabilities in iOS. When a usable vulnerability is found, a program is written. This program is the actual jailbreak software and it is then distributed on the internet. Apple discourages jailbreaking, and actively works towards eliminating vulnerabilities that make jailbreaking possible on iOS. In addition to the OS updates and bug fixes, new iOS releases usually include patches to eliminate known vulnerabilities that allow jailbreaking. When iOS vulnerabilities are fixed by updates, it forces hackers to start over.
Note: The jailbreak process is completely reversible. To remove the jailbreak and bring the device back to its factory state, connect it to iTunes and perform a Restore.
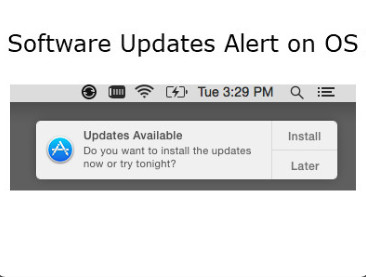
12.2.3.3 – Patching and Updating Operating Systems
Like the OS on a desktop or laptop, you can update or patch the OS on mobile devices. Updates add functionality or increase performance. Patches can fix security problems or issues with hardware and software.
Because there are so many different Android mobile devices, updates and patches are not released as one package for all devices. Sometimes a new version of Android cannot install on older devices where the hardware does not meet the minimum specifications. These devices might receive patches to fix known issues, but not receive OS upgrades.
Android updates and patches use an automated process for delivery. When a carrier or manufacturer has an update for a device, a notification on the device indicates that an update is ready, as shown in the figure. Touch the update to begin the download and installation process.
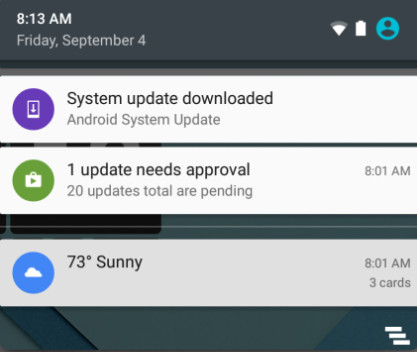
System Update Notification on Android
iOS updates also use an automated process for delivery, and devices that do not meet the hardware requirements are also excluded. To check for updates to iOS, connect the device to iTunes. A notice to download opens if updates are available. To manually check for updates, click the Check for Update button in the iTunes Summary pane.
There are two other types of updates for mobile device radio firmware that are important. These are called baseband updates and consist of the Preferred Roaming List (PRL) and the Primary Rate ISDN (PRI). The PRL is configuration information that a cellular phone needs to communicate on networks other than its own so that a call can be made outside of the carrier’s network. The PRI configures the data rates between the device and the cell tower. This ensures that the device is able to communicate with the tower at the correct rate.
12.2.3.4 – Check Your Understanding – Mobile Security Features
12.2.3.4 – Check Your Understanding – Mobile Security Features
12.3 – Linux and macOS Operating Systems
12.3.1 – Linux and macOS tools and features
12.3.1.1 – Introduction to Linux and macOS Operating Systems
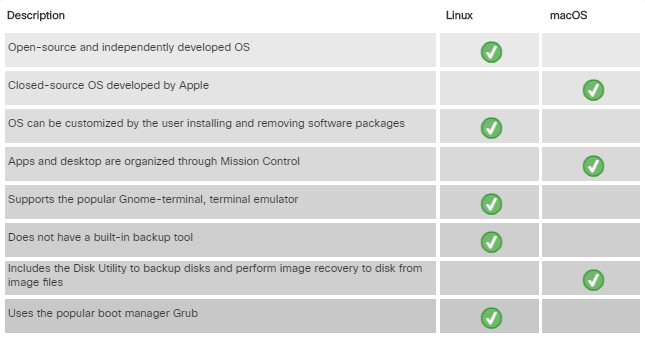
Two file systems used on most Linux operating systems are ext3, which is a 64-bit file system with support for journaling, and ext4, which delivers significantly better performance than ext3. Linux can also support FAT and FAT32. In addition, Network File System (NFS), can be used to mount remote storage devices into the local file system.
Most installations of Linux also support creation of a swap partition to use as swap space. The swap partition is used by the operating system to supplement system RAM. If applications or data files use up all the available space in RAM, data is written to the swap space on a disk and is treated as if it were stored in RAM.
Apple Mac workstations have their own file system, Extended Hierarchical File System (HFS Plus). This file system supports many of the same features as NTFS in Windows, but not native file/folder encryption. In macOS High Sierra and later, HFS Plus updated to the Apple File System (APFS), which does support native file encryption. HFS Plus has a maximum volume and file size of 8 ExaBytes.

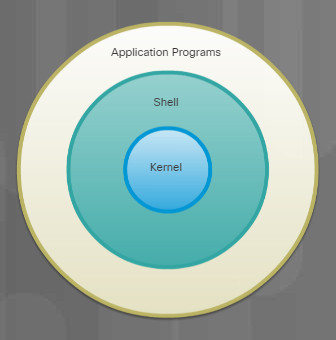
Unix is a proprietary operating system written in the C programming language. macOS and iOS are based upon the Berkley Standard Distribution (BSD) version of Unix.
GNU-Linux is an open-source, independently developed operating system which is compatible with Unix commands. Android, and many OS distributions rely upon the Linux kernel.

Linux operating systems are used in embedded-systems, wearable devices, smartwatches, cellphones, netbooks, PCs, servers and super computers. There are many different distributions (or distros) of Linux, including SUSE®, Red Hat®, CentOS®, Fedora®, Debian®, Ubuntu®, and Mint®. Each distro adds specific packages and interfaces to the generic Linux kernel and provides different support options. Most distributions provide a GUI interface.
Most distributions are a complete Linux implementation that includes the kernel, shell, applications, and utilities. Each Linux distro software vendor packages and distributes installation media and provides support.
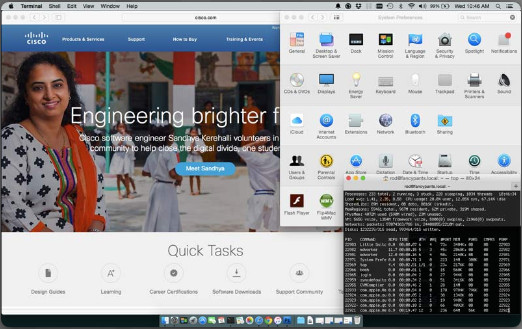
The operating system for Macintosh computers, macOS, is developed from the UNIX kernel, it is however, a closed source operating system.
Since its release in 2001, macOS has undergone regular updates and revision to keep pace with Apple Mac hardware updates. Updates and new OS versions are distributed for free through the App Store. Some older Mac computers may not be able to run the newest macOS versions. You can check support.apple.com/specs for the technical specifications of any macOS release.
macOS supports remote network installation similar to Preboot eXecution Environment (PXE) called NetBoot.
12.3.1.2 – Overview of Linux GUI
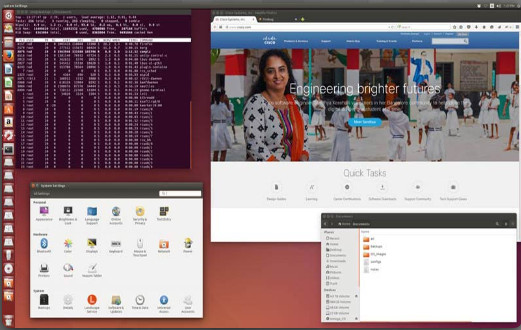
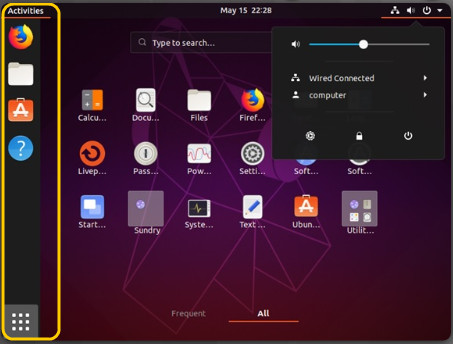
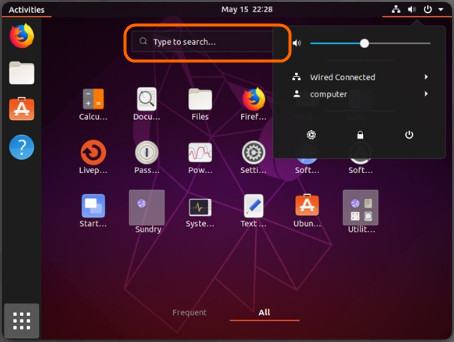
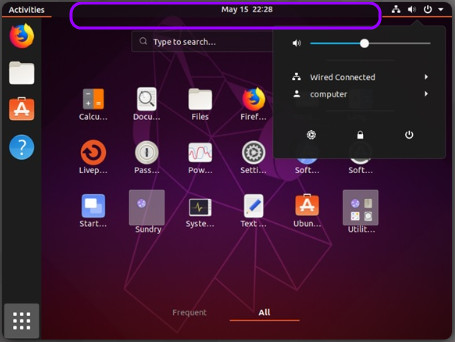
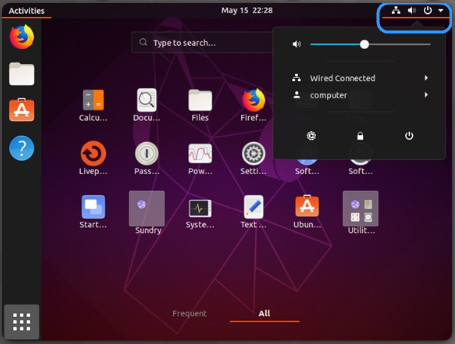
Different Linux distributions ship with different software packages, but users decide what stays in their system by installing or removing packages. The graphical interface in Linux is comprised of a number of subsystems that can also be removed or replaced by the user. While the details about these subsystems and their interactions are beyond the scope of this course, it is important to know the Linux GUI as whole can be easily replaced by the user. Because there are so many Linux distributions, this chapter focuses on Ubuntu when covering Linux.
Ubuntu Linux uses Unity as its default GUI. The figure shows a breakdown of the main components of Ubuntu Unity Desktop. Another feature in the Linux GUI is the ability to have multiple desktops or workspaces. This allows the users to arrange the windows on a particular workspace.
Canonical has a website that simulates Unity’s UI and also provides a tour through the Unity’s main features. To experience Unity via Canonical’s website visit http://tour.ubuntu.com/en.
12.3.1.3 – Overview macOS GUI
12.3.1.4 – Overview of Linux and macOS CLI
12.3.1.5 – Linux Backup and Recovery
The process of backing up data refers to creating a copy (or multiple copies) of data for safekeeping. When the backing up process is complete, the copy is called a backup. The primary goal is the ability to restore or recover the data in case of failure. Gaining access to an earlier version of the data is often seen as a secondary goal of the backing up process.
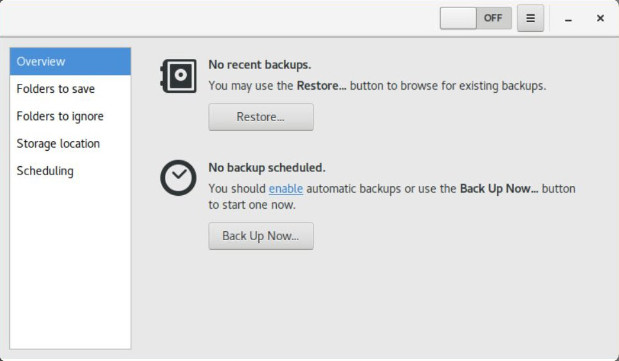
Linux Backup and Recovery
While backups can be achieved with a simple copy command, many tools and techniques exist to make the process automatic and transparent to the user.
Linux does not have a built-in backup tool. However, there are many commercial and open source backup solutions for Linux such as Amanda, Bacula, Fwbackups, and Déjà Dup. Déjà Dup is an easy and efficient tool for backing up data. Déjà Dup supports a number of features including local, remote, or cloud backup locations, data encryption compression, incremental backs up, periodic scheduled backups, and GNOME desktop integration. It also restores from any particular backup.
12.3.1.6 – macOS Backup and Recovery
macOS includes a backup tool called Time Machine. With Time Machine, users choose an external drive to be used as a backup destination device and connect it to the Mac via USB, FireWire or Thunderbolt. Time Machine will prepare the disk to receive backups and, when the disk is ready, it performs incremental backups periodically.
If the user has not specified a Time Machine destination disk, Time Machine will ask if the newly connected external disk should be used as the destination backup disk. Time Machine stores some backups on your Mac, so if the Time Machine backup disk is not available, you may be able to restore a backup directly from your Mac. This type of back up is called a local snapshot.
To enable Time Machine, go to System Preferences > Time Machine, slide the switch On and select the disk where the backups are stored, as shown in the figure. Clicking the Options button allows the user to select or unselect the files, folders, or drives to backup. By default, Time Machine performs hourly backups for the past 24 hours, daily backups for a month, and weekly backups for all previous months. When the destination backup drive becomes full, Time Machine removes the oldest backup files to free up space.

macOS Backup and Recovery
To restore data from Time Machine, make sure the destination backup disk is connected to the Mac and click Enter Time Machine in the Time Machine menu. A timeline on the right-hand side of the screen will show the available backups. Time Machine allows the user to restore the data to any previous version currently available in the destination backup disk.
12.3.1.7 – Overview of Disk Utilities

Overview of Disk Utilities
To help diagnose and solve disk-related problems, most modern operating systems include disk utility tools. Ubuntu Linux includes a disk utility called Disks. With Disks users can perform the most common disk-related tasks including partition management, mount or unmount, format disks and query Analysis and Reporting Technology, (S.M.A.R.T.). macOS includes Disk Utility. In addition to supporting the main disk maintenance tasks, Disk Utility also supports Verify Disk Permissions and Repair Disk Permissions. Repair Disk Permission is a common troubleshooting step in macOS. Disk Utility can also be used to backup disks to image files and perform an image recovery to disk from image files. These files contain the entire contents of a disk.
Below are a few common maintenance tasks that can be performed using disk utility software:
- Partition management – When working with computer disks, partitions may need to be created, deleted or resized.
- Mount or Unmount disk partitions – On Unix-like systems, mounting a partition relates to the process of binding a partition of a disk or a disk image file (usually a .iso) to a folder location.
- Disk Format – Before a partition can be used by the user or the system, it must be formatted.
- Bad Sector Check – When a disk sector is flagged as bad, it becomes harmless to the OS because it will no longer be used to store data. Many bad sectors could be an indicator of a failing disk. Disk utilities can salvage data stored in bad sectors by moving it to healthy disk sectors.
- Query S.M.A.R.T. attributes – S.M.A.R.T. can detect and report attributes about a disk’s health. The goal of S.M.A.R.T. is to anticipate disk failure, allowing the user to move the data to a healthy disk before the failing disk becomes inaccessible.
12.3.1.8 – Check your understanding – Linux and macOS Operating Systems
12.3.1.8 – Check your understanding – Linux and macOS Operating Systems
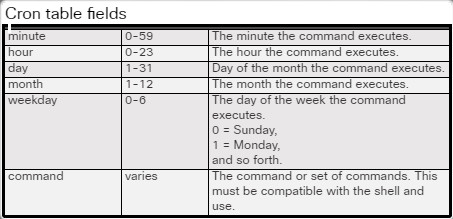
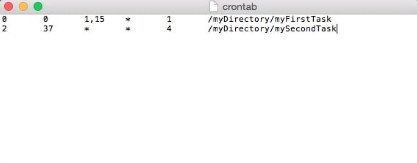
12.3.2.1 – Scheduled Tasks
12.3.2.2 – Operating System Updates
12.3.2.3 – Security
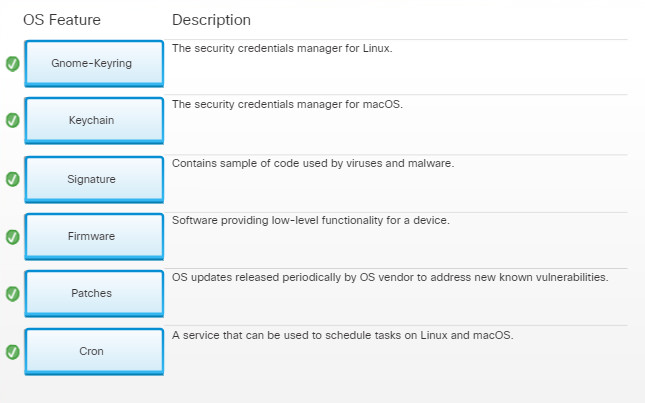
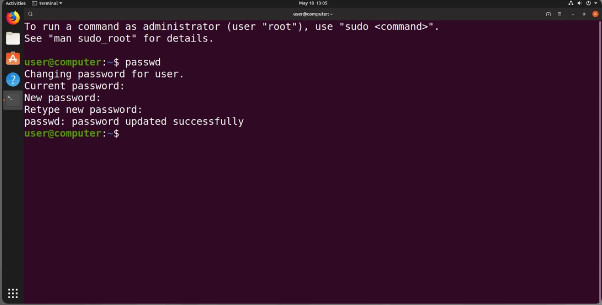
Usernames, passwords, digital certificates, and encryption keys are just a few of the security credentials associated to a user. Due to the increasing number of necessary security credentials, modern operating systems include a service to manage them. Applications and other services can then request and utilize the credentials stored by the security credentials manager service.

Gnome-keyring is a security credentials manager for Ubuntu Linux. To access Gnome-Keyring on Ubuntu Linux use the following path:
Click Dash > Search for Key > Click Passwords and Keys
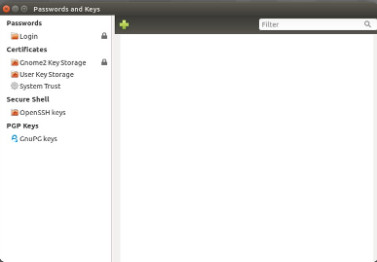
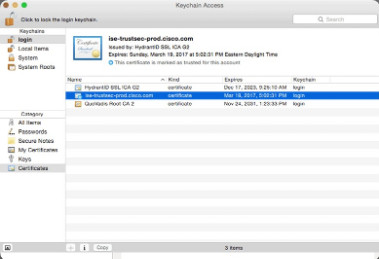
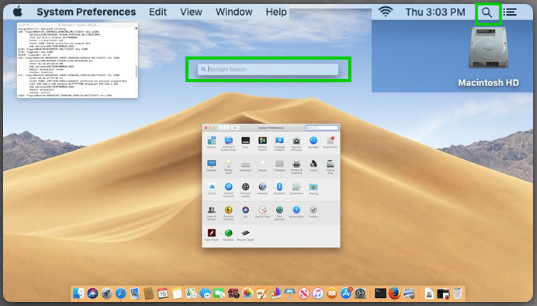
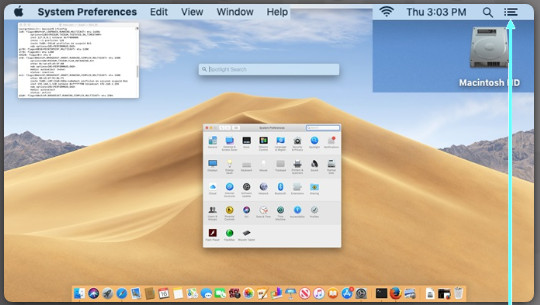
Keychain is a security credentials manager for macOS. To access Keychain on macOS, as shown, use the following path:
Applications > Utilities > Keychain Access
12.3.2.4 – Check Your Understanding – Linux and macOS Best Practices
12.3.2.4 – Check Your Understanding – Linux and macOS Best Practices
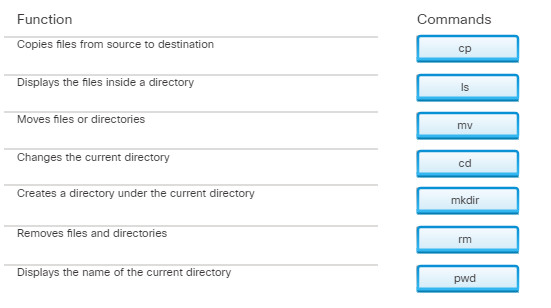
12.3.3 – Basic CLI Commands
12.3.3.1 – Syntax Checker – File and Directory Commands
12.3.3.2 – Check Your Understanding – File and Directory commands
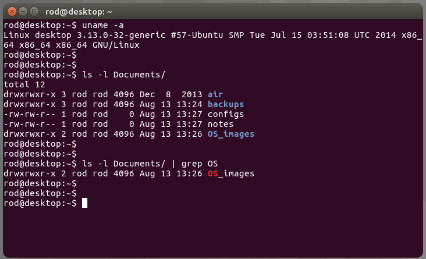
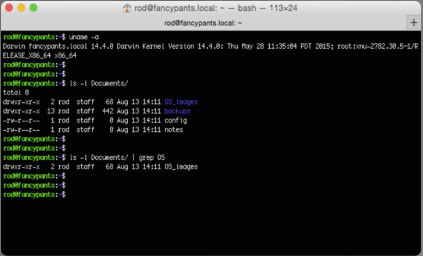
12.3.3.3 – The ls -l command output
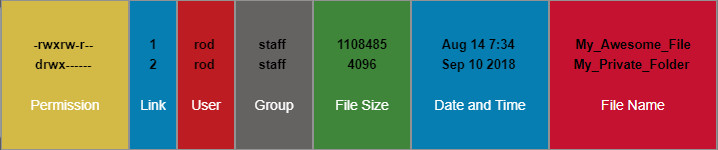
The ls -l command output
12.3.3.4 – Basic Unix File and Directory Permissions
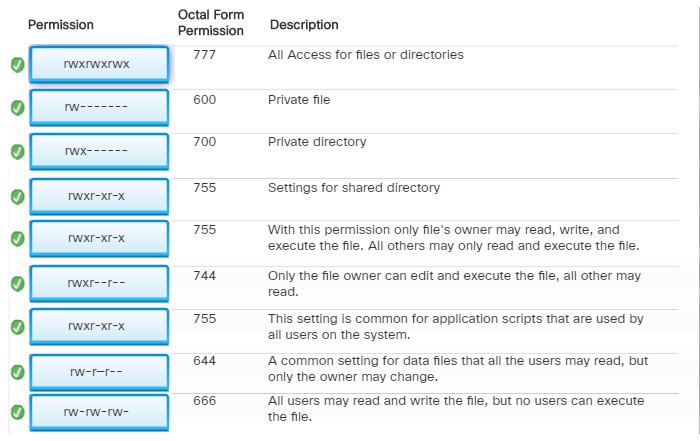
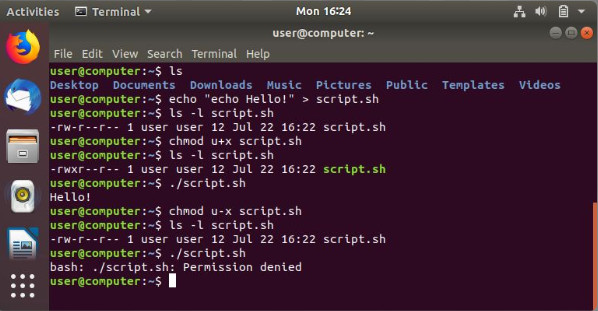
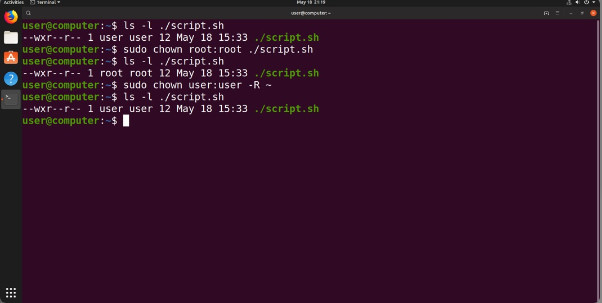
To organize the system and reinforce boundaries within the system, Unix uses file permissions. File permissions are built into the file system structure and provide a mechanism to define permissions to every file and directory. Every file and directory on Unix systems carries its permissions which define the actions that the owner, the group, and others can do with the file or directory.
The only user who can override file permissions in Unix is the root user. Having the power to override file permissions, the root user can write to any file. Because everything is treated as a file, the root user has full control over the Unix operating system. Root access is often required before performing maintenance and administrative tasks.
Note: Because Linux and OS X are based on Unix, both operating systems are in full compliance with Unix file permissions.
Review the different permission values shown in the Figure 1. Note the differences of how the file and directory access is affected by the permissions. Figure 2 is a summary of the permissions.
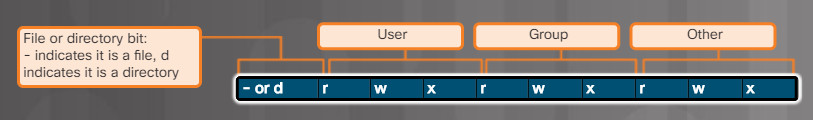
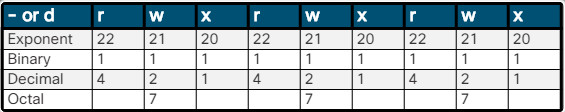
Basic Unix File and Directory Permissions
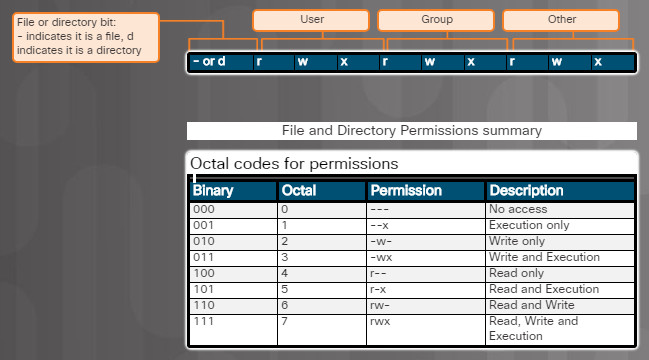
Basic Unix File and Directory Permissions Summary
12.3.3.5 – Syntax Checker: File and Directory Permissions
12.3.3.6 – Check Your Understanding – File and Directory Permission
12.3.3.6 – Check Your Understanding – File and Directory Permission
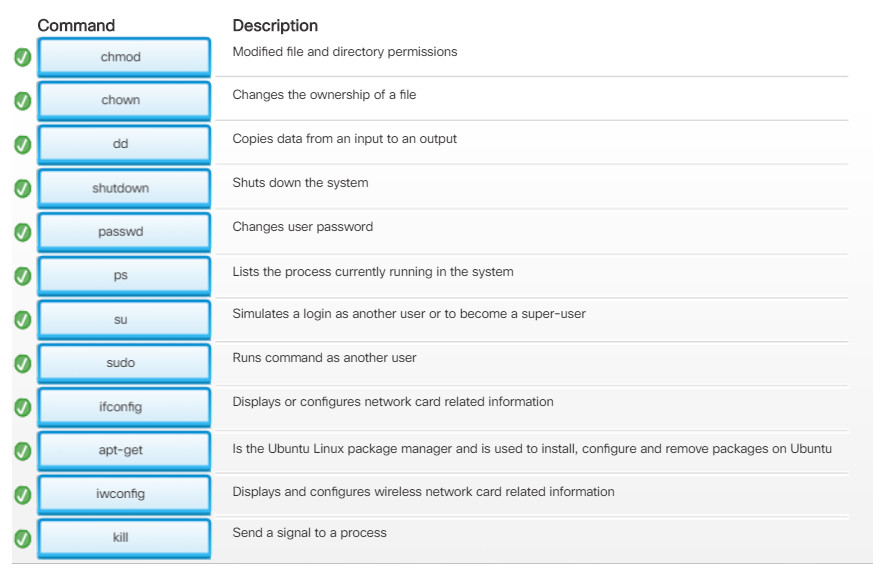
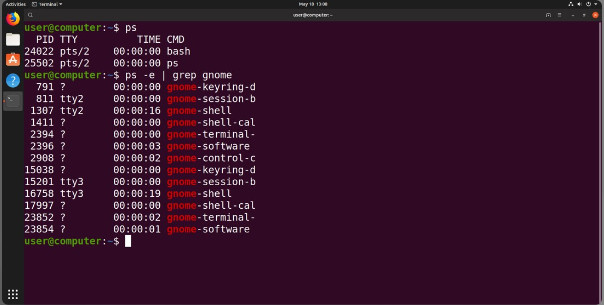
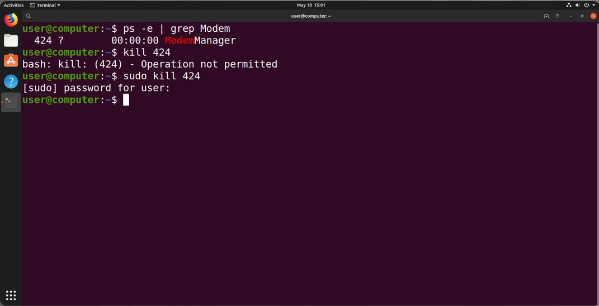
12.3.3.7 – Linux Administrative Commands
12.3.3.8 – Linux Administrative Commands Requiring Root Access
12.3.3.9 – Check Your Understanding: -Administrative Commands
12.3.3.9 – Check Your Understanding: -Administrative Commands
12.3.3.10 – Syntax Checker – File Ownership and Permission
12.4 – Basic Troubleshooting Process for Mobile, Linux, and…
12.4.1 – Applying the Troubleshooting Process to Mobile, Linux,…
12.4.1.1 – The Six Steps of the Troubleshooting Process
12.4.1.1 – The Six Steps of the Troubleshooting Process
12.4.1.2 – Identify the Problem
When troubleshooting problems with mobile devices, find out if the device is under warranty. If it is, it can often be returned for repair or an exchange. If the device is no longer under warranty, determine if a repair is cost-effective. To determine the best course of action, compare the cost of the repair with the replacement cost of the mobile device. Because many mobile devices change rapidly in design and functionality, they are often more expensive to repair than to replace. For this reason, mobile devices are usually replaced.
Mobile device problems can result from a combination of hardware, software, and network issues. Mobile technicians must be able to analyze the problem and determine the cause of the error to repair the mobile device. This process is called troubleshooting.
The first step in the troubleshooting process is to identify the problem. The figure shows a list of open-ended and closed-ended questions to ask the customer for mobile device operating systems and on Linux and macOS.
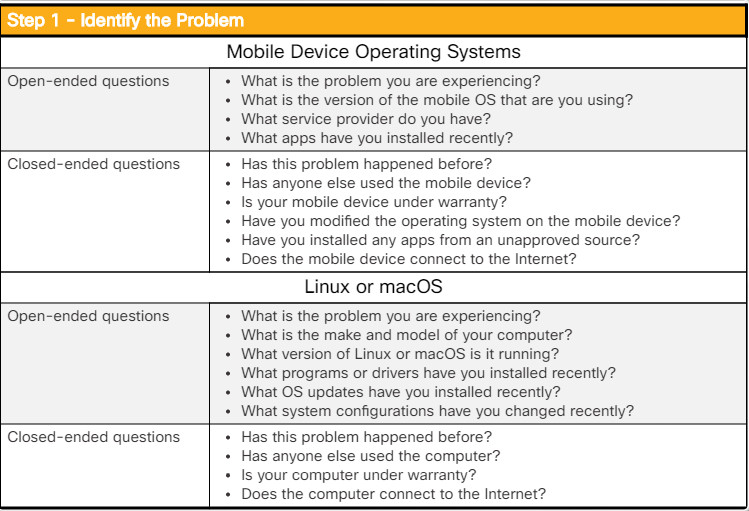
Identify the Problem
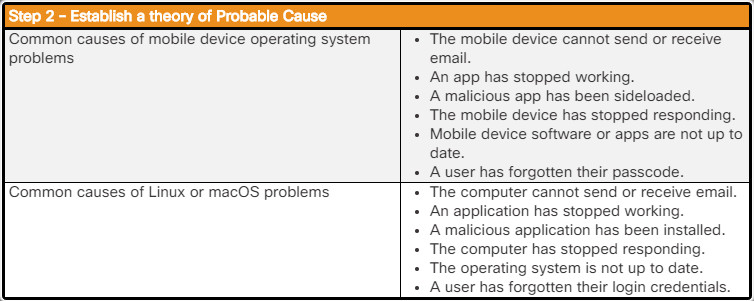
12.4.1.3 – Establish a theory of Probable Cause
After you have talked to the customer, you can establish a theory of probable causes. The figure shows a list of some common probable causes for mobile device operating systems, Linux, and macOS problems.
12.4.1.4 – Test the Theory to Determine the Cause
After you have developed some theories about what is wrong, test your theories to determine the cause of the problem. Once the theory is confirmed, you then determine the steps to resolve the problem. The figure shows a list of quick procedures that can determine the exact cause of the problem or even correct the problem. If a quick procedure corrects the problem, you can then verify full system functionality. If a quick procedure does not correct the problem, you might need to research the problem further to establish the exact cause.
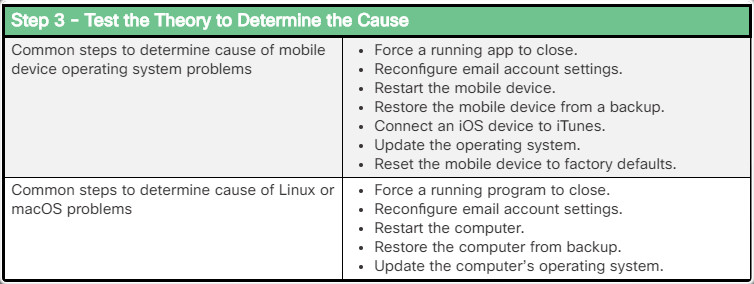
Test the Theory to Determine the Cause
12.4.1.5 – Establish a Plan of Action to Resolve the Problem and…
After you have determined the exact cause of the problem, establish a plan of action to resolve the problem and implement the solution. The figure shows some sources you can use to gather additional information to resolve an issue.
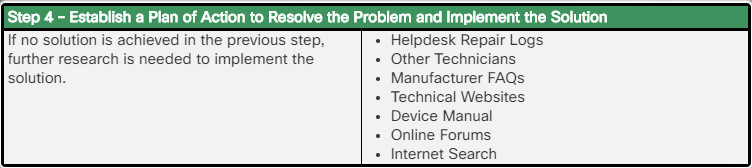
Establish a Plan of Action to Resolve the Problem and Implement the Solution
12.4.1.6 – Verify Full System Functionality and if Applicable,…
After you have corrected the problem, verify full functionality and, if applicable, implement preventive measures. The figure shows a list of the steps to verify the solution
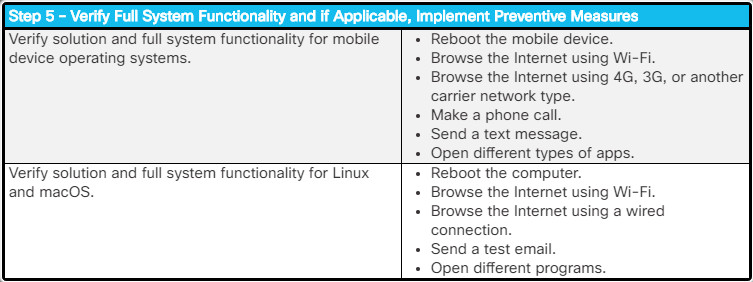
Verify Full System Functionality and if Applicable, Implement Preventive Measures
12.4.1.7 – Document Findings, Actions, and Outcomes.
In the final step of the troubleshooting process, you must document your findings, actions, and outcomes. The figure lists the tasks required to document the problem and the solution.
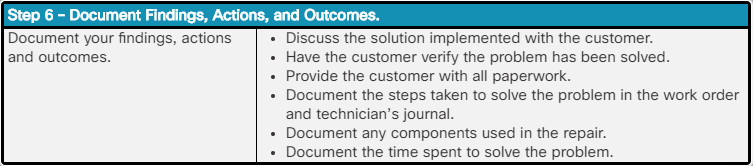
Document Findings, Actions, and Outcomes.
12.4.2.1 – Common Problems and Solutions for Mobile Operating…
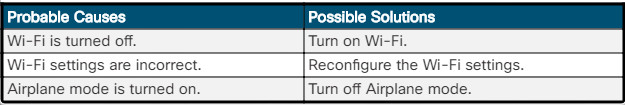
The mobile device will not connect to the internet.
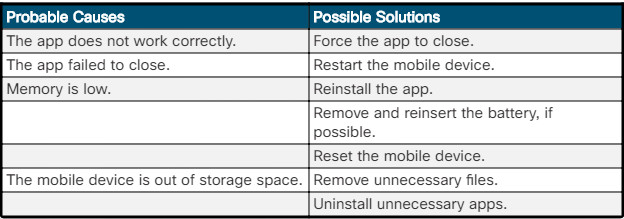
An app fails to respond.
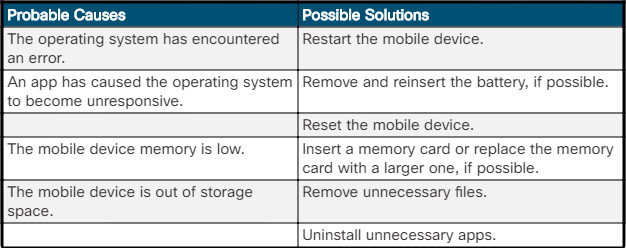
The mobile device fails to respond.
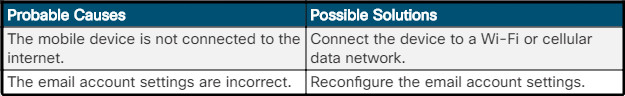
The mobile device cannot send or receive email.
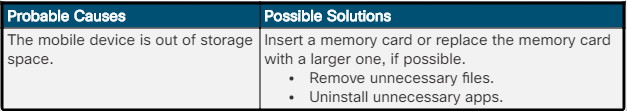
The mobile device cannot install additional apps or save photos.
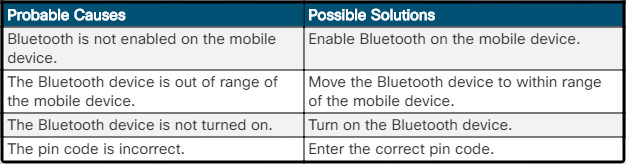
A mobile device cannot connect or pair with a Bluetooth device.
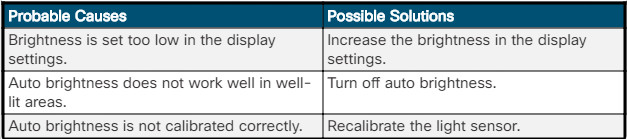
Mobile device display looks dim.
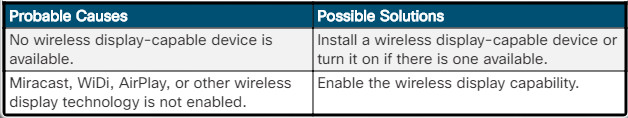
The mobile device cannot broadcast to an external monitor.
The mobile device is exhibiting slow performance.
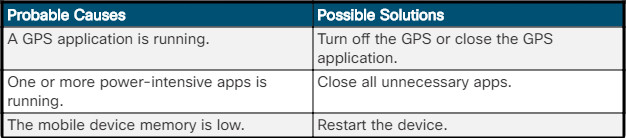
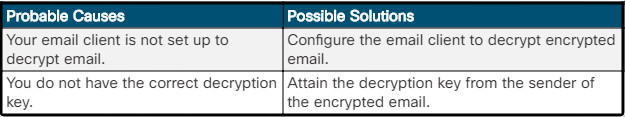
The mobile device is unable to decrypt email.
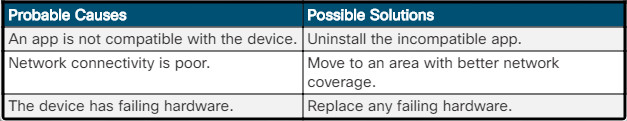
The mobile device operating system has frozen.
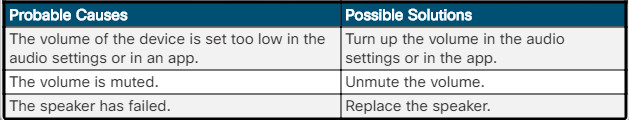
The mobile device has no sound coming from the speakers.
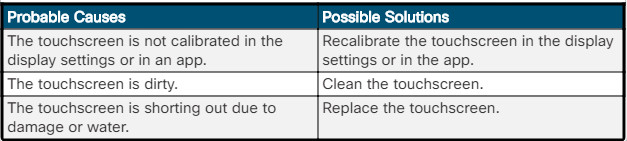
The mobile device touchscreen has inaccurate response.
12.4.2.2 – Common Problems and Solutions for Mobile OS Security
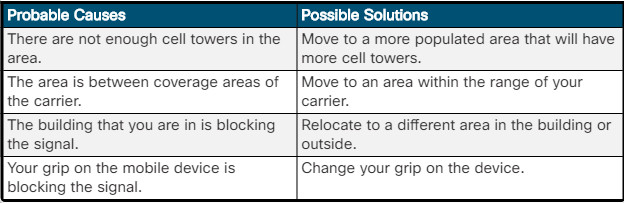
A mobile device has a weak signal or the signal has been dropped.
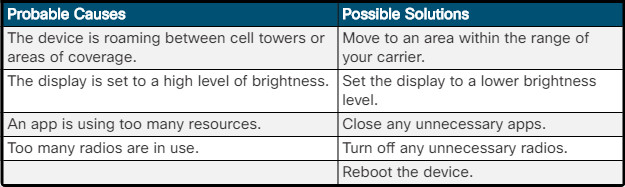
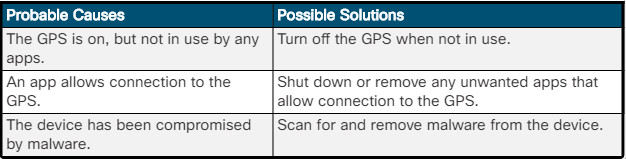
The power of a mobile device is draining more quickly than normal.
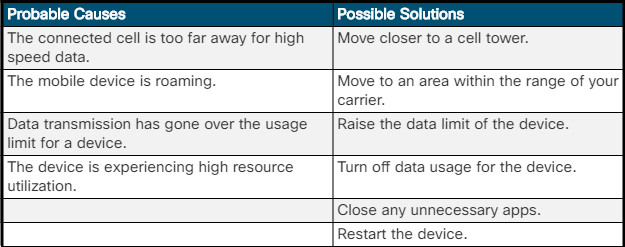
A mobile device has slow data speeds.
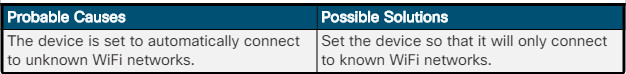
A mobile device connects to a WiFi network unintentionally.
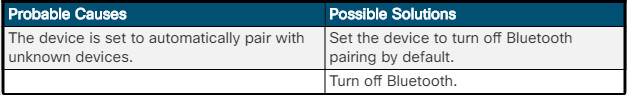
A mobile device pairs to a Bluetooth device unintentionally.
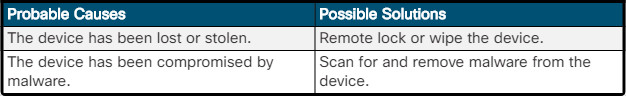
A mobile device has leaked personal files and data.
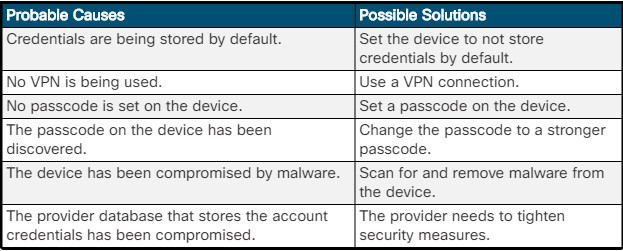
A mobile device account has been accessed by unauthorized personnel.
An app has achieved unauthorized access to root.
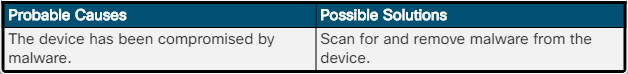
A mobile device is being tracked without permission.
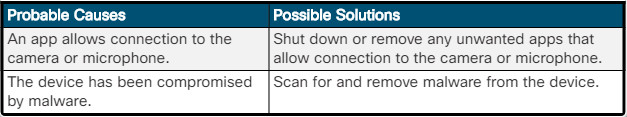
A mobile device camera or microphone is being accessed without permission.
12.4.2.3 – Common Problems and Solutions for Linux and macOS…
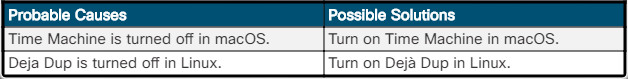
The automatic backup operation does not start.
The directory appears empty.
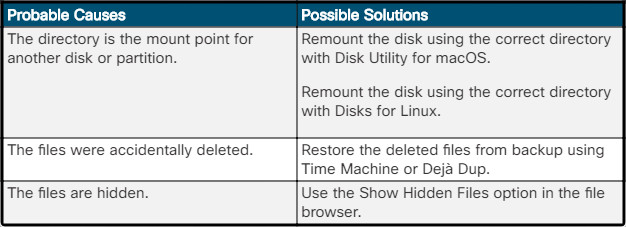
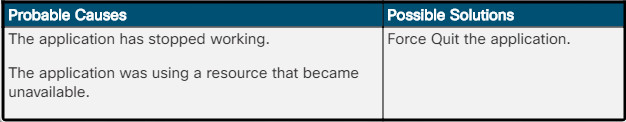
An application stops responding in macOS.
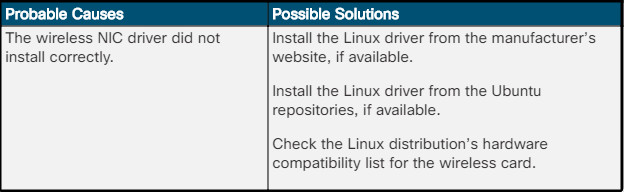
Wi-Fi is not accessible using Ubuntu.
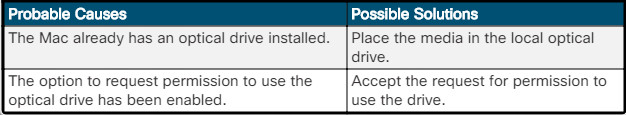
macOS cannot read the remote optical disc using Remote Disc.
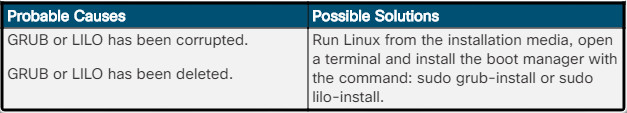
Linux fails to boot and you receive a “Missing GRUB” or “Missing LILO” message.
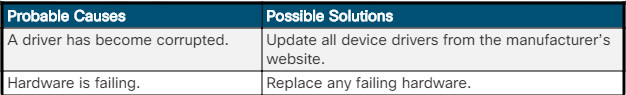
Linux or Mac OS freezes on startup and exhibits kernel panic where there is a stop screen.
12.4.2.4 – Lab – Troubleshoot Mobile Devices
In this lab, you will learn how to troubleshoot mobile devices.
12.4.2.4 – Lab – Troubleshoot Mobile Devices
12.5 – Summary
12.5.1 – Conclusion
12.5.1.1 – Chapter 12: Mobile, Linux, and macOS
In this chapter, you learned that, like desktops and laptops, mobile devices also use operating systems to interface with the hardware and to run software. The two most commonly used mobile operating systems are Android and iOS. You learned that Android is an open source operating system and is customizable while iOS is closed source and cannot be modified or redistributed without permission from Apple. Both platforms use apps to provide functionality. You worked with both the Android and iOS operating systems as part of lab exercises.
Mobile devices are easily lost or stolen, therefore as an IT professional, you need to be familiar with mobile security features such as screen locks, biometric authentication, remote lock and remote wipe, and patching and upgrading. You learned that mobile devices can be unlocked using facial recognition, fingerprints, passcodes, and swipe patterns. You also learned that mobile OSs can be configured to disable access if too many failed login attempts are made to prevent someone from trying to guess a passcode. Another measure of security is provided by remote lock and remote wipe for devices that have been lost or stolen. These features allow the device to be remotely wiped or locked to prevent data on the device from being compromised. You configured passcode locks on a mobile device in the lab.
You learned about the Linux and macOS operating systems and some of the differences between them. Linux supports ext3, ext4, FAT, and NFS file systems while macOS supports HFS and APFS. Also, macOS includes a backup tool called Time Machine while Linux does not have a built-in backup tool. Another major difference is the Linux GUI can be easily replaced by the user.
It is important to not only learn about other operating systems but to also build hands-on skills. In this chapter there was a lab to install Linux in a virtual machine and explore the GUI.
Finally, you learned the six steps in the troubleshooting process as they are applied to mobile, Linux, and macOS operating systems.









 a user’s home directory back to them.
a user’s home directory back to them.