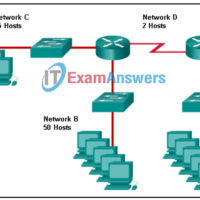
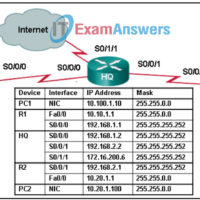
Final-Exam: Network Addressing and Basic Troubleshooting Final Exam Answers (Course Final Exam) 1. Match each item to the type of topology diagram on which it is typically identified. 2. Refer to the exhibit. The IP address of which device interface should be used as the default gateway setting …
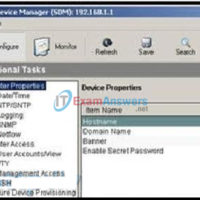
Checkpoint Exam: Cisco Devices and Troubleshooting Network Issues: Network Addressing and Basic Troubleshooting Module 7 – 8 Checkpoint Exam Answers (NABT) 1. After several configuration changes are made to a router, the copy running-configuration startup-configuration command is issued. Where will the changes be stored? NVRAM RAM flash ROM …
Checkpoint Exam: IP Addressing: Network Addressing and Basic Troubleshooting Module 4 – 6 Checkpoint Exam Answers 1. A network administrator is given the network prefix 10.25.0.0/16. What subnet prefix would provide the organization with 512 subnets, each capable of supporting at least 100 hosts? /25 /20 /28 /19 …
Checkpoint Exam: Physical, Data Link, and Network Layers: Network Addressing and Basic Troubleshooting Module 1 – 3 Checkpoint Exam Answers 1. A network specialist has been hired to install a network in a company that assembles airplane engines. Because of the nature of the business, the area is …
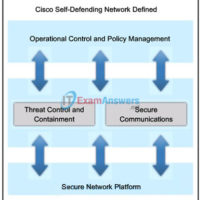
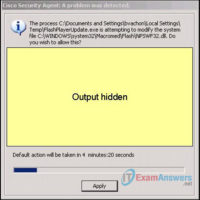
CCNA Security Final Exam Answers (CCNAS v1.2 and v1.1) 1. What will be disabled as a result of the no service password-recovery command ? aaa new-model global configuration command. change to the configuration register. password encryption service. ability to access ROMmon. 2. What occurs after RSA keys are …
CCNA Security Chapter 9 Exam Answers (CCNAS v1.2 and v1.1) 1. Which three statements describe ethics in network security? (Choose three.) principles put into action in place of laws foundations for current laws set of moral principles that govern civil behavior standard that is higher than the law …
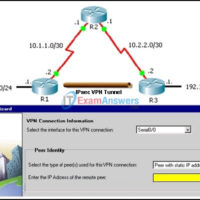
CCNA Security Chapter 8 Exam Answers (CCNAS v1.2 and v1.1) 1. What are two benefits of an SSL VPN? (Choose two.) It supports all client/server applications. It supports the same level of cryptographic security as an IPsec VPN. It has the option of only requiring an SSL-enabled web …
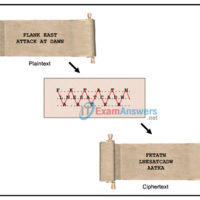
CCNA Security Chapter 7 Exam Answers (CCNAS v1.2 and v1.1) 1. Which symmetrical encryption algorithm is the most difficult to crack? 3DES AES DES RSA SHA 2. What is the basic method used by 3DES to encrypt plaintext? The data is encrypted three times with three different keys. …
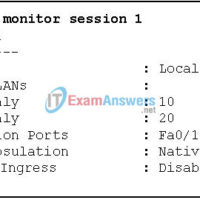
CCNA Security Chapter 6 Exam Answers (CCNAS v1.2 and v1.1) 1. Which two measures are recommended to mitigate VLAN hopping attacks? (Choose two.) Use a dedicated native VLAN for all trunk ports. Place all unused ports in a separate guest VLAN. Disable trunk negotiation on all ports connecting …
CCNA Security Chapter 5 Exam Answers (CCNAS v1.2 and v1.1) 1. An IPS sensor has detected the string confidential across multiple packets in a TCP session. Which type of signature trigger and signature type does this describe? Trigger: Anomaly-based detection Type: Atomic signature Trigger: Anomaly-based detection Type: Composite …